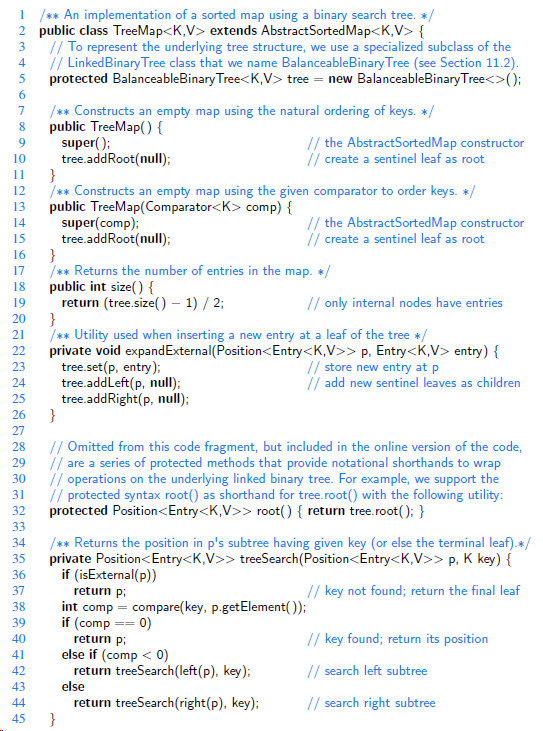
Our implementation of the treeSearch utility, from Code Fragment 11.3, relies on recursion. For a large unbalanced
Question:
Transcribed Image Text:
1 /** An implementation of a sorted map using a binary search tree. */ 2 public class TreeMap
1 /** An implementation of a sorted map using a binary search tree. */ 2 public class TreeMap extends AbstractSortedMap { // To represent the underlying tree structure, we use a specialized subclass of the // LinkedBinary Tree class that we name BalanceableBinary Tree (see Section 11.2). protected BalanceableBinary Tree tree = new BalanceableBinary Tree<>(); /** Constructs an empty map using the natural ordering of keys. */ public TreeMap() { super(); tree.addRoot(null); } /** Constructs an empty map using the given comparator to order keys. */ public TreeMap(Comparator comp) { super(comp); tree.addRoot(null); / the AbstractSortedMap constructor // create a sentinel leaf as root 9. 10 11 12 13 // the AbstractSortedMap constructor // create a sentinel leaf as root 14 15 16 /** Returns the number of entries in the map. */ public int size() { return (tree.size() – 1) / 2; } /** Utility used when inserting a new entry at a leaf of the tree */ private void expandExternal(Position> p, Entry entry) { tree.set(p, entry); tree.addLeft(p, null); tree.addRight(p, null); 17 18 // only internal nodes have entries 19 20 21 22 // store new entry at p // add new sentinel leaves as children 23 24 25 26 27 // Omitted from this code fragment, but included in the online version of the code, // are a series of protected methods that provide notational shorthands to wrap // operations on the underlying linked binary tree. For example, we support the // protected syntax root() as shorthand for tree.root() with the following utility: protected Position> root() { return tree.root(); } 28 29 30 31 32 33 /** Returns the position in p's subtree having given key (or else the terminal leaf).*/ private Position> treeSearch(Position> p. K key) { if (isExternal(p)) return p; int comp = compare(key, p.getElement()); if (comp 34 35 36 // key not found; return the final leaf 37 38 39 // key found; return its position 40 return p: else if (comp < 0) return treeSearch(left(p), key); else 41 // search left subtree 42 43 // search right subtree return treeSearch(right(p), key); } 44 45
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 63% (11 reviews)
private Position treeSearchPosition p K key Position walk p while i...View the full answer

Answered By

Mamba Dedan
I am a computer scientist specializing in database management, OS, networking, and software development. I have a knack for database work, Operating systems, networking, and programming, I can give you the best solution on this without any hesitation. I have a knack in software development with key skills in UML diagrams, storyboarding, code development, software testing and implementation on several platforms.
4.90+
63+ Reviews
152+ Question Solved
Related Book For 

