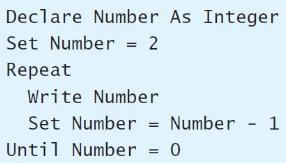
Draw a flowchart for the pseudocode in Exercise 13. Data from Exercise 13 Declare Number As Integer
Question:
Draw a flowchart for the pseudocode in Exercise 13.
Data from Exercise 13
Transcribed Image Text:
Declare Number As Integer Set Number = 2 Repeat Write Number Set Number = Number - 1 %3D Until Number = 0 %3D
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 40% (5 reviews)
Start Yes Nu...View the full answer

Answered By

PALASH JHANWAR
I am a Chartered Accountant with AIR 45 in CA - IPCC. I am a Merit Holder ( B.Com ). The following is my educational details.
PLEASE ACCESS MY RESUME FROM THE FOLLOWING LINK: https://drive.google.com/file/d/1hYR1uch-ff6MRC_cDB07K6VqY9kQ3SFL/view?usp=sharing
3.80+
3+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Draw a flowchart for the pseudocode in Exercise 15. Data from Exercise 15 Declare Number As Integer Set Number = 2 While Number != 0 Write Number Set Number Number - 1 End While
-
Draw a flowchart for a process of interest to you, such as a quick oil-change service, a factory process you might have worked in, ordering a pizza, renting a car or truck, buying products on the...
-
Draw a flowchart corresponding to the pseudocode in Exercise 35. Data from Exercise 35 Write pseudocode that will average a list of numbers input by the user. Use the following variables: Number As...
-
Have I done this correctly? In case you were wondering what experiment I was doing, it is the magic milk experiment about how food color moves away from the dish soap in a bowl of milk. EPS Unit 1...
-
Consider the spring and mass shown in Figure 3.3 where M = 1 kg, k = 100 N/m, and b = 20 Ns/m. (a) Find the state vector differential equation. (b) Find the roots of the characteristic equation for...
-
Use the outline for the BPP provided in Figure 5-9 to present the system specifications for the information system you chose for Problem and Exercise 5-35. Problem and Exercise 5-35. Consider your...
-
Water flows down the sloping ramp shown in Fig. P3.123 with negligible viscous effects. The flow is uniform at sections (1) and (2). For the conditions given show that three solutions for the...
-
1. If the variable cost per unit goes up, Contribution margin Break-even point a. Increases increases. b. Increases decreases. c. Decreases decreases. d. Decreases increases. e. Decreases remains...
-
32) Refer to the drawing of an elevated centrifugal pump taking suction from the bottom of an open storage tank containing water at 66F (see figure below). Assume standard atmospheric pressure. The...
-
A ride hailing company has their DB structured in 3 major tables as described in the SCHEMA section below. Write a query to fetch the top 100 users who traveled the most distance using the service....
-
Give the output of the loop in Exercise 15. Data from Exercise 15 a. Is this loop a pre-test loop or a post-test loop? b. List the statements in the body of the loop. c. What is the test condition...
-
Consider the following counter-controlled loop: What is the name of the counter variable? Give the values of the initial value, the increment, and the limiting value. Declare K As Integer For (K =...
-
Determine whether g or g (or neither) for the functions (x) = log 10 x and g(x) = ln x.
-
Why is it difficult to convict organized crime leaders?
-
With regard to tax avoidance and tax evasion, which of the following is most accurate? 1. Tax evasion is another term for tax fraud. 2. Tax avoidance and tax evasion are essentially the same...
-
What are the means by which cybercriminals meet and agree to participate in such an activity?
-
E-discovery rules were developed primarily with regard to what communication technology? 1. Telephone communications, including faxes 2. Sending and receiving emails 3. Downloading of e-books, using...
-
How many birthdays does the average person have?
-
The file Sedans contains the overall miles per gallon (MPG) of 2015 midsized sedans: a. Compute the mean, median, and mode. b. Compute the variance, standard deviation, range, coefficient of...
-
Why can wastewater treatment requirements in Hawaii be less stringent than those in most locations on the U.S. mainland?
-
Suppose Alice and Bob are communicating over an SSL session. Suppose an attacker, who does not have any of the shared keys. Inserts a bogus TCP segment into a packet stream with correct TCP checksum...
-
What is the purpose of the random nonces in the SSL handshake?
-
In Section 8.6. 1, it is shown that without sequence numbers, Trudy (a woman- in-the middle) can wreak havoc in an SSL session by interchanging TCP segments. Can Trudy do something similar by...
-
Golden Gate Mining Co. (GGMC) currently has a gold mine operating in Canada and is looking to purchase another gold mine in Peru, operating as Inca Gold Inc. (ICI). You currently work for the CFO at...
-
Cokolo Inc. has entered into the following two derivatives contracts: Purchased put options on 1,000 Trenton Co. shares that have an exercise price of $52 per share and expire in 60 days Negotiated a...
-
As a financial manager (consultant), undertake an investigation on your allocated company to evaluate its strategic financial position. Prepare a business report for the board of directors of the...

Study smarter with the SolutionInn App