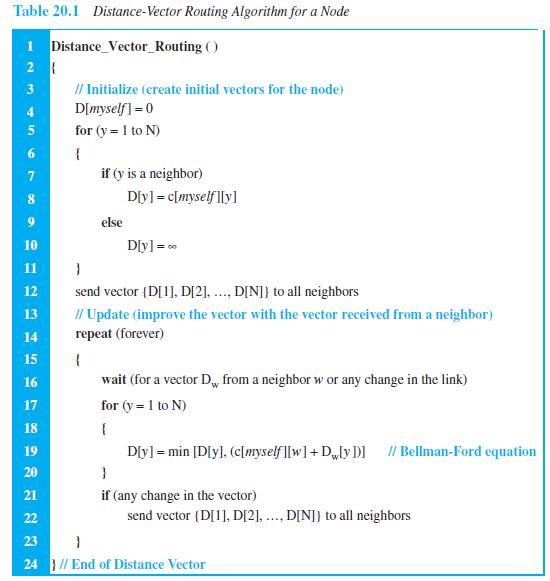
Write a program to simulate the distance-vector algorithm (Table 20.1). for (y = 1 to N) {
Question:
Write a program to simulate the distance-vector algorithm (Table 20.1).
Transcribed Image Text:
for (y = 1 to N) { if (y is a neighbor) D[y] = c[myself][y] else 10 D[y] = 0 11 } send vector {D[1], D[2], ..., D[N]} to all neighbors // Update (improve the vector with the vector received from a neighbor) repeat (forever) 12 13 14 15 { 16 wait (for a vector Dw from a neighbor w or any change in the link) for (y = 1 to N) 17 18 { 19 D[y] = min [D[y], (c[myself][w] + Dw[y])] // Bellman-Ford equation 20 } 21 if (any change in the vector) 22 send vector {D[1], D[2], ..., D[N]} to all neighbors 23 } 24 } // End of Distance Vector 6.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 91% (12 reviews)
The first program simulates the DistanceVector protocol The input object ...View the full answer

Answered By

Charles mwangi
I am a postgraduate in chemistry (Industrial chemistry with management),with writing experience for more than 3 years.I have specialized in content development,questions,term papers and assignments.Majoring in chemistry,information science,management,human resource management,accounting,business law,marketing,psychology,excl expert ,education and engineering.I have tutored in other different platforms where my DNA includes three key aspects i.e,quality papers,timely and free from any academic malpractices.I frequently engage clients in each and every step to ensure quality service delivery.This is to ensure sustainability of the tutoring aspects as well as the credibility of the platform.
4.30+
2+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Write a program to simulate the link-state algorithm (Table 20.2). Dijkstra's Algorithm ( ) // Initialization Tree = {root} 3 I/ Tree is made only of the root 4. for (y = 1 to N) II N is the number...
-
Write a program to simulate the path-vector algorithm (Table 20.3). Table 20.3 Path-vector algorithm for a node 1 Path_Vector_Routing ( ) 2 { // Initialization for (y = 1 to N) 3 { if (y is myself)...
-
Write a program to simulate the sending-site FSMs for the Stop-and-Wait protocol (Figure 23.21). Figure 23.21 FSMS for the Stop-and-Wait protocol Sender Request came from application. Make a packet...
-
Jack Williams works in a very active department called purchasing. He works with store managers, marketing, and supply companies. The people in his department try to have the right product, in the...
-
Wilson Corporation (not real) has a targeted capital structure of 40% long term debt and 60% common stock. The debt is yielding 6% and the corporate tax rate is 35%. The common stock is trading at...
-
Buenolorl Company produces a well-known cologne. The standard manufacturing cost of the cologne is described by the following standard cost sheet: Management has decided to investigate only those...
-
The finite element method is similar to a. Rayleigh's method b. the Rayleigh-Ritz method c. the Lagrange method
-
A sphere made of copper having 10 mm inner diameter is placed to an environment at 75C. When the sphere is removed from this environment and exposed to air flow at atmospheric pressure (1 atm). The...
-
Over the past several years, Japan ranked within the top three exporters of cars in the world. How does the theory of comparative advantage explain the dominance of Japanese cars in the global...
-
Go back and quickly review the rules that the Sarbanes-Oxley Act of 2002 placed on the auditing profession as described in this chapter. What do you think are the two or three main purposes of these...
-
In a graph, if we know that the shortest path from node A to node G is (A B E G), what is the shortest path from node G to node A?
-
Distinguish between multicasting and multiple unicasting.
-
A hollow box beam is constructed with webs of Douglas-fir plywood and flanges of pine, as shown in the figure in a cross-sectional view. The plywood is 1 in. thick and 12 in. wide; the flanges are 2...
-
Good day, highly esteemed tutors, please help with these questions 1. Evaluate the role of institutional investors, auditing, ethical, and CSR challenges in promoting sustainable and socially...
-
Analyzing Stockholders' Equity Accounts and Transactions Nutrien Ltd.--the world's largest potash producer-is a Canadian corporation based in Saskatoon, Saskatchewan. The following is information...
-
Rummaze Crafts, an artificial intelligence (AI) inspired robotic company specializing in the use of Al to manufacture handcrafted wooden sculptures, anticipates incurring $250,000 in fixed...
-
Martindale Company, a 100% owned subsidiary of Weisman Corporation, sells inventory to Weisman at a 20% profit on selling price. The following data are available pertaining to inter-company purchases...
-
Take a look at this article on how the law was ignored in the clearing of Kranji Woodland to make way for development....
-
On January 1, 2018, Wilmes Floral Supplies borrowed $2,413 from Bower Financial Services. Wilmes Floral Supplies gave Bower a $2,500 note with a maturity date of December 31, 2019. The note specified...
-
Find the velocity, acceleration, and speed of a particle with the given position function. r(t) = (t 2 , sin t - t cos t, cos t + t sin t), t > 0
-
Compare the medium of a wired LAN with that of a wireless LAN in todays communication environment.
-
A program to simulate the calculation of CRC.
-
In an 802.11, give the value of the address 1 field in each of the following situations (left bit defines To DS and right bit defines From DS). a. 00 b. 01 c. 10 d. 11
-
What is thread affinity, and how does it influence performance in multi-core systems? What tools or techniques are available for tuning thread affinity ?
-
Management of Mittel Company wants to reduce the elapsed time from when a customer places an order to when it is shipped. It provided the following data for a recent quarter: Inspection time Wait...
-
For a language L over alphabet , we define L = {xz *y * with |x| = |y| = |2| such that ryz L}. For example, if L = {a, to, cat, math, solve, theory}, then L = {ct,thry}. Prove that if L is regular,...

Study smarter with the SolutionInn App


