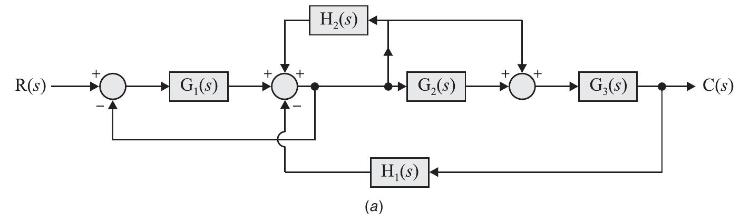
Find closed loop transfer function of systems shown in Fig. P3.4. (a), (b) and (c). R(S) G(s)
Question:
Find closed loop transfer function of systems shown in Fig. P3.4. (a), (b) and (c).
Transcribed Image Text:
R(S) G(s) H(s) G(s) H(s) (a) + G,(s) C(s)
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (QA)

Answered By

Rehab Rahim
I am well versed in communicating and teaching in areas of all business subjects. I have helped many students in different ways from answering answers to writing their academic papers.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Systems Analysis And Design questions
-
Suppose you accept your parents' offer of a 2017 BMW M6 convertible, but that's not the kind of car you want. Instead, you sell the car for AED200,000, spend AED80,000 on a used Corolla, and use the...
-
Solve the triangle, if possible. B 38 a 24 21 C
-
Solve the triangle, if possible. B 38 a 24 21 C
-
Using the aggregate expenditures table below, answer the questions that follow. a. Compute the APC when income equals $2,300 and the APS when income equals $2,800. b. Compute the MPC and MPS. c. What...
-
A small block with mass 0.250 kg is attached to a string passing through a hole in a frictionless, horizontal surface (see Fig. 10.48). The block is originally revolving in a circle with a radius of...
-
Conduct a follow-up analysis for the test in Exercise 49. Exercise 49. A survey by the National Institutes of Health asked a random sample of young adults (aged 19 to 25 years), Where do you live...
-
Amanda Forbes was hired as a nail technician by Showmann, Inc., in 2011. In 2017, Forbes attended a work-related holiday party where Showmann distributed raffle tickets to employees. One of the...
-
Effects of Stockholders Equity Transactions on the Balance Sheet The following transactions occurred at Horton Inc. during its first year of operation: a. Issued 100,000 shares of common stock at $5...
-
1. Find the mass of 3.02 x 10 19 atoms of arsenic, which has a molar mass of 74.9 g/mol. 2. Gold has a molar mass of 197 g/mol. (a) How many moles of gold are in a 3.03 g sample of pure gold? (b) How...
-
If all the system initial conditions are zero, find the Laplace transform of the output for given system inputs in Fig. P3.5. \[ \begin{aligned} & r_{1}(t)=3 e^{-t} \\ & r_{2}(t)=4 u(t) ; u(t) \text...
-
Reduce the diagram of Fig. P 3.3 to a single block. R(s) G(s) H(s) + G(s) H(s) G (s) H (s) Y(s)
-
Suppose that all young women were channeled into careers as secretaries, nurses, and teachers; at the same time, young men were encouraged to consider these three careers and many others as well. a....
-
Read scenarios one to four and determine the research design and strategy that you will use to address the research questions/ objectives. Please provide justifications for your decisions. 1. The...
-
What is the fundamental difference between attitudes and values and when communicating to effect change, which has a more powerful and long-term influence, attitude change or value change?
-
Sally needs to record a sales tax deposit of $375.23. What steps should she take to record this deposit? How they can be recorded in QBO.
-
How many hours would it take for 500 mL of intravenous (IV) solution to be delivered if it is flowing at 60 drops/ minute? This set is calibrated at 100 drops per mL.
-
answer the following questions. You can refer to external resources while answering questions. Q1. James is a scientist for a local manufacturer that employs a large percentage of the small town...
-
How is the fixed asset turnover ratio calculated, and what does the resulting ratio measure?
-
What is a content filter? Where is it placed in the network to gain the best result for the organization?
-
Consider the rt2.2 receiver in Figure 3.14, and the creation of a new packet in the se1f-ansition (i.e., the transition from the state back to itself) in the Waifor-0-from-below arid the...
-
Visit the Go-sack-N Java applet at the companion Web site. a. Have the source send five packets, and then pause the animation before any of the five packets reach the destination. Then kill the first...
-
A packet flow is said to conform to a leaky bucket specification (r, b) with burst size b and average rate r if the number of packets that arrive to the leaky bucket is less than n + b packets in...
-
Let's throw a coin three times. Let X be the number of crowns from the three throws. Let Y be the number of crowns from the first two tosses. Find the instantaneous code C from the set of values of...
-
What is the difference between add-ons and plug-ins? Explain a. Buffer overflow attack b. Integer overflow attack c. Heap Spray
-
What is Denial of Service (DoS)? What is the difference between DoS and Distributed Denial of Service (DDoS)? Explain a. Ping flood attack b. Smurf attack c. SYN flood attack

Study smarter with the SolutionInn App