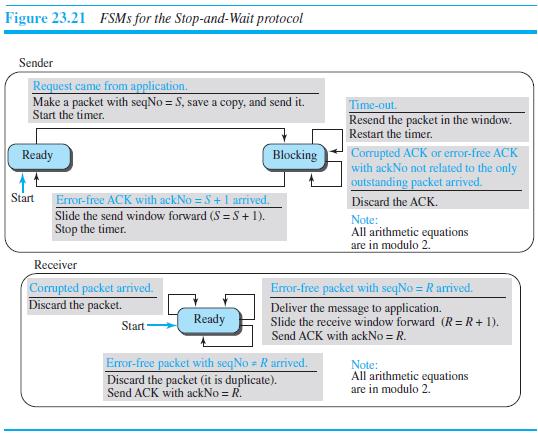
Write a program to simulate the sending-site FSMs for the Stop-and-Wait protocol (Figure 23.21). Figure 23.21 FSMS
Question:
Write a program to simulate the sending-site FSMs for the Stop-and-Wait protocol (Figure 23.21).
Transcribed Image Text:
Figure 23.21 FSMS for the Stop-and-Wait protocol Sender Request came from application. Make a packet with seqNo = S, save a copy, and send it. Start the timer. Time-out Resend the packet in the window. Restart the timer. Corrupted ACK or eror-free ACK with ackNo not related to the only outstanding packet arrived. Ready Blocking Start Error-free ACK with ackNo =5+ 1 arrived. Discard the ACK. Slide the send window forward (S =S+1). Stop the timer. Note: All arithmetic equations are in modulo 2. Receiver Corrupted packet arrived. Discard the packet. Error-free packet with seqNo = R arrived. Deliver the message to application. Ready Slide the receive window forward (R= R + 1). Send ACK with ackNo = R. Start Error-free packet with seqNo = R arrived. Discard the packet (it is duplicate). Send ACK with ackNo = R. Note: All arithmetic equations are in modulo 2.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 70% (10 reviews)
The second program simulates the StopAndWait protocol at the sender site It ...View the full answer

Answered By

Sarah Khan
My core expertise are:
-_ Finance
-_ Business
-_ Management
-_ Marketing Management
-_ Financial Management
-_ Corporate Finance
-_ HRM etc...
I have 7+ years of experience as an online tutor. I have hands-on experience in handling:
-_ Academic Papers
-_ Research Paper
-_ Dissertation Paper
-_ Case study analysis
-_ Research Proposals
-_ Business Plan
-_ Complexed financial calculations in excel
-_ Home Work Assistance
-_ PPT
-_ Thesis Paper
-_ Capstone Papers
-_ Essay Writing etc...
5.00+
91+ Reviews
92+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Write a program to simulate the sending-site FSMs for the simple protocol (Figure 23.18). Figure 23.18 FSMS for the simple protocol Request came from application. Packet arrived. Make a packet and...
-
Write a program to simulate the sending-site FSMs for the Go-Back-N protocol (Figure 23.27).
-
Write a program to simulate the sending-site FSMs for the Selective Repeat protocol (Figure 23.34). Figure 23.34 FSMS for SR protocol Sender Time-out. Resend all outstanding packets in window. Reset...
-
An air-filled X-band rectangular waveguide has dimensions a = 2.286 cm and b = 1.016 cm. If the waveguide has copper walls ( = o , = o , = 5.8 x 10 7 S/m), find the attenuation in dB/m due to the...
-
Go to the BEA website at www.bea.gov/newsreleases/international/intinv / intinvnewsrelease.htm and download annual data starting in 1976 on the United States' end-of-year international investment...
-
A firm improves its forecast accuracy using better marketing intelligence. What impact will this have on supply chain inventories and profitability? Why?
-
What is statelessness, and why is it a problem?
-
Ford 10-K, Toyota 20-F 1a. What are the key long-lived asset and related expense accounts for Ford? 1b. What are the critical accounting policies for these accounts? 1c. Calculate and compare...
-
3. (15 points) Sasha is a well-paid accountant, and for every hour she works, she earns $50 before taxes. Further- more, suppose that she can work up to 10 hours per day, 365 days per year. Draw her...
-
Wolfe Industries pays its employees on a semimonthly basis. Using the wagebracket tables in Appendix C, compute the federal income tax deductions for the following employees of Wolfe Industries. No...
-
Compare the range of 16-bit addresses, 0 to 65,535, with the range of 32-bit IP addresses, 0 to 4,294,967,295 (discussed in Chapter 18). Why do we need such a large range of IP addresses, but only a...
-
Operating systems assign a process number to every running application program. Can you explain why these process numbers cannot be used instead of port numbers?
-
The average free convection coefficient for the exterior surfaces of a long, horizontal rectangular duct exposed to a quiescent fluid can be estimated from the Hahn-Didion (H-D) correlation [ASHRAE...
-
Destiny's Child", the local parent's association, are worried about the education workers going on strike and the impact this will have on them and their children. The "Backstreet Boys", the local...
-
You negotiate a car price to $ 2 2 , 0 0 0 . You must add sales tax to the purchase of 1 0 . 2 5 % ( this varies from state to state ) , which gives you the total purchase price for the car at $ 2 4...
-
The following data are provided for Sandhill Corp's past two fiscal years: Dec 31, 2024 Dec 31, 2023 Cumulative preferred shares, $5, no par value, 4700 shares outstanding $206000 $206000 Common...
-
2. Consider a 50 km fiber link (with a loss of 0.25 dB km) having four connectors in its path. If each connector has a loss of 1.8 dB, then calculate the total loss. The loss at the source to the...
-
Mary age 34, fell from a ladder while hanging decorations for Halloween. She fell onto her outstretched hands from the top rung of the ladder.Immediately after, Anna notes that her wrist is swollen...
-
The city of Pawnee issues a fixed number of fishing licenses each year. a. Using the accompanying graph, demonstrate the effect of a limit of 100 fishing licenses at a cost of $20 per license. b. Is...
-
White Bolder Investments (WBI) You are an intern working for WBI, a large investment advisory services in Sydney. Among other regular customers, WBI has been providing advisory services for Jumbo...
-
Write a program to simulate the distance-vector algorithm (Table 20.1). for (y = 1 to N) { if (y is a neighbor) D[y] = c[myself][y] else 10 D[y] = 0 11 } send vector {D[1], D[2], ..., D[N]} to all...
-
Write a program to simulate the link-state algorithm (Table 20.2). Dijkstra's Algorithm ( ) // Initialization Tree = {root} 3 I/ Tree is made only of the root 4. for (y = 1 to N) II N is the number...
-
Write a program to simulate the path-vector algorithm (Table 20.3). Table 20.3 Path-vector algorithm for a node 1 Path_Vector_Routing ( ) 2 { // Initialization for (y = 1 to N) 3 { if (y is myself)...
-
9 Question 6 (3 marks) Distance can be measured in kilometres or in miles. The following graph shows the relationship between distance in kilometres and distance in miles. 100 80 (40, 64.4) distance...
-
5.6.4 The pipeline shown in Fig. X5.6.3 supplies water to a hydroelectric power plant, the elevation of which is 650 m below the level of the water at intake to the pipe. If 8 per cent of this total,...
-
The first part of the course we discuss methods of legal dispute settlement (i.e. how the law aims to resolve disputes/ how we use legal processes to settle or end disputes). In W3 and W4 we examine...

Study smarter with the SolutionInn App


