In Figure 31.10 in the text, why do we need an expansion P-box? Why cant we use
Question:
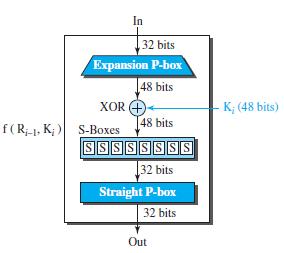
In Figure 31.10 in the text, why do we need an expansion P-box? Why can€™t we use a straight or a compression P-box?
Figure 31.10
Transcribed Image Text:
In 32 bits Expansion P-box 48 bits XOR 4 - K; (48 bits) [48 bits f(R1. K; ) S-Boxes SSSSSSSS 32 bits Straight P-box 32 bits Out
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 71% (14 reviews)
Half of the input in DES is only 32 bits The key is applied on...View the full answer

Answered By

Bhartendu Goyal
Professional, Experienced, and Expert tutor who will provide speedy and to-the-point solutions. I have been teaching students for 5 years now in different subjects and it's truly been one of the most rewarding experiences of my life. I have also done one-to-one tutoring with 100+ students and help them achieve great subject knowledge. I have expertise in computer subjects like C++, C, Java, and Python programming and other computer Science related fields. Many of my student's parents message me that your lessons improved their children's grades and this is the best only thing you want as a tea...
3.00+
2+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
In Figure 25.10 in the text, how does the server know that a client has requested a service? Figure 25.10 Sockets used in TCP communication Server O Connection establishment Client 1 Data transfer...
-
Compare and contrast the protocol field at the network layer with the port numbers at the transport layer. What is their common purpose? Why do we need two port-number fields but only one protocol...
-
Explain why encryption is used in the second message (from Bob to Alice) in Figure 31.23, but signing is done in the third message (from Alice to Bob) in Figure 31.24. Figure 31.23 Figure 31.24 Alice...
-
Why does the following code fragment not have the same effect as the code fragment in the previous question? x.next t.next = t; = x.next;
-
Explain the role of the media specialist company and suggest reasons why a client might choose such a company to handle media buying and planning.
-
Describe structured programming?
-
Assume that the wood column is pinned top and bottom for movement about the \(x-x\) axis, and fixed at the bottom and free at the top for movement about the \(y-y\) axis. Determine the maximum...
-
Solar Entertainment is a provider of cable, Internet, and on- demand video services. Solar currently sends monthly bills to its customers via the postal service. Because of a concern for the...
-
Vanessa has undertaken a significant exploration program in outback Australia that led to the discovery of a large deposit of silver. Robust geological assessments indicate the ore body comprises no...
-
The worksheet Base Data in the Excel file Credit Risk Data provides information about 425 bank customers who had applied for loans. The data include the purpose of the loan, checking and savings...
-
Explain why private-public keys cannot be used in creating a MAC.
-
A cryptographic hash function needs to be second preimage resistant, which means that given the message M and the message digest d, we should not be able to find any other message, M, whose digest is...
-
Write a structural formula or build a molecular model and give a correct IUPAC name for each alkene of molecular formula C7H14 that has a tetrasubstituted double bond.
-
Show how, using a single DFT of length \(N\), one can compute the DFT of four sequences: two even and real sequences and two odd and real sequences, all with length \(N\).
-
Based on Note 1, the fee on the Caribou Fund is best described as a: A. performance fee. B. management fee. C. administrative fee. Three years ago, the Albright Investment Management Company...
-
Home Innovations is evaluating a new product design. The estimated receipts and disbursements associated with the new product are shown below. MARR is 10 percent/year. a. What is the discounted...
-
Which of the following is a liability? (A) Machinery (B) Accounts payable for goods (C) Motor vehicles (D) Cash at bank
-
Which of the following should not be called 'Sales'? (A) Office fixtures sold (B) Goods sold on time (C) Goods sold for cash (D) Sale of item previously included in 'Purchases'
-
How do bacteriophages differ from other viruses?
-
What are the two methods used to translate financial statements and how does the functional currency play a role in determining which method is used?
-
Fill in the blanks in each of the following statements: a) Computers process data under the control of sequences of instructions called __________. b) A computer consists of various devices referred...
-
Fill in the blanks in each of the following statements: a) Objects, or more precisely the________ that objects come from, are essentially reusable software components. b) You send messages to an...
-
Fill in the blanks in each of the following statements: a) The __________executes .NET programs. b) The CLR provides various services to __________code, such as integrating software components...
-
provide requirements for a ATM machine On MS word (PLEASE USE AGILE METHODOLOGY) Who is the actor on a this ATM machine What is the system? Write a User Story for the ATM machine write system...
-
A solid metal sphere with a diameter of 2 cm and a mass of 8 g is used for the following heat transfer experiments. You can assume the temperature throughout the inside of the metal sphere is...
-
Find the charters that exhibit outliers in fuel consumption per hour. Check for standardized fuel consumption per hour larger or less than -1.5 and 1.5 respectively. -- use query3 in a "from" clause.

Study smarter with the SolutionInn App


