Consider the modification of the STS KAS that is presented as Protocol 3. In this modification of
Question:
Consider the modification of the STS KAS that is presented as Protocol 3. In this modification of the protocol, the signatures omit the intended receiver. Show how this renders the protocol insecure, by describing a man-in-the-middle attack. Discuss the consequences of this attack, in terms of how they are violated. (This attack is known as an unknown key-share attack.) (Hint: suppose the adversary Eve can register the public key of any party as its own.)
Modified station-to-station KAS.
The public domain parameters consist of a group (G;), and element ? ? G having order n.
1. U chooses a random number a U , 0? a U ? n ? 1. Then she computes b U = a aU and she sends Cert (U) and b U to V.
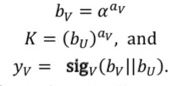
2. V chooses a random number a V , 0? a V ? n ? 1. Then she computes
Then V sends Cert(V), b U , and y V to U.
3. U verifies y v using ver v . If the signature y V is not valid, then she ?rejects? and quits. Otherwise, she ?accepts,? she computes
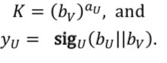
And she sends y U to V.
4. V verifies y U using ver U . If the signature y U is not valid, then he ?rejects?; otherwise, he ?accepts.?

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross




