Can router R1 in Figure 18.35 receive a packet with destination address 140.24.7.194? What will happen to
Question:
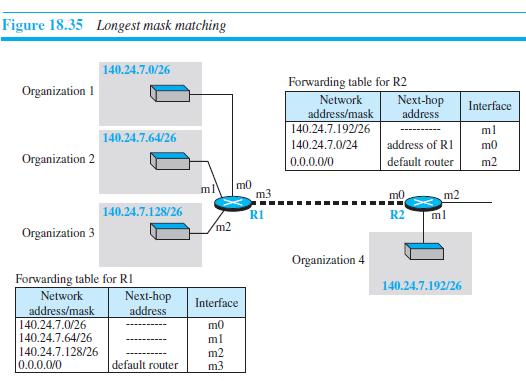
Can router R1 in Figure 18.35 receive a packet with destination address 140.24.7.194? What will happen to the packet if this occurs?
Figure 18.35
Transcribed Image Text:
Figure 18.35 Longest mask matching 140.24.7.0/26 Forwarding table for R2 Network address/mask 140.24.7.192/26 Organization 1 Next-hop address Interface ml 140.24.7.64/26 140.24.7.0/24 address of RI m0 Organization 2 default router m2 0.0.0.0/0 m0 m3 ml m0 m2 140.24.7.128/26 RI R2 ml m2 Organization 3 Organization 4 Forwarding table for RI 140.24.7.192/26 Network Next-hop address Interface address/mask 140.24.7.0/26 140.24.7.64/26 m0 ml 140.24.7.128/26 0.0.0.0/0 m2 m3 default router
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 66% (12 reviews)
Router R1 has four interfaces Let us investigate the possibility of a packet with destination ...View the full answer

Answered By

Payal Mittal
I specialize in finance and accounts.You can ask any question related to til undergradution.Organizational behaviour and HRM are my favourites for you can always relate to them and is an art with practical knowledge base.
4.90+
226+ Reviews
778+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
In Figure 18.10, assume that the link between R1 and R2 is upgraded to 170 kbps and the link between the source host and R1 is now downgraded to 140 kbps. What is the throughput between the source...
-
Assume router R2 in Figure 18.35 receives a packet with destination address 140.24.7.42. How is the packet routed to its final destination? Figure 18.35 Figure 18.35 Longest mask matching...
-
Figure 8.27 shows a switch (router) in a datagram network. Find the output port for packets with the following destination addresses: a. Packet 1: 7176 b. Packet 2: 1233 Output Destination address...
-
ABC Pty Ltd would like to set up a Virtualisation Platform on their organisation. You have been hired by Company to be their network and system administrator to implement virtualisation for...
-
Using the same balance sheet as in Problem 5, calculate Tristan Narvaja's contribution to its parent's translation loss if the exchange rate on December 31 is $U22/$. Assume all peso accounts remain...
-
HomeLife Life Insurance Company has two service departments ( actuarial and premium rating ) and two production departments ( advertising and sales ) . The distribution of each service department s...
-
The plate is deformed uniformly into the shape shown by the dashed lines. If at A, xy = 0.0075 rad., while AB = AF 0, determine the average shear strain at point G with respect to the x' and y'...
-
Assume Frozen Foods of Maine, Inc., completed the following transactions during 2012, the companys 10th year of operations: Requirement 1. Analyze each transaction in terms of its effect on the...
-
Conduct an A-B-C analysis of the child's behavior. ABC Data Collection Time Antecedent Behavior Consequence How many instances of the problem behavior (tantrums) did you observe? What were...
-
4.9 Estimate the static formation temperature from the following data (from Ref. 30): depth=7,646 ft, drilling stopped-22:00
-
An organization is granted the block 130.56.0.0/16. The administrator wants to create 1024 subnets. a. Find the number of addresses in each subnet. b. Find the subnet prefix. c. Find the first and...
-
Can the value of the header length field in an IPv4 packet be less than 5? When is it exactly 5?
-
Describe the Internet Generation, and discuss the pros and cons of teleworking.
-
Which of the following is not part of the remediation process as it relates to fraud examination and forensic accounting? 1. Identify and assess the control weaknesses that led to the original...
-
Which of the following best describes the contribution of ratio analysis to a forensic accounting or fraud examination engagement? 1. A. Ratio analysis may provide red flags or symptoms of fraudulent...
-
Select the least accurate statement: 1. A. Risks come in many forms. 2. B. RPA is an emerging technology consistent with artificial intelligence. 3. C. The Foreign Corrupt Practices Act requirements...
-
Of what crime was Al Capone convicted?
-
Should the SEC take leniency on a company that self-reports accounting improprieties and other frauds?
-
4.0 mol of monatomic gas A interacts with 3.0 mol of monatomic gas B. Gas A initially has 9000 J of thermal energy, but in the process of coming to thermal equilibrium it transfers 1000 J of heat...
-
What did Lennox gain by integrating their WMS, TMS, and labor management systems?
-
What is the length of a contention slot in CSMA/CD for (a) A 2-km twin-lead cable (signal propagation speed is 82% of the signal propagation speed in vacuum)?, (b) A 40-km multi mode fiber optic...
-
Consider five wireless stations, A, B, C, D, and E. Station A can communicate with all other stations. B can communicate with A, C and E. C can communicate with A, B and D. D can communicate with A,...
-
Six stations, A through F, communicate using the MACA protocol. Is it possible for two transmissions to take place simultaneously? Explain your answer.
-
4. The water in Earth's atmosphere blocks most of the infrared waves coming from space. In order to observe light of this wavelength, the Kuiper Airborne Observatory has been developed. The...
-
What amount of gain should Pharoah recognize on the exchange assuming lack of commercial substance?
-
If R1=7 Q, R2=3 Q, R3=9 Q, V= 12 V, and V2=8 V. Find the current (in A) that pass through R. R R R V V 2 +

Study smarter with the SolutionInn App


