Alice and Bob are both users on a Unix system, and Alice wants to share some...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
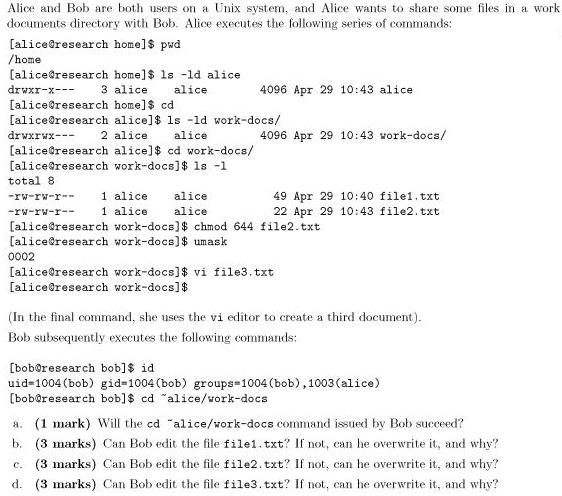
Alice and Bob are both users on a Unix system, and Alice wants to share some files in a work documents directory with Bob. Alice executes the following series of commands: [alice@research home]$ pwd /home [alice@research home]$ ls -ld alice 3 alice [alice@research home]$ cd [alice@research alice]$ ls -ld work-docs/ drwxr-x--- alice 4096 Apr 29 10:43 alice drwxrwx--- 2 alice alice 4096 Apr 29 10:43 vork-docs/ [alice@research alice)$ cd work-docs/ [alice@research work-docs]$ 1s -1 total 8 1 alice 1 alice -rw-rw-r- alice 49 Apr 29 10: 40 file1. txt 22 Apr 29 10:43 file2. txt -rw-rw-r-- alice [alice@research work-docs]$ chmod 644 file2.txt [alice@research work-docs]$ umask 0002 [alice@research work-docs]$ vi file3. txt [alice@research work-docs]$ (In the final command, she uses the vi editor to create a third document). Bob subsequently executes the following commands: [boboresearch bob]$ id uid-1004 (bob) gid=1004 (bob) groups-1004 (bob),1003 (alice) [bob@research bob]$ cd "alice/vork-docs a. (1 mark) Will the ed "alice/work-docs command issued by Bob succeed? b. (3 marks) Can Bob edit the file file1.txt? If not, can he overwrite it, and why? c. (3 marks) Can Bob edit the file file2.txt? If not, can he overwrite it, and why? d. (3 marks) Can Bob edit the file file3. txt? If not, can he overwrite it, and why? Alice and Bob are both users on a Unix system, and Alice wants to share some files in a work documents directory with Bob. Alice executes the following series of commands: [alice@research home]$ pwd /home [alice@research home]$ ls -ld alice 3 alice [alice@research home]$ cd [alice@research alice]$ ls -ld work-docs/ drwxr-x--- alice 4096 Apr 29 10:43 alice drwxrwx--- 2 alice alice 4096 Apr 29 10:43 vork-docs/ [alice@research alice)$ cd work-docs/ [alice@research work-docs]$ 1s -1 total 8 1 alice 1 alice -rw-rw-r- alice 49 Apr 29 10: 40 file1. txt 22 Apr 29 10:43 file2. txt -rw-rw-r-- alice [alice@research work-docs]$ chmod 644 file2.txt [alice@research work-docs]$ umask 0002 [alice@research work-docs]$ vi file3. txt [alice@research work-docs]$ (In the final command, she uses the vi editor to create a third document). Bob subsequently executes the following commands: [boboresearch bob]$ id uid-1004 (bob) gid=1004 (bob) groups-1004 (bob),1003 (alice) [bob@research bob]$ cd "alice/vork-docs a. (1 mark) Will the ed "alice/work-docs command issued by Bob succeed? b. (3 marks) Can Bob edit the file file1.txt? If not, can he overwrite it, and why? c. (3 marks) Can Bob edit the file file2.txt? If not, can he overwrite it, and why? d. (3 marks) Can Bob edit the file file3. txt? If not, can he overwrite it, and why?
Expert Answer:

