Research the Koch Snowflake online then, using the techniques you learned in Section 18.9, implement an application
Question:
Research the Koch Snowflake online then, using the techniques you learned in Section 18.9, implement an application that draws the Koch Snowflake.
Transcribed Image Text:
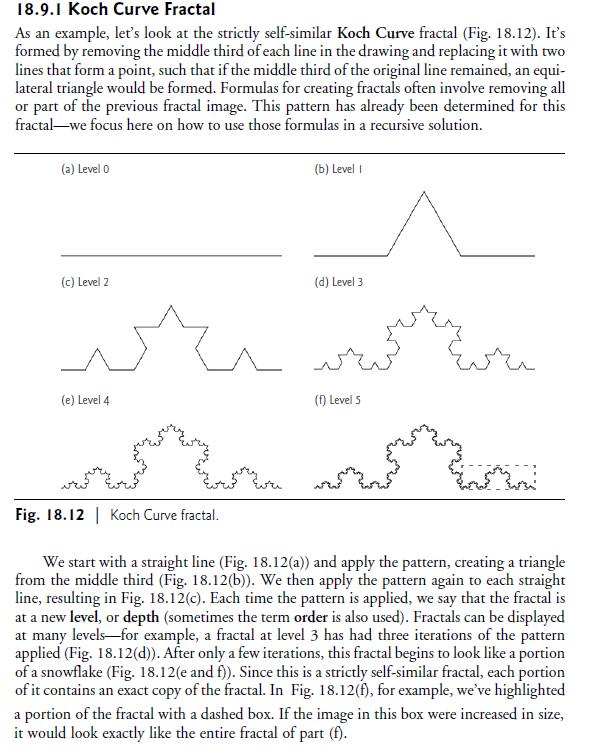
18.9.1 Koch Curve Fractal As an example, let's look at the strictly self-similar Koch Curve fractal (Fig. 18.12). It's formed by removing the middle third of each line in the drawing and replacing it with two lines that form a point, such that if the middle third of the original line remained, an equi- lateral triangle would be formed. Formulas for creating fractals often involve removing all or part of the previous fractal image. This pattern has already been determined for this fractal we focus here on how to use those formulas in a recursive solution. (a) Level 0 (c) Level 2 (e) Level 4 Fig. 18.12 | Koch Curve fractal. (b) Level I (d) Level 3 (f) Level S or w We start with a straight line (Fig. 18.12(a)) and apply the pattern, creating a triangle from the middle third (Fig. 18.12(b)). We then apply the pattern again to each straight line, resulting in Fig. 18.12(c). Each time the pattern is applied, we say that the fractal is at a new level, or depth (sometimes the term order is also used). Fractals can be displayed at many levels for example, a fractal at level 3 has had three iterations of the pattern applied (Fig. 18.12(d)). After only a few iterations, this fractal begins to look like a portion of a snowflake (Fig. 18.12(e and f)). Since this is a strictly self-similar fractal, each portion of it contains an exact copy of the fractal. In Fig. 18.12(f), for example, we've highlighted a portion of the fractal with a dashed box. If the image in this box were increased in size, it would look exactly like the entire fractal of part (f).
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (1 review)
The Koch Snowflake is a mathematical curve and one of the earliest fractal curves to have been described It is built by starting with an equilateral t...View the full answer

Answered By

Charles mwangi
I am a postgraduate in chemistry (Industrial chemistry with management),with writing experience for more than 3 years.I have specialized in content development,questions,term papers and assignments.Majoring in chemistry,information science,management,human resource management,accounting,business law,marketing,psychology,excl expert ,education and engineering.I have tutored in other different platforms where my DNA includes three key aspects i.e,quality papers,timely and free from any academic malpractices.I frequently engage clients in each and every step to ensure quality service delivery.This is to ensure sustainability of the tutoring aspects as well as the credibility of the platform.
4.30+
2+ Reviews
10+ Question Solved
Related Book For 

