Using the procedure given in Section 1-7, find the hexadecimal Gray code.
Question:
Using the procedure given in Section 1-7, find the hexadecimal Gray code.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (QA)
To find the hexadecimal Gray code we can follow the procedure outlined in Section 17 The Gray ...View the full answer

Answered By

David Ngaruiya
i am a smart worker who concentrates on the content according to my clients' specifications and requirements.
4.50+
7+ Reviews
19+ Question Solved
Related Book For 

Logic And Computer Design Fundamentals
ISBN: 9780133760637
5th Edition
Authors: M. Morris Mano, Charles Kime, Tom Martin
Question Posted:
Students also viewed these Computer science questions
-
Using the procedure given in Problem 33, compute the probability that at least 2 people in a room of 23 people share the same birthday.
-
Case Study: Quick Fix Dental Practice Technology requirements Application must be built using Visual Studio 2019 or Visual Studio 2017, professional or enterprise. The community edition is not...
-
File to edit sprintf ~~~~~~~~~~~~~~~~~ #sprintf! #$a0 has the pointer to the buffer to be printed to #$a1 has the pointer to the format string #$a2 and $a3 have (possibly) the first two substitutions...
-
Provide an overview of the OS and the manufacturer What is the footprint for the selected OS? What security architecture was implemented? How many CVEs does this OS have?
-
How would you prepare the following compounds from toluene? A diazonio replacement reaction is needed in someinstances. (a) (b) (c) NH2 CH2NH2 H
-
Discuss the realism of the underlying assumptions of break-even analysis (that is, how likely it is that the assumptions will hold in reality).
-
Consider the air pollution and mortality data given in Problem 3.15 and Table B. 15 . Problem 3.15 McDonald and Ayers [1978] present data from an early study that examined the possible link between...
-
1. Convert your ERD to a domain class diagram. 2. Develop a use case diagram. 3. Create a fully developed use case description or an activity diagram for each use case. 4. Develop a system sequence...
-
Island Telephone Corporation issued a $240,000 face value bond on March 21, 1989, carrying a 9.25% coupon and 25 years to maturity. Global Financial Services purchased the bond on March 21, 1996, at...
-
(a) List the 6-bit binary number equivalents for 32 through 47 with a parity bit added in the rightmost position, giving odd parity to the overall 7-bit numbers. (b) Repeat for even parity.
-
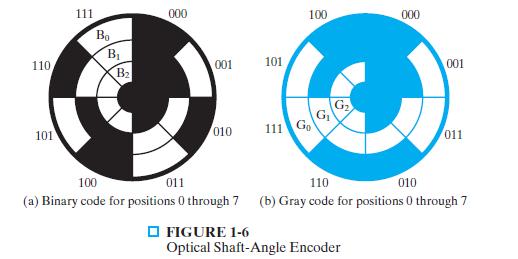
This problem concerns wind measurements made by the wireless weather station in Example 1-1. The wind direction is to be measured with a disk encoder like the one shown in Figure 1-6(b). (a) Assuming...
-
Repeat Prob. 10-96 assuming an isentropic efficiency of 84 percent for the turbines and 100 percent for the pumps. Prob. 10-96 Consider an ideal reheat-regenerative Rankine cycle with one open...
-
What are ways to draft policies and procedures that are to be implement into a corporate policy specific to a law firm. Identify steps to show compliance with these specific policies and procedures. ?
-
What strategies can managers implement to enhance cultural awareness and overcome preconceived biases or stereotypes?
-
A monkey's ear ring experiences an electric field force of 1 2 N in the presence of an external electric field of 3 0 0 0 0 N / C . The electric force is opposite to the electric field. What is the...
-
How do demographic shifts, such as aging populations and urbanization, reshape social structures and demand innovative approaches to address emerging societal needs, such as healthcare, housing, and...
-
In general partnerships, every partner has the statutory right to participate in the management of the partnership. a. Why do you think limited partners are prohibited in the management of the...
-
a. Wotan owns 1,000 shares of a firm that has just announced an increase in its dividend from $2.00 to $2.50 a share. The share price is currently $150. If Wotan does not wish to spend the extra...
-
Find the radius of convergence in two ways: (a) Directly by the CauchyHadamard formula in Sec. 15.2. (b) From a series of simpler terms by using Theorem 3 or Theorem 4.
-
In this exercise, we will look at the different ways capacity affects overall performance. In general, cache access time is proportional to capacity. Assume that main memory accesses take 70 ns and...
-
This exercise examines the impact of different cache designs, specifically comparing associative caches to the direct-mapped caches from Section 5.4. For these exercises, refer to the address stream...
-
Mean Time Between Failures (MTBF), Mean Time To Replacement (MTTR), and Mean Time To Failure (MTTF) are useful metrics for evaluating the reliability and availability of a storage resource. Explore...
-
In the cookie Kit determine how many "materials' are needed to create the kit. Be sure to provide a detailed list. Consider how these materials are sourced and used. Discuss in your own words, the...
-
3. What is stored in numList after the following code executes? (15 Points) int numList[6] = {25, 37, 62, 78, 92, 13}; int *listPtr = numList; int *temp = listPtr + 2; int num; *listPtr = *(listPtr +...
-
The Natural Resources Defense Council's November 2007 Report stated, "Although there are some exceptions, in most cases, locally produced food proves the best choice for minimizing global warming and...

Study smarter with the SolutionInn App