Related Book For 

Fundamental financial accounting concepts
ISBN: 978-0078025365
8th edition
Authors: Thomas P. Edmonds, Frances M. Mcnair, Philip R. Olds, Edward
Posted Date:
Students also viewed these mathematics questions
-
The Party Store had the following series of transactions for 2013: Required a. Determine the quantity and dollar amount of inventory at the end of the year, assuming The Party Store uses the FIFO...
-
Alice and Bob are experimenting with CSMA using a W 2 Walsh table (see Figure 12.29). Alice uses the code [+1, +1] and Bob uses the code [+1, 1]. Assume that they simultaneously send a hexadecimal...
-
Alice and Bob are playing a game where they take turns drawing on a piece of paper. Alice goes first and Bob goes second. The rules of the game are as follows: We start off with n crosses, i.e....
-
Addie's grandfather has left them a trust and the value of the money they receive depends on the age choose to collect this gift of money. Their options are given in the table below. Payoff at age 19...
-
On the dust jacket of his 2007 book Cult of the Amateur, Andrew Keen writes: Our most valued cultural institutions our professional newspapers, magazines, music, and movies are being overtaken by...
-
On November 1, 2013, Quantum Technology, a geothermal energy supplier, borrowed $16 million cash to fund a geological survey. The loan was made by Nevada BancCorp under a noncommitted short-term line...
-
A U.S. Treasury bond pays a 7% coupon on January 7 and July 7. How much interest accrues per \($100\) of principal to the bond holder between July 7, 2013, and August 9, 2013? How would your answer...
-
Callie Peters is completing the audit of MakingNewFriends.com for the year ended December 31, 2013. Callie has been the audit manager on this engagement for the past three years. MakingNewFriends.com...
-
3 Hadley has of a box of white envelopes and of a box of gray envelopes. When full, each box of envelopes has the same number of envelopes. Hadley said she has of a box when she puts the white...
-
You work in the human resources department of your company helping new employees fill out the necessary paperwork to get their first paycheck. There are a number of decisions that employees must make...
-
An investor buys 5 books for $100 and plans to sell them all within the next 5 years. At the end of year 1, he sells 1 for $140, at the end of year 2 he sells another for $130, and at the end of year...
-
What is your "theory of change"? What are your assumptions about how social change might occur (for example, spiritually or secularly? Through individual actions or large group events? Single issue...
-
What is the nature and scope of the alcohol and/or drug abuse problem in the United States today on year 2022? For example, is this problem more significant today than it was in the past? What are...
-
Describe some front office strategies for communicating with guests, others in the front office and other hotel areas for each of these five requests. Identify five typical service requests that...
-
Discuss how video games either socially isolate us or allow us a means of interaction with others. If you choose isolation, discuss what the solution would be to reengage with us socially. If you...
-
What are the ramifications of biased media coverage? 2. What is nationalism, and how is it evident in the sport media? 3. Identify five athlete-activists and pioneers and their contributions to sport...
-
14) Kerberos relies exclusively on A. symmetric encryption C. private key encryption B. asymmetric encryption D. public key encryption
-
Don Griffin worked as an accountant at a local accounting firm for five years after graduating from university. Recently, he opened his own accounting practice, which he operates as a corporation....
-
At the end of the accounting period, Adams Companys general ledger contained the following adjusted balances: Required 1. Set up the preceding spreadsheet format. (The spreadsheet tips for ATC 3-9...
-
Business Applications Case Understanding real-world annual reports Required Use the Target Corporations annual report in Appendix B to answer the following questions. a. For the year ended January...
-
Barker Company had the following balances in its accounting records as of December 31, 2012: The following accounting events apply to Barker Companys 2013 fiscal year: Jan. 1 Acquired $20,000 cash...
-
As an illustration of the difficulty in identifying monopolies, try to decide which of the following are monopolies: a train operating company; your local evening newspaper; the village hairdresser;...
-
Will competition between oligopolists always reduce total industry profits?
-
In which of the following industries is collusion likely to occur: bricks, beer, margarine, cement, crisps, washing powder, or carpets? Explain why.

Study smarter with the SolutionInn App