Java How To Program Late Objects Version
ISBN: 9780136123712
8th Edition
Authors: Paul Deitel, Deitel & Associates
Question Posted:
Students also viewed these Computer science questions
-
Using the techniques you learned in Section 18.9, implement an application that draws the Koch Curve. 18.9.1 Koch Curve Fractal As an example, let's look at the strictly self-similar Koch Curve...
-
Write a literature review for your study. See below for an example of a literature review. Your literature review should provide both analysis and synthesis of previous studies as related to the...
-
THIRD AVENUE SOFTWARE HEALTH-CARE APP PROJECT This case is new for the ninth edition of Information Technology Project Management . The case provides an opportunity to apply agile and Scrum...
-
Because the entries in the present value table (Table 13 - 3) are reciprocals of the corresponding entries in the future value table (Table 13 - 1), how can Table 13 - 3 be used to find the future...
-
Omar Morena, a fellow student, contends that the double entry system means that each transaction must be recorded twice. Is Omar correct? Explain.
-
Using the following partial listing of T accounts, prepare closing entries in general journal form dated January 31, 20--. Then post the closing entries to the Taccounts. Accum. Depr.- Del. Equip....
-
Standard atmospheric air \(\left(T_{0}=59^{\circ} \mathrm{F}, p_{0}=14.7 \mathrm{psia} ight)\) is drawn steadily through a frictionless and adiabatic converging nozzle into an adiabatic, constant...
-
Target Corporation prepares its financial statements according to U.S. GAAP. Targets financial statements and disclosure notes for the year ended February 3, 2018, are available in Connect. This...
-
Research the civil case Katz, et al. v. Panera Bread Co. and answer the following questions: Give a brief description of the lawsuit. Did Panera properly display the contents of the drink? Explain...
-
Using the String-processing capabilities, the file and directory capabilities and a Map, create an application that recursively walks a directory structure supplied by the user and reports the number...
-
Enhance the Fibonacci program of Fig. 18.5 so that it calculates the approximate amount of time required to perform the calculation and the number of calls made to the recursive method. For this...
-
In Figure 11.13, the X, Y, and Z coordinates (in feet) of station A are 1816.45, 987.39, and 1806.51, respectively, and those of B are 1633.11, 1806.48, and 1806.48, respectively. Determine the...
-
In strict terms, speed is a scalar and velocity is a vector. True False
-
A baseball with a mass of 137 g is thrown horizontally with a speed of 39.3 m/s (88 mi/h) at a bat. The ball is in contact with the bat for 1.00 ms and then travels straight back at a speed of 46.0...
-
A spy satellite traveling at 0.6c (so that y=1.25) records a top-secret handoff that lasts 2.5s according to the camera on the satellite. How long does the hand off take according to the spies on...
-
In a cooling isobaric process of steam the dew point temperature is: The temperature at which the isobaric curve intercept the limit curve of steam-water at steam quality equal to zero; The...
-
budget can be defined as a financial plan for the future period of time. Thus, it sets out the intentions which management has for the period concerned. Required: Explain the 5 ( Five ) distinct...
-
Your class has volunteered to work for Referendum 13 on the November ballot, which calls for free tuition and books for all college courses except operations management. Support for the referendum...
-
Compare and contrast licensing and subcontracting.
-
Which of the four digital-to-analog conversion techniques (ASK, FSK, PSK or QAM) is the most susceptible to noise? Defend your answer.
-
We have a baseband channel with a 1-MHz bandwidth. What is the data rate for this channel if we use each of the following line coding schemes? a. NRZ-L b. Manchester c. MLT-3 d. 2B1Q
-
What is the maximum data rate of a channel with a bandwidth of 200 KHz if we use four levels of digital signaling.
-
Beginning inventory Merchandise Finished goods Cost of merchandise purchased Cost of goods manufactured Ending inventory Merchandise Finished goods Unimart Bare Manufacturing $ 316,000 $ 632,000...
-
a. Briefly explain 3 advantages of using input/output files in programming. (3 marks) b. Write C++ statements that allow you to enter 50 employees data that consists of an staf ID, name and their...
-
Consider the following Haskell code length:: [a] > Int length [] = 0 length (x:xs) = 1 + length xs decision::Bool -> Bool -> Int decision True _ = 0 - decision True = 1 decision = 26 -- Assume that...

Study smarter with the SolutionInn App


