In Section 8.6. 1, it is shown that without sequence numbers, Trudy (a woman- in-the middle) can
Question:
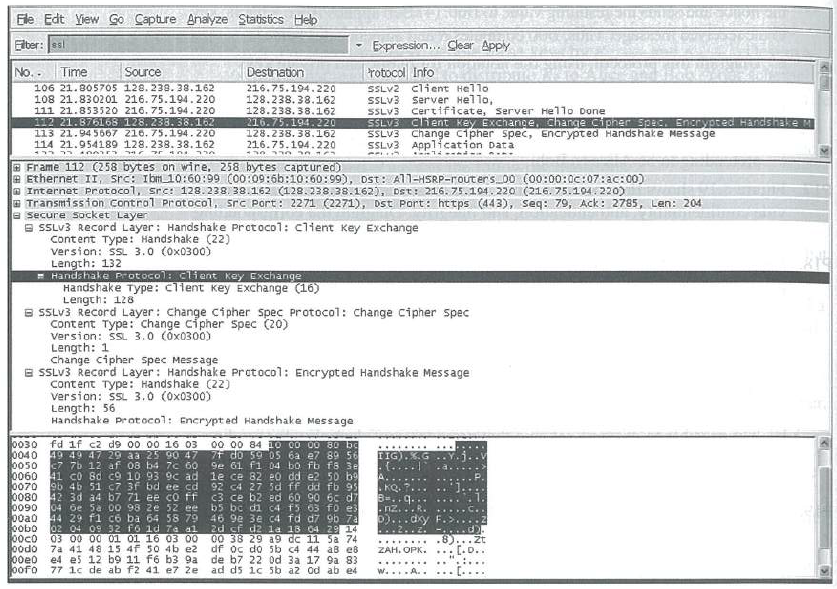 (Wire shark screenshot reprinted by permission of the Wire shark Foundation.)
(Wire shark screenshot reprinted by permission of the Wire shark Foundation.)
Transcribed Image Text:
Ele Edt Yiew Go Capture Anayze Statistics Heb Elber: ss Expression.. Clear Apply rotocol Info No.. Time Source Destnation SSLV2 Client Hello SSLV3 SSLV3 SSLV3 Chent Key Exchange, Change Cipner Spec. Encrypted Handshake M SSLV3 Change cipher spec, Encrypted Handshake Message SSLV3 Application Data 106 21.805705 128. 238. 38.162 108 21.8302 01 216. 75.194.220 216.75.194.220 128.238. 38.162 128.238. 38.162 216.75.194.220 128.238. 38.162 216.75.194.220 Server Hel1o, Certificate, Server He1lo Done 111 21.853520 216. 75.194.220 112 21.876168 128. 238. 38.162 113 21.94 5667 216. 75.194.220 114 21.954189 128.238. 38.162 E Frame 112 (258 bytes on wire, 258 bytes captured) e Ethernet II, src: Ib10:60:99 (00:09:6b:10:60:99), Dst: All-HSRP-routers 00 C00:00:0c:07:ac:00) a Internet protocol, src: 128.238. 38.162 (128.238.38.162), Dst: 216. 75.104. 220 (216. 75.104.220) a Transmission Control Protocol, src Port: 2271 (2271), Dst Port: https (443), Seq: 79, Ack: 2785, Len: 204 a secure Socket Layen E SSLV3 Record Layer: Hands hake Protoco1: client Key Exchange content Type: Handshake (22) version: SL 3.0 (0x0300) Length: 132 Handshake Protocol: client Key Exchange Handshake Type: client Key Exchange (16) Length: 128 B SSLV3 Record Layer: Change Cipher spec Protocol: Change Cipher spec content Type: change cipher Spec (20) Version: SSL 3.0 (óx0300) Length: 1 Change cipher spec Message E SSLV3 Record Layer: Handshake Protocol: Encrypt ed Handshake Message content Type: Handshake (22) version: SL 3.0 (0x0300) Length: 56 Handshake protocol: Encrypt ed Handshake Message 0030 0040 0050 0060 0070 0080 42 3d a4 b7 71 ee co ff 0090 00a0 oobo 00c0 0odo ббео рого fd if c2 d9 00 00 16 03 49 49 47 29 aa 25 90 47 c7 7b 12 af 08 b4 7c 60 41 c0 8d c9 10 93 9c ad le ce 82 e0 dd e2 50 b 9b 46 51 c7 3f bd ee cd 00 00 84 10 00 00 80 ba 7f do 59 0S 6a e7 89 56 9e 61 fi 04 bo fb fs 3e TIG).K. {.... A... KQ. 7... 92 C4 27 5d ff dd fb 95 c3 ce b2 ed 60 90 6c d7 3=..g... b5 bc di c4 f5 03 fo e 46 9e 3e c4 fd d7 9b 7a 2d sf d2 1a 18 04 29 14 00 38 29 a9 dc 11 Sa 74 df oc do 5b c4 44 aB e8 de b7 22 0d 3a 17 9a 83 ad ds ic 5b a2 od ab e4 04 oe 5a 00 98 ze 52 ee 44 29 f1 có ba 64 58 79 02 04 09 32 fo ld 7a al 03 00 00 01 01 16 03 00 7a 41 48 15 4f 50 4b e2 e4 es 12 b9 11 f6 b3 9a 77 1c de ab f2 41 e7 že -nz...R b)...dky ...... ZAH. OPK. ... [.D.. w.A.. ::
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 37% (8 reviews)
Again we suppose that SSL does not provide sequence numbers Suppose that Trudy ...View the full answer