Data Structures and Algorithms in Java
ISBN: 978-1118771334
6th edition
Authors: Michael T. Goodrich, Roberto Tamassia, Michael H. Goldwasser
Question Posted:
Students also viewed these Computer science questions
-
Consider lines 3133 of Code Fragment 10.8 in our implementation of the class ChainHashMap. We use the difference in the size of a secondary bucket before and after a call to bucket.remove(k) to...
-
If the outermost while loop of our implementation of quickSortInPlace (line 9 of Code Fragment 12.6) were changed to use condition left < right, instead of condition left /** Sort the subarray S[a.b]...
-
In our implementation of the scale function (page 25), the body of the loop executes the command data[j] *= factor. We have discussed that numeric types are immutable, and that use of the *= operator...
-
You are looking at buying a piece of real estate and you intend to borrow as much as you possibly can from a bank to buy the property. The bank you are dealing with has a requirement that the LVR for...
-
Mercury Company has only one inventory pool. On December 31, 2018, Mercury adopted the dollar-value LIFO inventory method. The inventory on that date using the dollar-value LIFO method was $200,000....
-
Since 2 0 X 0 , Ames Steel Company has replaced all of its major manufacturing equipment and now has the following equipment recorded in the appropriate accounts. Ames uses a calendar year as its...
-
Determine the magnitude and direction of the anchoring force needed to hold the horizontal elbow and nozzle combination shown in Fig. P5.45 in place. Atmospheric pressure is \(100...
-
The following is a code for one product in an extensive cosmetic line: L02002Z621289. L means that it is a lipstick, 0 means it was introduced without matching nail polish, 2002 is a sequence code...
-
How do you architect a comprehensive data protection framework integrating backup and restore mechanisms, employing advanced techniques such as incremental-forever backups and point-in-time recovery,...
-
Judge and Cable (2010) report the results of a study demonstrating a negative relationship between weight and income for a group of women professionals. Following are data similar to those obtained...
-
Is the search tree of Figure 11.22(a) a (2,4) tree? Why or why not? Figure 11.22(a) 22 5 10 25 3 4 23 24 6 8 14 27 11 13 17 (a)
-
Dr. Amongus claims that the order in which a fixed set of entries is inserted into an AVL tree does not matterthe same AVL tree results every time. Give a small example that proves he is wrong.
-
Corporate restructuring can be voluntary or involuntary. True of False
-
This is an open exercise for the readers. Every algorithm that is solved using recursion (system stack) can also be solved using user defined or library defined stack. So try to figure out what all...
-
During 2015, Simms Company redeemed 2,000,000 of bonds payable for 1,880,000 cash. Indicate how this transaction would be reported on a statement of cash flows, if at all.
-
Were the shares of stock issued as a result of Snaps initial public offering (IPO) sold in a primary market or a secondary market? Was the IPO an example of direct finance or indirect finance?
-
Under what circumstances might a monopolistically competitive firm continue to earn an economic profit as new firms enter its market?
-
Sony suffered losses selling televisions from 2004 to 2013, before finally earning a small profit on this business from 2014 to 2016. Given the strong consumer demand for plasma, LCD, and LED...
-
Which information attributes are seldom or never applied to software elements?
-
Tiger, Inc. signed a lease for equipment on July 1, 2007.The lease is for 10 years (the useful life of the asset).The first of 10 equal annual payments of $500,000 was made on July 1, 2007.The...
-
We can improve the running time of quicksort in practice by taking advantage of the fast running time of insertion sort when its input is "nearly" sorted. Upon calling quicksort on a subarray with...
-
Consider a sorting problem in which we do not know the numbers exactly. Instead, for each number, we know an interval on the real line to which it belongs. That is, we are given n closed intervals of...
-
Argue that for any constant 0 < 1/2, the probability is approximately 1 - 2 that on a random input array, PARTITION produces a split more balanced than 1 to .
-
why you assume value of Machine A is assumed to decrease by $7,000 each year for the purpose of these calculations?
-
1. You want to create a Dog object. Which of the following would you use to describe it? (Choose all that apply.) A. String breed B. int age C. boolean isADog D. String ownerName E....
-
Part 1: Cathy Forth Photography Services (20 marks) You have been hired by Cathy Forth as her new bookkeeper. She has given you the following information: Use the current date and provide an...

Study smarter with the SolutionInn App