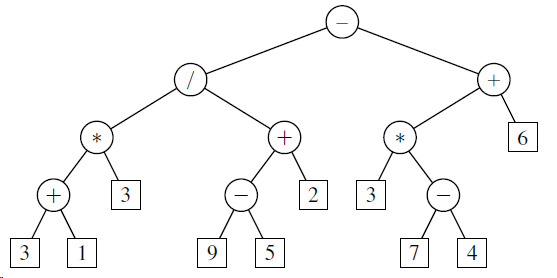
In what order are positions visited during a preorder traversal of the tree of Figure 8.6? +
Question:
In what order are positions visited during a preorder traversal of the tree of Figure 8.6?
Transcribed Image Text:
+ + 3 2 9 5 7 4 3.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 62% (8 reviews)
In preorder traversal the root no...View the full answer

Answered By

Ajay Negi
Hi, I've completed my degree in engineering (Information Technology) from an NIT. Currently working as a software engineer. Wish to impart quality education to the future generation.
5.00+
2+ Reviews
10+ Question Solved
Related Book For 

Data Structures and Algorithms in Java
ISBN: 978-1118771334
6th edition
Authors: Michael T. Goodrich, Roberto Tamassia, Michael H. Goldwasser
Question Posted:
Students also viewed these Computer science questions
-
In what order are positions visited during a postorder traversal of the tree of Figure 8.6? 3 3 5 4
-
Let the rank of a position p during a traversal be defined such that the first element visited has rank 1, the second element visited has rank 2, and so on. For each position p in a tree T, let...
-
We can define a binary tree representation T² for an ordered general tree T as follows (see Figure 8.21): ¢ For each position p of T, there is an associated position p² of T²....
-
A beam of light enters the end of an optic fiber as shown in Fig. 23-52. Show that we can guarantee total internal reflection at the side surface of the material (at point a), if the index of...
-
Bob Smith incorporated Smith Inc. 20 years ago and owns all of the shares himself. Smith Inc. is a "small business corporation" which carries on an active business in Victoria, B.C. Thirteen years...
-
An investment analyst wishes to explain his clients' rates of return on their portfolios using two variables measuring returns from stocks and three from bond mutuals. The results of an unrestricted...
-
When the plaintiff was 16, he was employed by Kmart as a cashier. At the end of his training, he was required to read Kmarts policy agreement, which included an agreement to submit all employment...
-
The following audit procedures were planned by Linda King, CPA, in the audit of the acquisition and payment cycle for Cooley Products, Inc.: 1. Review the acquisitions journal for large and unusual...
-
help me respond to this, Can I request a little insight on this zoom meetings attendees and the intended end result? Will this information conclusion be going back to the County auditors in a report?...
-
On 1st September 2021, HA was waiting for a friend next to a bus stop in Yewsbridge. The road by the bus stop is narrow and there have been accidents on that road before where pedestrians on the...
-
Draw the binary tree representation of the following arithmetic expression: (((5+2) (21))/((2+9)+((72)1)) 8).
-
Give the output of the method parenthesize(T, T.root( )), as described in Code Fragment 8.26, when T is the tree of Figure 8.6. Fragment 8.26 Figure 8.6 3 3 5 4
-
Beta decay is caused by the weak force, as are all reactions in which strangeness changes. Does this imply that the weak force can change quark flavor? Explain.
-
5. Can you incorporate open-source code from a GitHub forum into an Infosys proprietary tool? Oa. Yes, since it is freely available, it is assumed safe for use in proprietary tools. Ob. No, Infosys...
-
Misinformation refers to intentionally stating or circulating inaccurate information, on the other hand while Disinformation refers to something that is not true. O True False
-
define interviews research strategy in line with interpretivism research philosophyand indicate the reasoning for its use in supply chain management challenges and add source fo this.
-
A Which is the best way to meet stakeholders' expectations? A O Host team building sessions with stakeholders. B C D O Keep stakeholders regularly informed throughout the project. Hold weekly status...
-
The transactions demand for holding money is when people hold money: To transact purchases they expect to make. As insurance against unexpected expenses. Instead of near money. To speculate in the...
-
Terry transferred $500,000 of real estate into an irrevocable trust for her son, Lee. The trustee was directed to retain income until Lee's 21st birthday and then pay him the corpus of the trust....
-
Trade credit from suppliers is a very costly source of funds when discounts are lost. Explain why many firms rely on this source of funds to finance their temporary working capital.
-
In the analog hierarchy of Figure 6.9, find the overhead (extra bandwidth for guard band or control) in each hierarchy level (group, supergroup, master group, and jumbo group). Figure 6.9 48 kHz 12...
-
Which of the three multiplexing techniques is (are) used to combine analog signals? Which of the three multiplexing techniques is (are) used to combine digital signals?
-
We need to transmit 100 digitized voice channels using a passband channel of 20 KHz. What should be the ratio of bits/Hz if we use no guard band?
-
Develop a SWOT analysis of Coles potential business. b. Can Cole be profitable and if so, in what period of time? c. What are the major business assumptions that require verification? d. Does Cole,...
-
The current temperature is 12 oC and the dew point is -29 oC. What is the relative humidity in percentage? Answer to one decimal place. The current temperature is 12 oC and the dew point is -29 oC....
-
The density of the block depends on what material the block is made out of. The table below shows the average densities for 3 different kinds of Earth materials. Using these data, calculate the...

Study smarter with the SolutionInn App