In Sec. 4.8.4, it was pointed out that it would be better to search for holes for
Question:
In Sec. 4.8.4, it was pointed out that it would be better to search for holes for the text and data segments separately. Implement this improvement.
Data from Sec. 4.8.4
Transcribed Image Text:
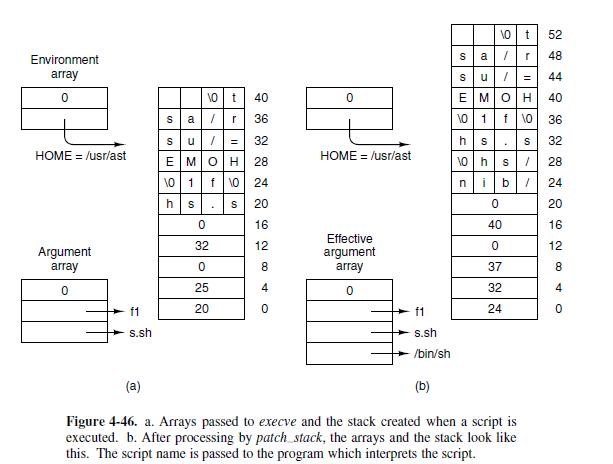
The code for exec follows the outline of Fig. 4-40. It is contained in the pro- cedure do_exec (line 18747) in exec.c. After making a few validity checks, the PM fetches the name of the file to be executed from user space (lines 18773 to 18776). Recall that the library procedures which implement exec build a stack within the old core image, as we saw in Fig. 4-38. This stack is fetched into the PM's memory space next (line 18782). The next few steps are written as a loop (lines 18789 to 18801). However, for ordinary binary executables only one pass through the loop takes place. We will first describe this case. On line 18791 a message to the file system switches to the user's directory so the path to the file will be interpreted relative to the user's, rather than to PM's, working directory. Then allowed is called-if execution is allowed it opens the file. If the test fails a negative number is returned instead of a valid file descriptor, and do exit terminates indicating failure. If the file is present and executable, the PM calls read_header and gets the segment sizes. For an ordinary binary the return code from read header will cause an exit from the loop at line 18800. Now we will look at what happens if the executable is a script. MINIX 3, like most UNIX-like operating systems, supports executable scripts. Read_header tests the first two bytes of the file for the magic shebang (#!) sequence and returns a special code if this is found, indicating a script. The first line of a script marked this way specifies the interpreter for the script, and possibly also specifies flags and options for the interpreter. For instance, a script can be written with a first line like
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 83% (6 reviews)

Answered By

GERALD KAMAU
non-plagiarism work, timely work and A++ work
4.40+
6+ Reviews
11+ Question Solved
Related Book For 

Operating Systems Design And Implementation
ISBN: 9780131429383
3rd Edition
Authors: Andrew Tanenbaum, Albert Woodhull
Question Posted:
Students also viewed these Computer science questions
-
Hyten Corporation On June 5, 1998, a meeting was held at Hyten Corporation, between Bill Knapp, Director of Marketing/Sales, and John Rich, director of engineering. The purpose of the meeting was to...
-
In this chapter it was pointed out that market geography is subject to changes. Why should the channel manager be concerned with such changes?
-
For years, Dell's seemingly magical power to squeeze efficiencies out of its supply chain and drive down costs made it a darling of the financial markets. Now we learn that the magic was at least...
-
1. List five line coding schemes discussed in this book. 2. Define block coding and give its purpose. 3. Define scrambling and give its purpose. 4. Compare and contrast PCM and DM 5. What are the...
-
Elegant Outdoor Furniture Company included the following stockholders equity on its year-end balance sheet at February 28, 2011: Stockholders' Equity Preferred stock, 6.5% cumulative par value $35...
-
Your employees are breaking into ethnically based cliques. Members of ethnic groups eat together, socialize together, and often chat in their native languages while they work. You appreciate how...
-
Table B. 14 contains data concerning the transient points of an electronic inverter. Fit a regression model to all 25 observations but only use \(x_{1}-x_{4}\) as the regressors. Investigate this...
-
On January 1, 2011, Burleson Corporation's projected benefit obligation was $30 million. During 2011 pension benefits paid by the trustee were $4 million. Service cost for 2011 is $12 million....
-
Brite Toothbrushes has gathered the following Information to complete its Production Report for the month of April. Assume all materials are added at the beginning of the process. Required: Using the...
-
If an instruction takes 1 nsec and a page fault takes an additional n nsec, give a formula for the effective instruction time if page faults occur every k instructions.
-
Now revisit the previous question using a hole list. How much memory is needed for the list in the best case and in the worst case? Assume the operating system occupies the bottom 512 KB of memory.
-
(a) What is the difference between the Arrhenius and the Brnsted-Lowry definitions of an acid? (b) NH3(g) and HCl(g) react to form the ionic solid NH4Cl(s). Which substance is the Brnsted-Lowry acid...
-
Answer the questions in Exercise 1.17, this time assuming that the quantities purchased are 12 loaves of bread, 6 pounds of meat, and 2 gallons of milk. Exercise 1.17 Table 1.15 shows the prices of...
-
You have access to the following rates: Current spot exchange rate: \($0.0100\)/yen Current 180-day forward exchange rate: \($0.0105\)/yen 180-day U.S. interest rate (on dollar-denominated assets):...
-
Table 1.15 shows the prices of three items in 2000 and 2010. a. Construct a price index that is equal to 100 in 2000. What is the value of your index in 2010? What is the percentage change in your...
-
Create flowcharts or storyboards to illustrate the first-time experience of a player. Know how you will direct players, show them benefits, reward them quickly and move them into more complex...
-
Table 1.14 shows data on four apparel price indexes that are used to compute the CPI. Explain why you either agree or disagree with these statements: a. Mens apparel cost more than womens apparel in...
-
Dorsey Corporation purchased 90% of the common stock of Lansing Company on January 1, 2002. The cost of the investment was equal to the book value interest acquired. Lansing Company operates two...
-
In Problem 8.43, determine the smallest value of for which the rod will not fall out of the pipe. IA -3 in.-
-
Calculate 1.666015625 10 0 (1.9760 10 4 + -1.9744 10 4 ) by hand, assuming each of the values are stored in the 16-bit half precision format described in Exercise 3.27 (and also described in the...
-
Calculate (1.666015625 10 0 1.9760 10 4 ) + (1.666015625 10 0 -1.9744 10 4 ) by hand, assuming each of the values are stored in the 16-bit half precision format described in Exercise 3.27 (and...
-
Based on your answers to 3.38 and 3.39, does (1.666015625 10 0 1.9760 10 4 ) + (1.666015625 10 0 -1.9744 10 4 ) = 1.666015625 10 0 (1.9760 10 4 + -1.9744 10 4 )?
-
Describe how marketing management and metrics assist service organisations in implementing and measuring their marketing strategy.
-
Maslow and Herzberg may view the relationship between the extrinsic and intrinsic factors somewhat differently. Which theory best aligns with your approach to creating a motivating climate for staff ?
-
Rajiv is a member of market research team. His boss observes his work on specific aspects of his job (client calls, conducting meetings, attending seminars, etc. and writes down using specific...

Study smarter with the SolutionInn App