Consider the instruction formats of the basic computer shown in Fig. 5-5 and the list of instructions
Question:
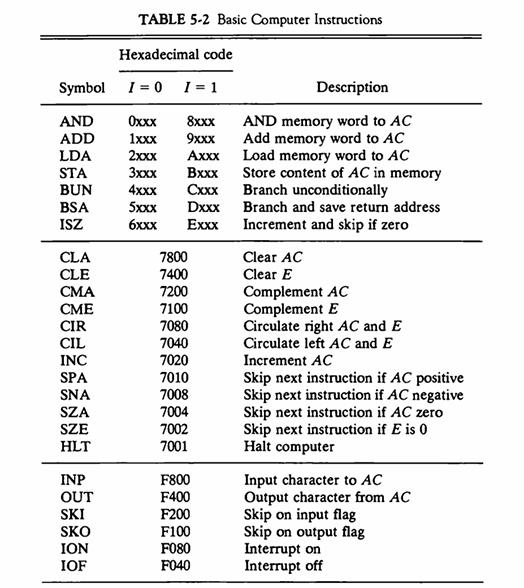
Consider the instruction formats of the basic computer shown in Fig. 5-5 and the list of instructions given in Table 5-2. For each of the following 16-bit instructions, give the equivalent four-digit hexadecimal code and explain in your own words what it is that the instruction is going to perform.
a. 0001 0000 0010 0100
b. 1011 0001 0010 0100
c. 0111 0000 0010 0000
Fig. 5-5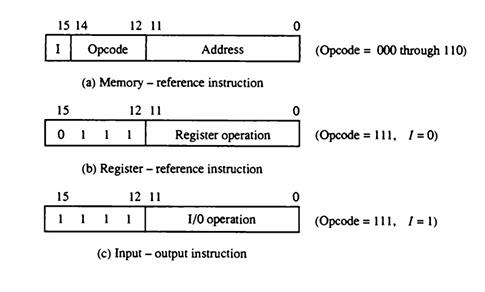
Table 5-2
Transcribed Image Text:
15 14 I 15 0 15 1 12 11 Opcode (a) Memory-reference instruction 12 11 1 1 1 Register operation (b) Register - reference instruction 12 11 1 Address 1/0 operation (c) Input-output instruction 0 (Opcode = 000 through 110) (Opcode = 111, 1 = 0) (Opcode = 111, 1=1)
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 50% (2 reviews)
We must first comprehend the syntax of the instructions before mapping the provided 16bit instructio...View the full answer

Answered By

Asim farooq
I have done MS finance and expertise in the field of Accounting, finance, cost accounting, security analysis and portfolio management and management, MS office is at my fingertips, I want my client to take advantage of my practical knowledge. I have been mentoring my client on a freelancer website from last two years, Currently I am working in Telecom company as a financial analyst and before that working as an accountant with Pepsi for one year. I also join a nonprofit organization as a finance assistant to my job duties are making payment to client after tax calculation, I have started my professional career from teaching I was teaching to a master's level student for two years in the evening.
My Expert Service
Financial accounting, Financial management, Cost accounting, Human resource management, Business communication and report writing. Financial accounting : • Journal entries • Financial statements including balance sheet, Profit & Loss account, Cash flow statement • Adjustment entries • Ratio analysis • Accounting concepts • Single entry accounting • Double entry accounting • Bills of exchange • Bank reconciliation statements Cost accounting : • Budgeting • Job order costing • Process costing • Cost of goods sold Financial management : • Capital budgeting • Net Present Value (NPV) • Internal Rate of Return (IRR) • Payback period • Discounted cash flows • Financial analysis • Capital assets pricing model • Simple interest, Compound interest & annuities
4.40+
65+ Reviews
86+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Derive the circuit for a 9's complementer when decimal digits are represented in the excess-3 code (Table 3-6). A mode control input determines whether the digit is complemented or not. What is the...
-
It is necessary to design an adder for two decimal digits represented in the excess-3 code (Table 3-6). Show that the correction after adding two digits with a 4-bit binary adder is as follows: a....
-
Explain in your own words what it means when one alternative stochastically dominates another.
-
If an investor holds a credit-linked note and the credit event does not occur, the investor receives: A. All promised cash flows as scheduled. B. All coupon payments as scheduled but not the par...
-
Harrington Inc. is introducing a new product in its line of household appliances. Household products generally have 10-year life cycles and are viewed as capital budgeting projects over that period....
-
Define each of the following terms using graphs or equations to illustrate your answers whenever feasible: a. Risk; stand-alone risk; probability distribution b. Expected rate of return, c. Standard...
-
Why is significance an important construct in the study and use of inferential statistics?
-
Using the appropriate tables, solve each of the following: Required 1. Beginning December 31, 2008, five equal withdrawals are to be made. Determine the equal annual withdrawals if $30,000 is...
-
Design a simple relational database schema for a library management system, including tables for books, authors, members, and loans .
-
Why did hackers develop botnets? What advantage do they offer the criminals? How are they detected? Why do larger ad networks have an advantage in click fraud detection?
-
The following register transfers are to be executed in the system of Fig. 5-4. For each transfer, specify: (1) The binary value that must be applied to bus select inputs S 2 , S 1 , and S 0 ; (2) The...
-
What measures do governments use to promote exports and restrict imports? Who benefits and who loses from protectionist policies? What is the net outcome for society?
-
The height of the Sun above the horizon is 31.6 o . You sit on a raft and want to orient a mirror so that sunlight reflects off the mirror and travels at an angle of 45 o in the water of refractive...
-
6. Three particles, A, B and C, are attached by light inextensible strings AB and BC. Particles A and B are held at an equal height of 2 m above a horizontal floor. B rests on a rough horizontal...
-
To remove a nut from an old rusty bolt, Jefferson applies a 96.5 N force to the end of a wrench perpendicular to the wrench handle. The distance from the applied force to the axis of the bolt is...
-
A sprinter performs a 100 m dash. During the initial s25 = 25m he accelerates, obtaining an average acceleration a = 2.3 m/s2 . After the first 25m he holds the velocity constant. Between the 90m...
-
A motor is exerting a clockwise torque on a wheel, with a force of 24.4 N, and a lever arm of 0.22 m. An outside force is exerting a counter-clockwise torque, with a force of 7.9 N, and a lever arm...
-
Nitrogen gas (N 2 ) reacts with hydrogen gas (H 2 ) to form ammonia gas (NH 3 ). You have nitrogen and hydrogen gases in a 15.0- L container fitted with a movable piston (the piston allows the...
-
Write an essay describing the differing approaches of nursing leaders and managers to issues in practice. To complete this assignment, do the following: 1. Select an issue from the following list:...
-
Give a proof of Proposition 11.10 Proposition 11.10 The algorithm for deleting an entry from a red-black tree with n entries takes O(log n) time and performs O(log n) recolorings and at most two...
-
Is the search tree of Figure 11.22(a) a (2,4) tree? Why or why not? Figure 11.22(a) 22 5 10 25 3 4 23 24 6 8 14 27 11 13 17 (a)
-
Our implementation of the treeSearch utility, from Code Fragment 11.3, relies on recursion. For a large unbalanced tree, it is possible that Javas call stack will reach its limit due to the recursive...
-
Among the configurations you explored in this module, which one is a true security function? Why What are some steps I would take to secure my home wireless network?
-
Task statements in Functional Job Analysis are rated on their complexity on which three main scales? Explain all these scales with two suitable examples.
-
Describe why companies provide benefits to their employees.? What effect do companies expect benefits will have on employee work behavior?

Study smarter with the SolutionInn App