Fill in the right-hand column of the following table to describe the processing of the call instruction
Question:
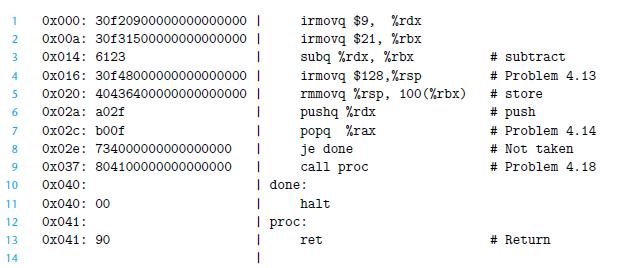
Fill in the right-hand column of the following table to describe the processing of the call instruction on line 9 of the object code in Figure 4.17:
![Stage Fetch Stage Decode Execute Generic call Dest icode:ifun M [PC] valC Mg[PC +1] valP - PC +9 Generic](https://dsd5zvtm8ll6.cloudfront.net/images/question_images/1698/2/1/0/2876538a1ef126efUntitled.png)
Figure 4.17
Transcribed Image Text:
Stage Fetch Stage Decode Execute Generic call Dest icode:ifun ← M₁ [PC] valC Mg[PC +1] valP - PC +9 Generic call Dest valB R[%rsp] valE ← valB + (-8) Mg[valE] R[%rsp] + valE PC valC ← valP Specific call 0x041 Memory Write back PC update What effect would this instruction execution have on the registers, the PC, and the memory? Specific call 0x041
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (2 reviews)
We can see that this instruction is located at address 0x037 and is 9 by...View the full answer

Answered By

Sarfraz gull
have strong entrepreneurial and analytical skills which ensure quality tutoring and mentoring in your international business and management disciplines. Over last 3 years, I have expertise in the areas of Financial Planning, Business Management, Accounting, Finance, Corporate Finance, International Business, Human Resource Management, Entrepreneurship, Marketing, E-commerce, Social Media Marketing, and Supply Chain Management.
Over the years, I have been working as a business tutor and mentor for more than 3 years. Apart from tutoring online I have rich experience of working in multinational. I have worked on business management to project management.
5.00+
3+ Reviews
10+ Question Solved
Related Book For 

Computer Systems A Programmers Perspective
ISBN: 9781292101767
3rd Global Edition
Authors: Randal E. Bryant, David R. O'Hallaron
Question Posted:
Students also viewed these Computer science questions
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
Fill in the right-hand column of the following table to describe the processing of the irmovq instruction on line 4 of the object code in Figure 4.17: Figure 4.17 Stage Fetch Decode Execute Generic...
-
Fill in the right-hand column of the following table to describe the processing of the popq instruction on line 7 of the object code in Figure 4.17. Figure 4.17 Stage Fetch Generic popq rA icode:ifun...
-
(a) An n n matrix K is the encryption matrix for the Hill cipher. Give the encryption formula. (b) The plaintext is (2, 5, 1,0). Encrypt it (show your work and the ciphertext) using the Hill cipher...
-
Lucy Dunworth, developer of a shopping mall, entered into an easement and operating agreement with three major department stores. One of the covenants in the agreement was that each occupant promised...
-
Making use of the fact that the Helmholtz free energy \(A(N, V, T)\) of a thermodynamic system is an extensive property of the system, show that \[ N\left(\frac{\partial A}{\partial N}ight)_{V,...
-
What is the mirror-image rule?
-
Under what circumstances is it appropriate to record goodwill in the accounts? How should goodwill , properly recorded on the books, be written off in order to conform with generally accepted...
-
Cash Receipt Schemes and Other Asset Misappropriations, identify and describe two big data and data analytic techniques each for detecting skimming, cash larceny, and noncash misappropriations.
-
Write HCL code for the signal need_valC in the SEQ implementation.
-
Which best describes the origin of life according to the data? (A) Life required an environment with atmospheric oxygen and any type of nucleic acids. (B) Life required an environment with...
-
Does your state have an inheritance/estate tax? If so, provide a brief summary indicating the tax rates and levels at which an estate/inheritance is taxed.
-
What is the definition of unconscionable?
-
Ruslan invents a light bulb that lasts longer than ordinary bulbs. To prevent others from making, using, or selling the bulb or its design, he should obtain a. a trademark. b. a copyright. c. a...
-
When can a person refuse to give information to law enforcement officers?
-
When is a contract in restraint of trade enforceable?
-
Mandy registers a domain name that is confusingly similar to the trademark of Security Services Corporation. She then offers to sell the domain name to Security Services. This is a. cybersquatting....
-
Beacher Motors specializes in producing one specialty vehicle. It is called Surfer and is styled to easily fit multiple surfboards in its back area and top-mounted storage racks. Beacher has the...
-
A supermarket chain is interested in exploring the relationship between the sales of its store-brand canned vegetables (y), the amount spent on promotion of the vegetables in local newspapers (x1)...
-
Assume we have created a packet-switched internet. Using the TCP/IP protocol suite, we need to transfer a huge file. What are the advantage and disadvantage of sending large packets?
-
A host communicates with another host using the TCP/IP protocol suite. What is the unit of data sent or received at each of the following layers? a. Application layer b. Network layer c. Data-link...
-
Assume a system uses five protocol layers. If the application program creates a message of 100 bytes and each layer (including the fifth and the first) adds a header of 10 bytes to the data unit,...
-
In 3 years you plan to invest $164 in an account that earns 11.1% compound interest per year. What is the value of your investment in 14 years from today? Round to the nearest cent.
-
Bond valuation-Semiannual interest Calculate the value of each of the bonds shown in the following table, all of which pay interest semiannually. (Click on the icon located on the top-right corner of...
-
IT's About Business 1.3 Information Technology Has the Potential for Revolutionizing Cuba In recent years, Cuba's private sector has been undergoing a huge transformation. Hundreds of thousands of...

Study smarter with the SolutionInn App