Answered By

Joram mutua
I am that writer who gives his best for my student/client. Anything i do, i give my best. I have tutored for the last five years and non of my student has ever failed, they all come back thanking me for the best grades. I have a degree in economics, but i have written academic papers for various disciplines due to top-notch research Skills.In additional, I am a professional copywriter and proofreader.
5.00+
2+ Reviews
10+ Question Solved
Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0133594140
7th edition
Authors: James Kurose, Keith Ross
Question Posted:
Students also viewed these Computer science questions
-
In Section 8.5.1. it is shown that without sequence numbers. Trudy (a woman-in-the middle) can wreak havoc in an SSL session by interchanging TCP segments. Can Tmdy do something similar by deleting a...
-
As described in Section 5.7, virtual memory uses a page table to track the mapping of virtual addresses to physical addresses. This exercise shows how this table must be updated as addresses are...
-
SYN cookies were discussed in Section 3.5.6. a. Why is it necessary for the server to use a special initial sequence number in the SYNACK? b. Suppose an attacker knows that a target host uses SYN...
-
Pls Show the answers and explanation 5. AJD Company had a production run of 8,000 pairs of jeans during the last week of June, with the following unit costs: Final inspection revealed that 600 pairs,...
-
How has Vladimir Putin been able to accumulate so much political power in Russia?
-
Provide some examples of customer- and provider-routed services that you have encountered that are different from those described in this chapter. Can you identify any improvements to these processes?
-
Owing to a small federal grant from the Department of Housing and Urban Development (HUD) to the Town of Stillman, Nadine Gordimer, CPA has performed grant audits for the town in each of the past...
-
A small, private university specializing in graduate programs needs to keep track of the list of students who (a) apply, (b) are accepted, and (c) actually enroll in the university. For security...
-
You have a stock bottle of 3mM tetrodotoxin solution, but your protocol states that you need 6ml of 1mM tetrodotoxin (MW-319.27 g/mol). How much of your 3mM stock solution (liquid) should you use to...
-
LaneScapes Incorporated Transactions Background LaneScapes Incorporated is a newly founded corporation in Oregon that provides premium ecologically conscious landscaping services in Lane County....
-
What is the purpose of the random nonces in the SSL handshake?
-
In the SSL record, there is a field for SSL sequence numbers. True or false?
-
Discuss whether you consider that all products on sale in the high street can be sold as easily via the Internet.
-
Describe the core elements required within the DSCSA (Drug Supply Chain Security Act) Describe the role of pharmacy benefit managers (PBMs) in the US Healthcare System Explain the overall structure...
-
Discuss the significance of Process Hazard Analysis (PHA) techniques, such as Hazard and Operability Studies (HAZOP) and Failure Modes and Effects Analysis (FMEA), in identifying potential risks in...
-
Joe runs up the stadium steps as an athletic drill. There are 50 steps and each one is 0.30 meters high and 0.50 meters deep. If Joe has a mass of 95 kg and runs the steps in 30 seconds, how much...
-
You are an investigator called to the scene of a suspicious death. Once on scene, you are told by the initial responding patrol officer that a relative of the female occupant of the home came to the...
-
How does the concept of inherently safer design (ISD) integrate with hazard analysis to promote safety at the earliest stages of process design? Provide examples where ISD principles have...
-
Two parallel concentric disks, 20 cm and 40 cm in diameter, are separated by a distance of 10 cm. The smaller disk ( = 0.80) is at a temperature of 300C. The larger disk ( = 0.60) is at a temperature...
-
Find the center of mass of a thin triangular plate bounded by the y-axis and the lines y = x and y = 2 - x if (x, y) = 6x + 3y + 3.
-
Suppose that N switches supporting K VLAN groups are to be connected via a trunking protocol. How many ports are needed to connect the switches? Justify your answer.
-
If all the links in the Internet were to provide reliable delivery service, would the TCP reliable delivery service be redundant? Why or why not?
-
What are some of the possible services that a link-layer protocol can offer to the network layer? Which of these link-layer services have corresponding services in IP? In TCp?
-
ENG 571, Theory of Energy and Sustainability Engineering, Sp 2023 HW# 3, Due on Friday, April 28 (*two days later than stated on the syllabus) Note: Students who are tasking this course for 4 hours...
-
Discuss your personal experience with dynamic pricing ( airlines , hotels, Uber, event tickets, etc. ) . Also, discuss any professional experience including: What revenue - management methods does...
-
you to play the role of an international marketing manager from an international consulting company. Your mission is helping your selected Japanese company in Japan to marketing its product or...

Study smarter with the SolutionInn App


