A permutation on the set {1, . . . , k} is a one-to-one, onto function on
Question:
A permutation on the set {1, . . . , k} is a one-to-one, onto function on this set. When p is a permutation, pt means the composition of p with itself t times. Let
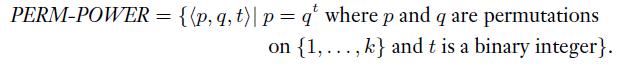
Show that PERM-POWER ∈ P. Note that the most obvious algorithm doesn’t run within polynomial time. First try it where t is a power of 2.
Transcribed Image Text:
PERM-POWER = {{p,q, t)| p = q' where p and q are permutations on {1, ..., k} and t is a binary integer}.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 73% (15 reviews)
To show that PERMPOWER P we need to give a polynomialtime algorithm that decides whether a given triple p q t is in PERMPOWER One way to approach this ...View the full answer

Answered By

Biplab Sutradhar
I'm a Master's in Computer Application with 10 years of experience in the Information Technology Industry and 5 years of experience as a home tutor. As a tutor, I have extensive hands-on experience in providing individualized instruction to students in a variety of subject areas. I am highly proficient in breaking down complex topics into smaller, more manageable pieces, and I have a strong ability to explain concepts in a clear and concise way. I am experienced in creating engaging learning activities and finding innovative ways to keep students engaged and motivated. I also have experience in developing individualized learning plans to meet the specific needs of each student. Additionally, I am an expert in providing feedback and guidance to help students reach their academic goals.
0.00
0 Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
A permutation block (P-box) in a modern block cipher is an example of a keyless transposition cipher. What does this statement mean? (See Figure 31.8 in the text.) Figure 31.8 2 3. 2 Straight...
-
In Figure 31.9, we have two straight permutation operations: initial permutation and final permutation. Experts believe these operations are useless and do not help to make the cipher stronger. Can...
-
A d-dimensional box with dimensions (x 1 , x 2 , . . . ,x d ) nests within another box with dimensions (y 1 , y 2 , . . . ,y d ) if there exists a permutation on {1, 2, . . . ,d} such that x (1) < y...
-
Two independent situations follow: 1. Ready Car Rental leased a car to Culver Company for three months. Terms of the lease agreement call for monthly payments of $885, beginning on May 21, 2024....
-
Instead of measuring only a single piece of DNA with the new method, 20 pieces are measured and 650 errors are found. Does the new method reduce the number of errors? A company develops a new method...
-
Can you tell me about a time when you had difficulty working with a customer or a colleague? What did you learn about yourself after you resolved the issue?
-
a. Run a regression of LNPAID on AGE. Is AGE a statistically significant variable? To respond to this question, use a formal test of hypothesis. State your null and alternative hypotheses,...
-
Over the past year, M. D. Ryngaert & Co. has realized an increase in its current ratio and a drop in its total assets turnover ratio. However, the companys sales, quick ratio, and fixed assets...
-
Image transcription text Assume a pumped hydro energy storage arrangement in which water is pumped up from a low-level water reservoir to a higher-level reservoir to store energy. The water then...
-
The following data were obtained from 3 separate enzyme kinetic experiments using 3 different substrates S1, S2 and S3 forming products P1, P2 and P3 respectively . The amount of enzyme in each...
-
Let Show that MODEXP P. (Note that the most obvious algorithm doesnt run in polynomial time. Try it first where b is a power of 2. MODEXP = {(a, b, c, p)| a, b, c, and p are positive binary integers...
-
Show that P is closed under the star operation. Use dynamic programming. On input y = y 1 y n for y i , build a table indicating for each i j whether the substring y i y j A * for any A P.)
-
What is the main disadvantage of daily forecasting using regression analysis?
-
What are the four major stress and health theories, and how are they different?
-
How do maladaptive mental health conditions manifest as a consequence of stressors at work?
-
How is worklife conflict different from worklife enrichment?
-
What do you think organizations can do to mitigate the micro-stressors that commonly affect employees?
-
Would a job costing system or a process costing system be used for this production process? Give specific reasons for your choice of which costing system would be most appropriate for this...
-
Boston Scientific Corporation (BSX) is a competitor of Kips Bay Medical (MBA 5-3). It was organized in 1979 and also develops, produces, and sells medical devices. The following data (in thousands)...
-
What are conversion costs? What are prime costs?
-
In CRC, which of the following generators (divisors) guarantees the detection of a single bit error? a. 101 b. 100 c. 1
-
Although it can be formally proved that the code in Table 10.3 is both linear and cyclic, use only two tests to partially prove the fact: Table 10.3 a. Test the cyclic property on codeword 0101100....
-
In CRC, if the dataword is 5 bits and the codeword is 8 bits, how many 0s need to be added to the dataword to make the dividend? What is the size of the remainder? What is the size of the divisor?
-
Compare life cover end funeral cover stating the advantages and disadvantages of each.
-
What are the change management issues in C 3 solutions?
-
What are 2 key events discussed in the documentary kanyi?

Study smarter with the SolutionInn App