Explain why encryption is used in the second message (from Bob to Alice) in Figure 31.23, but
Question:
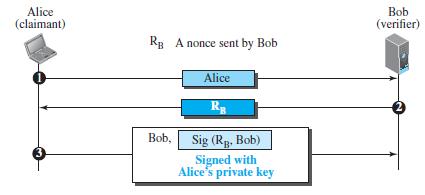
Explain why encryption is used in the second message (from Bob to Alice) in Figure 31.23, but signing is done in the third message (from Alice to Bob) in Figure 31.24.
Figure 31.23
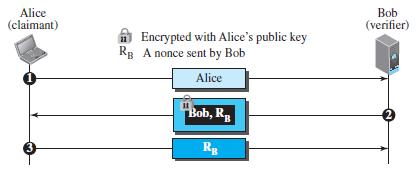
Figure 31.24
Transcribed Image Text:
Alice (claimant) Bob (verifier) A Encrypted with Alice's public key Rg A nonce sent by Bob Alice Bob, R 3 Rg
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 66% (12 reviews)
In Figure 3123 Bob encrypts the message with Alices public key encryption should ...View the full answer

Answered By

Pushpinder Singh
Currently, I am PhD scholar with Indian Statistical problem, working in applied statistics and real life data problems. I have done several projects in Statistics especially Time Series data analysis, Regression Techniques.
I am Master in Statistics from Indian Institute of Technology, Kanpur.
I have been teaching students for various University entrance exams and passing grades in Graduation and Post-Graduation.I have expertise in solving problems in Statistics for more than 2 years now.I am a subject expert in Statistics with Assignmentpedia.com.
4.40+
3+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Explain why we may need a router in Figure 9.16. Bob Alice R Alice's site Bob's site
-
Suppose Alice wants to communicate with Bob using symmetric key cryptography using a session key KS. In Section 8.2, we learned how public-key cryptography can be used to distribute the session key...
-
Change Figure 31.23 to allow bidirectional authentication. Alice needs to be authenticated for Bob and Bob for Alice.
-
A double-ended queue or deque (pronounced "deck") is a collection that is a combination of a stack and a queue. Write a class Deque that uses a linked list to implement the following API: public...
-
Critically assess the similarities and differences between the marketing communications mix elements when it comes to influence on society.
-
Define mobile CRM?
-
The tube is made of copper and has an outer diameter of \(35 \mathrm{~mm}\) and a wall thickness of \(7 \mathrm{~mm}\). Determine the eccentric load \(\mathrm{P}\) that it can support without...
-
Megan Haak and Kathy Quandt borrowed $15,000 on a 7-month, 8% note from Golden State Bank to open their business, MKs Coffee House. The money was borrowed on June 1, 2012, and the note matures...
-
rt a letter to Rose McBride. Writing Plan - Refusal to a Request Rubric Buffer: Start with a neutral statement on which both reader and writer can agree, such as a compliment, appreciation, a quick...
-
Sketch a free-body diagram of each element in the figure. Compute the magnitude and direction of each force using an algebraic or vector method, asspecified. F=0.8 kN 600
-
If Alice and Bob need to communicate using asymmetric-key cryptography, how many keys do they need? Who needs to create these keys?
-
If the one-time pad cipher (Figure 31.12 in the text) is the simplest and most secure cipher, why is it not used all of the time? Figure 31.12 Random sequence bit generator Secure key-exchange...
-
Once we check thoroughly for preconditions in the code, what data invariants can we now assume about the list?
-
Show that the Fourier transform of an imaginary and odd sequence is real and odd.
-
Show that the Fourier transform of a conjugate antisymmetric sequence is imaginary.
-
The term empty input describes what happens when a. the user presses the Spacebar Enter and then the key b. an input operation attempts to read data, but there is no data to read c. the user enters 0...
-
In the month preceding the creation of this exercise, the author made no phone calls on 19 of the 30 days in the month. Assume that 10 days from that month are randomly selected with replacement....
-
Determine the solutions of the difference equations below, supposing that the systems they represent are initially relaxed: (a) \(y(n)-\frac{1}{\sqrt{2}} y(n-1)+y(n-2)=2^{-n} \sin \left(\frac{\pi}{4}...
-
How did the reconstitution experiment of FraenkelConrat and colleagues show that the genetic information of tobacco mosaic virus (TMV) is stored in its RNA rather than its protein?
-
You have just begun your summer internship at Omni Instruments. The company supplies sterilized surgical instruments for physicians. To expand sales, Omni is considering paying a commission to its...
-
A complex view can contain which of the following? a. Data from one or more tables b. An expression c. A GROUP BY clause for data retrieved from one table d. Five columns from one table e. All of the...
-
What does FIND-MAXIMUM-SUBARRAY return when all elements of A are negative?
-
Write pseudocode for the brute-force method of solving the maximum-subarray problem. Your procedure should run in (n 2 ) time.
-
A) Translate the following C into RV641 assembly. Be sure to follow the calling (Refer to slide22 of lec6_postZoom.pdf) and comment each line of your assembly. Remember that long long is 64 bits in...
-
Given a Binary Tree, find the maximum sum path from a leaf to root. Input: 1 A Input: 10 -27 4 23 Output: Explanation Following the path 3-1, results in a sum of 4, which is the maximum path sum from...
-
On December 1 , 2 0 1 5 , your company pays $ 2 4 , 0 0 0 for rent on your store that covers the next 6 months. When you paid the cash, you debited Prepaid Rent.. The adjusting journal entry on...

Study smarter with the SolutionInn App


