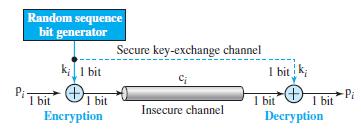
If the one-time pad cipher (Figure 31.12 in the text) is the simplest and most secure cipher,
Question:
If the one-time pad cipher (Figure 31.12 in the text) is the simplest and most secure cipher, why is it not used all of the time?
Figure 31.12
Transcribed Image Text:
Random sequence bit generator Secure key-exchange channel k;1 bit I bit k; I bit 1 bit Encryption Pi I bit Decryption I bit Insecure channel
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 80% (10 reviews)
The onetime pad is an ideal but a theoretical cipher it cann...View the full answer

Answered By

Christopher Mwenda
I am an enthusiastic person committed to a career in research, writing, and Consultancy and an excellent Media studies and communication advisor with experience in research and writing and career guidance in Media studies and communication and finally skilled in Education related subjects (Core Subjects: Physics&Chemistry, OPT: Psychology, sociology, History, Religion, and English)
0.00
0 Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Each round in a block cipher should be invertible to make the whole block invertible. Modern block ciphers use two approaches to achieve this. In the first approach, each component is invertible; in...
-
In a transposition cipher the encryption and decryption keys are often represented as two one-dimension tables (arrays) and the cipher is represented as a piece of software (a program). a. Show the...
-
A permutation block (P-box) in a modern block cipher is an example of a keyless transposition cipher. What does this statement mean? (See Figure 31.8 in the text.) Figure 31.8 2 3. 2 Straight...
-
Design a linear-time algorithm to sort an array of Comparable objects that is known to have at most three distinct values. (Edsger Dijkstra named this the Dutch-national-flag problem because the...
-
Critically assess the role of consumer and accountability groups in the context of regulation and self-regulation.
-
American Can Company announced that it was interested in acquiring a company in the health maintenance organization (HMO) field. Two decisions were involved in this act: (1) The decision to acquire...
-
Solve Prob. 13-57 if the column is an A-36 steel W12 \(\times 16\) section. Data from Prob. 13-57 Determine the \(\operatorname{load} P\) required to cause the steel \(\mathrm{W} 12 \times 50\)...
-
Casey Corporation is a manufacturing company that makes small electric motors it sells for $25 per unit. The variable costs of production are $10 per motor, and annual fixed costs of production are...
-
Below are the accounts for Mason's Landscaping and Snow Removal: Bank Service Fees Earned Accounts Receivable Rent Expense Supplies Insurance Expense Prepaid Insurance Supplies Expense Bank Loan...
-
Gloria Delgado owns 500 shares of Rio Tinto stock, listed on Nasdaq. Today is November 12 th , 2020, and the stock, currently trading at $63, is already down since the time Gloria purchased it....
-
Explain why encryption is used in the second message (from Bob to Alice) in Figure 31.23, but signing is done in the third message (from Alice to Bob) in Figure 31.24. Figure 31.23 Figure 31.24 Alice...
-
The nonce in Figure 31.22 is to prevent a replay of the third message. Eve cannot replay the third message and pretend that it is a new request from Alice, because when Bob receives the response, the...
-
Ms. Magna has thought of another possibility. She could abandon the venture entirely by selling the plane at the end of the first year. Suppose that the piston-engine plane can be sold for $150,000...
-
Allied Electronics must purchase a new automatic soldering machine to meet increased demand for its electronic goods. Of all the machines considered, management has narrowed the choices to the...
-
Write a MatLaB program to compute the impulse responses of the systems described by following difference equations: (a) \(y(n)+y(n-1)+y(n-2)=x(n)\) (b) \(4 y(n)+y(n-1)+3 y(n-2)=x(n)+x(n-4)\).
-
Look at the following pseudocode: a. What value is stored in numbers[2]? b. What value is stored in numbers[0]? Constant Integer SIZE === 3 Declare Integer numbers [SIZE] = 1, 2, 3
-
Two projects, A and B, are analyzed using ranking present worth analysis with MARR at \(i \%\). It is found that \(\mathrm{PW}(\mathrm{A})>\mathrm{PW}(\mathrm{B})\). If \(M A R R\) is changed to...
-
Find P 80 , the 80th percentile for the red blood cell counts of women.
-
(a) What was the objective of the experiment carried out by Hershey and Chase? (b) How was the objective accomplished? (c) What is the significance of this experiment?
-
This problem continues the Draper Consulting, Inc., situation from Problem 12-45 of Chapter 12. In October, Draper has the following transactions related to its common shares: Oct 1 Draper...
-
Show that the solution of T(n) = T(n 1) + n is O(n 2 ).
-
Give asymptotic upper and lower bounds for T (n) in each of the following recurrences. Assume that T (n) is constant for n 2. Make your bounds as tight as possible, and justify your answers. a. T...
-
Write pseudocode for Strassens algorithm.
-
es Hart, Attorney at Law, experienced the following transactions in Year 1, the first year of operations: 1. Accepted $16,600 on April 1, Year 1, as a retainer for services to be performed evenly...
-
Dahlia Corporation has a current accounts receivable balance of $439,516. Credit sales for the year just ended were $5,503,810. a. What is the receivables turnover? Note: Do not round intermediate...
-
Why does the organizational structure hold political significance? Provide an in-depth analysis of this concept using examples from both academic literature and real-world instances. Additionally,...

Study smarter with the SolutionInn App


