Assume router R2 in Figure 18.35 receives a packet with destination address 140.24.7.42. How is the packet
Question:
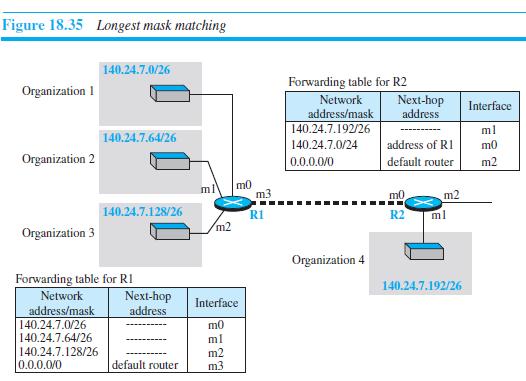
Assume router R2 in Figure 18.35 receives a packet with destination address 140.24.7.42. How is the packet routed to its final destination?
Figure 18.35
Transcribed Image Text:
Figure 18.35 Longest mask matching 140.24.7.0/26 Forwarding table for R2 Network address/mask 140.24.7.192/26 Organization 1 Next-hop address Interface ml 140.24.7.64/26 140.24.7.0/24 address of RI m0 Organization 2 default router m2 0.0.0.0/0 m0 m3 ml m0 m2 140.24.7.128/26 RI R2 ml m2 Organization 3 Organization 4 Forwarding table for RI 140.24.7.192/26 Network Next-hop address Interface address/mask 140.24.7.0/26 140.24.7.64/26 m0 ml 140.24.7.128/26 0.0.0.0/0 m2 m3 default router
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 12% (8 reviews)
The packet is sent to router R1 and eventually to organization 1 as shown bel...View the full answer

Answered By

Mamba Dedan
I am a computer scientist specializing in database management, OS, networking, and software development. I have a knack for database work, Operating systems, networking, and programming, I can give you the best solution on this without any hesitation. I have a knack in software development with key skills in UML diagrams, storyboarding, code development, software testing and implementation on several platforms.
4.90+
60+ Reviews
144+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
(a) If the header length field's value is 6 and the total length field's value is 50, how long is the data field? Show your work. (b) What is the general function of the second row in the IPv4...
-
A router using DVMRP receives a packet with source address 10.14.17.2 from interface 2. If the router forwards the packet, what are the contents of the entry related to this address in the unicast...
-
a. What does a router do if it receives a packet with a TTL value of 2? 16a.) A router will discard a packet if the Time to Live (TTL) value in an arriving packet is ______. a. 0 b. 1 c. 254 d. 256...
-
In schema normalisation, is Boyce-Codd Normal Form (BCNF) always to be preferred over 3rd Normal Form (4NF)? Explain your answer. [5 marks] 8 (TURN OVER) CST.2004.7.4 8 Economics, Law and Ethics (a)...
-
Tristan Narvaja, S.A., is the Uruguayan subsidiary of a U.S. manufacturing company. Its balance sheet for January 1 follows. The January 1 exchange rate between the U.S. dollar and the peso Uruguayo...
-
A DC motor delivers mechanical power to a rotating stainless steel shaft (k = 15.1 W/m·K) with a length of 25 cm and a diameter of 25 mm. In a surrounding with ambient air temperature of...
-
Describe the purpose of certification and licensure, and list reasons for revocation of licenses.
-
A survey of 1,700 shoppers were asked, "Does social media influence your purchase decisions?" The results, available at bit.ly/1JVaKoh, indicated that 20.3% of females responded that their purchase...
-
Suppose you borrowed $12,000 at a rate of 9.6% and must repay it in 5 equal installments at the end of each of the next 5 years. How much interest would you have to pay in the first year?
-
Claude Lopez is the president of Zebra Antiques. His employee, Dwight Francis, is due a raise. Dwight?s current benefits analysis is as follows: Company Cost (Current) Yearly Benefit Costs Employee...
-
Can router R1 in Figure 18.35 receive a packet with destination address 140.24.7.194? What will happen to the packet if this occurs? Figure 18.35 Figure 18.35 Longest mask matching 140.24.7.0/26...
-
Can the value of the header length field in an IPv4 packet be less than 5? When is it exactly 5?
-
If the group engagement team plans to request a component auditor to perform work on the financial information of a component, what must the group engagement team understand about the component...
-
How do we tell if a Find operation on a map was successful?
-
Give arguments for and against using functions (such as Swap) to encapsulate frequently used code in a sorting routine.
-
A priority queue is implemented as a heap: 1. Show how the heap would look after this series of operations: 2. What would the values of x, y, and z be after the series of operations in part (a)? 25...
-
1. What is the height of the tree? 2. What nodes are on Level 3? 3. Which levels have the maximum number of nodes that they could contain? 4. What is the maximum height of a binary search tree...
-
Read the code segment and fill in blank #24. 1. false 2. true 3. predLoc == NULL 4. location != NULL 5. answer not shown 4 Class Unsorted Type { public: //all the prototypes go here. private: int...
-
A manufacturing company operates three shifts daily. Each shift produces two models: A and B. A random sample of daily production has been taken, and the results are in the file Shift Production. a....
-
What are the key elements of a system investigation report?
-
What is the baud rate of classic 10-Mbps Ethernet?
-
Sketch the Manchester encoding on a classic Ethernet for the bit stream 0001110101.
-
Some books quote the maximum size of an Ethernet frame as 1522 bytes instead of 1500 bytes. Are they wrong? Explain your answer.
-
In which one of the following lists are ALL items relevant to the determination of employment income? Employee RPP contributions; signing bonus on accepting employment; use of an employer - owned...
-
what is the shortest maturity bond issued by pfizer that is outstanding?
-
Manufacturing Company Balance Sheet Partial balance sheet data for Diesel Additives Company at August 31 are as follows: Finished goods inventory $89,400 Prepaid insurance 9,000 Accounts receivable...

Study smarter with the SolutionInn App


