For each of the following arguments, construct an indirect proof of validity. P: B [(OV~0) (TVU)] P:
Question:
For each of the following arguments, construct an indirect proof of validity.
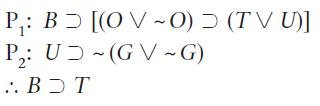
Transcribed Image Text:
P₁: B [(OV~0) (TVU)] P₂: UD~(GV-G) 2 :. BOT
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 55% (9 reviews)
B OV 0 TVU UD GV G 1 2 3 4 5 6 7 8 9 10 11 12 0 0B 13 OV O B BOT B...View the full answer

Answered By

ZIPPORAH KISIO LUNGI
I have worked on several other sites for more than five years, and I always handle clients work with due diligence and professionalism. Am versed with adequate experience in the fields mentioned above in which have delivered quality papers in research, thesis, essays, blog articles, and so forth.
I have gained extensive experience in assisting students to acquire top grades in biological, business and IT papers. Notwithstanding that, I have 7+ years of experience in corporate world software design and development.
5.00+
194+ Reviews
341+ Question Solved
Related Book For 

Introduction To Logic
ISBN: 9781138500860
15th Edition
Authors: Irving M. Copi, Carl Cohen, Victor Rodych
Question Posted:
Students also viewed these Social Science questions
-
For each of the following statements provide an indirect proof [as in part (2) of Theorem 2.4] by stating and proving the contrapositive of the given statement. (a) For all integers k and l, if kl is...
-
For each of the following arguments, construct an indirect proof of validity. P: (GVH) G ~G
-
Write a program that finds a contiguous subarray of length at most \(m\) in an array of \(n\) long integers that has the highest average value among all such subarrays, by trying all subarrays. Use...
-
Refer to Apples financial statements in Appendix A to answer the following. 1. Identify the note that reports on Apples business segments. 2. Describe the focus and activities of each of Apples...
-
A CSTR Is used to produce a specialty chemical. The reaction is exothermic and exhibits first-order kinetics. .Laboratory analyses for the product quality are time consuming, requiring several hours...
-
The collar has a weight of \(50 \mathrm{lb}\) and falls from rest down the titanium bar. If the bar has a diameter of 0.5 in., determine the maximum stress developed in the bar if the weight is (a)...
-
Kaiwan, Inc., a calendar year S corporation, is partly owned by Sharrod, whose beginning stock basis is $32,000. During the year, Sharrods share of a Kaiwan long-term capital gain (LTCG) is $5,000,...
-
Like wars and socio-politic shifts, contagious diseases have changed the economics and politics of the world throughout history. In 2020, the world faced COVID-19, a globally effective virus leading...
-
Cusic Music Company is considering the sale of a new sound board used in recording studios. The new board would sell for $26,400, and the company expects to sell 1,500 per year. The company currently...
-
The following set of arguments involves, in each case, one inference only, in which one of the ten logical equivalences set forth in this section has been employed. Here are two examples, the first...
-
Use Conditional Proof to prove the validity of the following arguments. G (P): (HD) (P): (CD) (E > F) (P): G (CVE) (P): (DVF) (HVD) :. G = (DVF)
-
Is it inevitable that employees will respond to change with feelings of fear? If you believe the answer is yes, state the implications of this for managing strategic change. If you believe the answer...
-
Assuming the clowns database exists and contains one empty table named clowns, what is the output of the following? A. The code terminates successfully without any output. B. The code does not...
-
Which is true if the clowns database exists and contains an empty clowns table? A. The code compiles and prints 0 without error. B. The code compiles and prints 1 without error. C. The code does not...
-
Given the following two classes, what change to the StealSecret class would allow it to read and email the password to a hacker? A. There are no changes, as the Secret class is secure. B. Override...
-
Suppose we have a peacocks table with two columns: name and rating. What does the following code output if the table is empty? A. false B. true C. The code does not compile due to line s1. D. The...
-
Why is a journal referred to as the book of original entry?
-
What volume of 3.99 M H2SO4 is needed to obtain 4.61 mol of H2SO4?
-
The Ferris wheel in the figure has a radius of 68 feet. The clearance between the wheel and the ground is 14 feet. The rectangular coordinate system shown has its origin on the ground directly below...
-
All war zones are places where abuse of discretion is rampant. Some places where abuse of discretion is rampant are international borders. Therefore, some international borders are war zones. Use the...
-
All inside traders are people subject to prosecution. Some executives with privileged information are not people subject to prosecution. Therefore, some executives with privileged information are...
-
All successful flirts are masters at eye contact. All masters at eye contact are people genuinely interested in others. Therefore, some people genuinely interested in others are successful flirts....
-
What is the firm appears to have used financial leverage most effectively in enhancing the rate of ROCE? Explain your reasoning.
-
What is output given the user input? >3 blind mice System.out.print("Enter info: "); Scanner keyboard = new Scanner(System.in); String info = keyboard.nextLine(); Scanner inputScnr = new...
-
Given the code below fill in the blanks. 5 => LRStack() s.push('foo') s.push('bar') s.top() s.push('baz') s.pop() s.push('bat') The stack has elements. is at the top of the stack. is second from the...

Study smarter with the SolutionInn App