Draw the graph of the NRZ-L scheme using each of the following data streams, assuming that the
Question:
a. 00000000
b. 11111111
c. 01010101
d. 00110011
Transcribed Image Text:
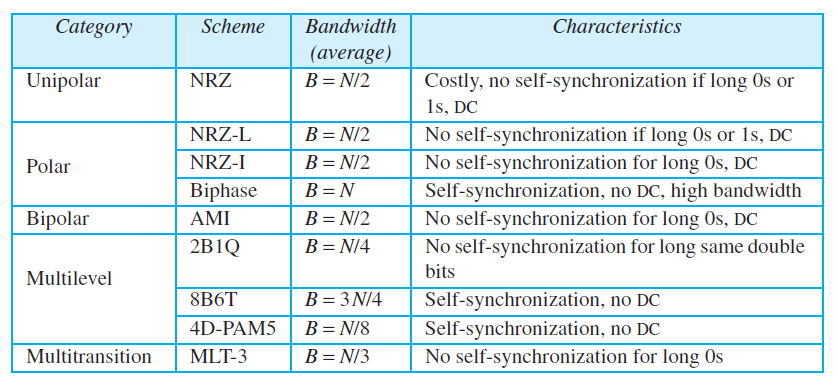
Characteristics Category Scheme Bandwidth (average) Costly, no self-synchronization if long Os or 1s, DC No self-synchronization if long Os or 1s, DC No self-synchronization for long Os, DC Self-synchronization, no DC, high bandwidth No self-synchronization for long Os, DC Unipolar NRZ B = N/2 NRZ-L B = N/2 B = N/2 NRZ-I Polar Biphase B = N Bipolar AMI B = N/2 B = N/4 2B1Q No self-synchronization for long same double bits Multilevel 8B6T B = 3 N/4 Self-synchronization, no DC Self-synchronization, no DC No self-synchronization for long 0Os 4D-PAM5 B= N/8 Multitransition MLT-3 B= N/3
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 75% (12 reviews)
See the following figure Bandwidth is proportional to 38N w...View the full answer

Answered By

Larlyu mosoti
I am a professional writer willing to do several tasks free from plagiarism, grammatical errors and submit them in time. I love to do academic writing and client satisfaction is my priority. I am skilled in writing formats APA, MLA, Chicago, and Harvard I am a statistics scientist and I can help out in analyzing your data. I am okay with SPSS, EVIEWS, MS excel, and STATA data analyzing tools.
Statistical techniques: I can do linear regression, time series analysis, logistic regression, and some basic statistical calculations like probability distributions. . I'm ready for your working projects!
Services I would offer:
• Academic writing.
• Article writing.
• Data entry.
• PDF conversion.
• Word conversion
• Proofreading.
• Rewriting.
• Data analyzing.
The best reason to hire me:
- Professional and Unique work in writing.
- 100% satisfaction Guaranteed
- within required time Express delivery
- My work is plagiarism Free
- Great communication
My passion is to write vibrantly with dedication. I am loyal and confident to give my support to every client. Because Client satisfaction is much more important to me than the payment amount. A healthy client-contractor relationship benefits in the longer term. Simply inbox me if you want clean work.
5.00+
3+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Repeat Problem P4-3 for the Manchester scheme. Problem 4-3 Draw the graph of the NRZ-L scheme using each of the following data streams, assuming that the last signal level has been positive. From the...
-
Repeat Problem P4-3 for the differential Manchester scheme. Problem 4-3 Draw the graph of the NRZ-L scheme using each of the following data streams, assuming that the last signal level has been...
-
Repeat Problem P4-3 for the MLT-3 scheme, but use the following data streams. a. 00000000 b. 11111111 c. 01010101 d. 00011000 Problem 4-3 Draw the graph of the NRZ-L scheme using each of the...
-
Data for Barry Computer Co. and its industry averages follow. a. Calculate the indicated ratios for Barry. b. Construct the DuPont equation for both Barry and the industry. c. Outline Barrys...
-
According to the AICPA Code of Professional Conduct, under what conditions if any can a CPA in public practice disclose confidential client data?
-
Consider the drug treatment system shown in the figure below. A hemispherical cluster of unhealthy cells is surrounded by a larger hemisphere of stagnant dead tissue (species B), which is turn...
-
In Problem 3.5 a regression model was developed for the gasoline mileage data using the regressor engine displacement \(x_{1}\) and number of carburetor barrels \(x_{6}\). Calculate the PRESS...
-
Summarized versions of Calabasa Corporations financial statements for two recent years are as follows. Requirement 1. Complete Calabasa Corporations financial statements by determining the missing...
-
What do you believe are the main differentiators between Core, Core Plus, Value Add and Opportunistic apartment communities? Do you believe it is better to lease student housing by the unit or by...
-
Create common size income statements and perform a basic ratio analysis of the two companies for fiscal year 2021, which is the fiscal year ended on Jan. 29, 2022/Jan. 28, 2022. (Note: fiscal year...
-
Define baseline wandering and its effect on digital transmission.
-
Distinguish between data rate and signal rate.
-
Consider the following statements: Heat is a form of energy, and energy is conserved. The heat lost by a system must be equal to the amount of heat gained by the surroundings. Therefore, heat is...
-
What are some possible real-life representations of a 3D array?
-
After referring to the Internet or other references to obtain knowledge of hamish jiddiya, draft and discuss the journal entries to account for a hamish jiddiyah deposit of $5,000 and its refund...
-
Read the FTC Guides Concerning the Use of Endorsements and Testimonials for Advertising at www.ftc.gov/os/2009/10/091005revisedendorsementguides.pdf. How will the guides affect your own brand...
-
Identify a student organization that uses social media to promote its activities and membership opportunities. Briefly review the social media zones in use by the organization and define three SMART...
-
What are the aspects of social identity? How do individuals build their social identities? How are these identities relevant to marketers?
-
A social scientist has noticed that people seem to be spending a lot of nonwork hours on computers and wants to determine if this may, in some way, be associated with social relationship satisfaction...
-
Reichenbach Co., organized in 2018, has set up a single account for all intangible assets. The following summary discloses the debit entries that have been recorded during 2018 and 2019. Instructions...
-
The DiffieHellman key exchange protocol is vulnerable to a manin-the-middle attack as shown in Figure 8.7. Outline how DiffieHellman can be extended to protect against this possibility. Figure 8.7)...
-
Suppose a user employs one-time passwords as above (or, for that matter, reusable passwords) but that the password is transmitted sufficiently slowly. (a) Show that an eavesdropper can gain access to...
-
One mechanism for resisting replay attacks in password authentication is to use one-time passwords: a list of passwords is prepared, and once password[N] has been accepted, the server decrements N...
-
Consider a Carnot heat engine placed between a finite thermal energy source and an infinite thermal energy sink. Since the temperature of the thermal source is constantly changing, then so must the...
-
A complex pair of eigenvalues are shown on the s-plane below. For this pair of eigenvalues, Wn ? W = ? damping ratio = ? time constant = ? X 2 -1 0 X -2 If r(t) is a step with magnitude 10, Use...
-
F m J, r Motor k = k T b R www C

Study smarter with the SolutionInn App


