Using Figure 3-31 as a guide, write a structural Verilog description for the fulladder circuit in Figure
Question:
Using Figure 3-31 as a guide, write a structural Verilog description for the fulladder circuit in Figure 3-58. Compile and simulate your description. Apply all eight input combinations to check the correction function of your description.
Figure 3-31
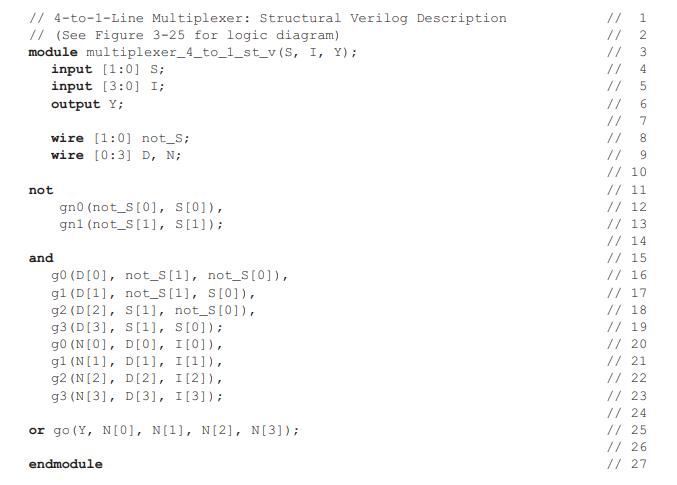
Figure 3-58
Transcribed Image Text:
// 4-to-1-Line Multiplexer: Structural Verilog Description // (See Figure 3-25 for logic diagram) module multiplexer_4_to_1_st_v (S, I, Y); input [1:0] S; input [3:0] I; output Y; wire [1:0] not_S; wire [0:3] D, N; not and gno (not_S[0], s[0]), gn1 (not_S [1], S[1]); g0 (D [0], not_S [1], gl (D[1], not_s [1], s[0]), g2 (D[2], S[11], not_S[0]), g3 (D[3], S[1], S[0]); g0 (N[0], D[0], I[0]), g1 (N[1], D[1], I[1]), g2 (N[2], D[2], I[2]), g3 (N[3], D[3], I [3]); or go (Y, N[0], N[1], N[2], N[3]); not_S[0]), endmodule // // // 11 // 1234 o 5 7 // // 9 // 10 // 11 // 12 // 13 // 14 // 15 // 16 // 17 // 18 // 19 // 20 // 21 // 22 // 23 // 24 // 25 // 26 // 27
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 50% (2 reviews)
It appears that there is a misunderstanding or error as the images shown do not correspond to Figure ...View the full answer

Answered By

Krishnavendra Y
I am a self motivated financial professional knowledgeable in; preparation of financial reports, reconciling and managing accounts, maintaining cash flows, budgets, among other financial reports. I possess strong analytical skills with high attention to detail and accuracy. I am able to act quickly and effectively when dealing with challenging situations. I have the ability to form positive relationships with colleagues and I believe that team work is great key to performance. I always deliver quality, detailed, original (0% plagiarism), well-researched and critically analyzed papers.
5.00+
4+ Reviews
10+ Question Solved
Related Book For 

Logic And Computer Design Fundamentals
ISBN: 9780133760637
5th Edition
Authors: M. Morris Mano, Charles Kime, Tom Martin
Question Posted:
Students also viewed these Computer science questions
-
Using Figure 3-28 as a guide, write a structural VHDL description for the full-adder circuit in Figure 3-58. Compile and simulate your description. Apply all eight input combinations to check the...
-
Using Figure 2-46 as a framework, write a structural Verilog description of the circuit in Figure 2-43. Replace X, Y, and Z with input [2:0] X. Compile and simulate your Verilog model for all eight...
-
Compile and simulate the behavioral description of the 4-bit adder in Figure 3-51. Assuming a ripple carry implementation, apply all eight input combinations to check out the rightmost full adder....
-
discuss the benefits and challenges of the employee job performance evaluation process as it relates to the ratings of an individual. For example, if an employer uses a standard Likert Scale (1...
-
How might you use IR spectroscopy to distinguish among the three isomers 1 -butyne, 1, 3-hutadiene, arid 2-butyne?
-
At the time of Robert Grangers death, his estate consisted of the following assets and liabilities measured at fair market value: Assets Cash .. .... .. . . .. . .. .. .. .. .. .. . .. . . .. .. . ....
-
Water is flowing through a long pipe of diameter \(15 \mathrm{~cm}\) at \(300 \mathrm{~K}\). The pressure gradient is \(500 \mathrm{~Pa} / \mathrm{m}\). Using the Blasius equation for the friction...
-
1. Outline an internal control program that could be installed that would prevent or at least disclose irregularities such as those identified in this case. 2. Outline an internal audit program that...
-
You create a new project roadmap that is visually appealing and contains all the information for the stakeholders to reference. However, this document took a lot of time to create and has caused some...
-
Compile and simulate the 4-bit adder in Figures 3-47 and 3-48. Apply combinations that check out the rightmost full adder for all eight input combinations; this also serves as a check for the other...
-
Design two versions of the combinational circuit whose input is a 4-bit number and whose output is the 2s complement of the input number, for each of the following cases using AND, OR, and NOT gates:...
-
Persian Rugs needs $600 million to support growth next year. If it issues new common stock to raise the funds, the flotation (issuance) costs will be 4 percent. If Persian can issue stock at $125 per...
-
Discuss ways in which you could apply the lessons learned in Chapter 13 to improve your ability to read people. Provide specific examples to support your response.
-
The beta of firm A is 1.5 and the beta of firm B is 0.5. What is the difference in returns between firm A and B if the market risk premium is 6%?
-
Suppose that someone's taxable income is $ 4 2 , 6 0 0 they're married but finally separately due to their partners immigration status calculate their taxes and show your work.
-
Answer the following questions with reference to the contiguous sequential representation of a complete binary tree: 1. How do you find the right child of node at A[i]? 2. In an array representing a...
-
what did you learn about yourself from reading the other theories of personality? List and explain at least three things.
-
The Turing test is a hypothetical test to determine whether a computer system has reached the level of artificial intelligence. If the computer can fool a person into thinking it is another person,...
-
TRUE OR FALSE: 1. Banks with a significantly large share of fixed-interest rate home loans are less exposed to interest rate risks. 2. Although Australian banks are pretty big, they are not...
-
Consider two network entities. A and B. which are connected by a perfect hi-directional channel (i.e., any message sent will he received correctly: the channel will not corrupt, lose, or re-order...
-
Suppose two TCP connections are present over some bottleneck link of rate R bps. Both connections have a huge tile to send (in the same direction over the bottleneck link. The transmissions of the...
-
Suppose an application uses rdt. 3.0 as its transport layer protocol. As the stop-and-wait protocol has very low channel utilization (shown in the cross- country example), the designers of this...
-
Explain about the FED's policy toolkit. Also, delineate the process through which the FED's conduct open market operations.
-
The Web is rapidly becoming the major medium through which people communicate, make decisions, and even construct their social identities. Think about the difference this has on the effects of...
-
Hongyi has decided to change his investment strategy. Instead of holding the property forever, he will sell it after ten years. The property currently has a market value of $750,000. Hongyi expects...

Study smarter with the SolutionInn App


