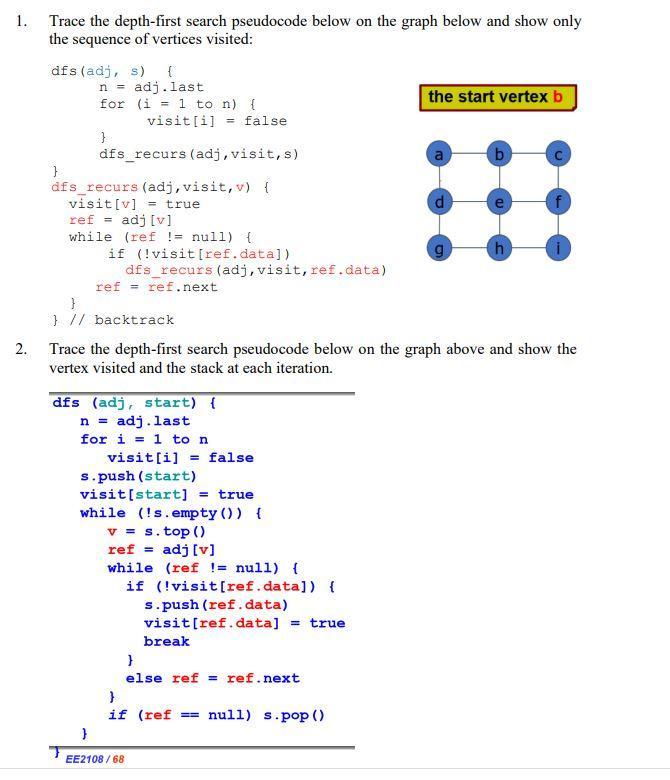
1. 2. Trace the depth-first search pseudocode below on the graph below and show only the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
1. 2. Trace the depth-first search pseudocode below on the graph below and show only the sequence of vertices visited: dfs (adj, s) { } n = adj.last for (i =1 to n) { } visit[i]= false dfs_recurs (adj, visit, s) dfs_recurs (adj, visit, v) { visit [v] = true ref = adj [v] while (ref !=null) { if (!visit [ref. data]) dfs_recurs (adj, visit, ref.data) ref= ref.next } } // backtrack dfs (adj, start) { n = adj. last for i=1 to n visit[i]= false Trace the depth-first search pseudocode below on the graph above and show the vertex visited and the stack at each iteration. s.push (start) visit [start] = true while (!s. empty()) { v=s.top () ref adj [v] while (ref != null) { if (!visit[ref.data]) { s.push (ref.data) visit[ref.data] = true } EE2108/68 break } else ref = ref.next } if (ref the start vertex b null) s.pop() b h 1. 2. Trace the depth-first search pseudocode below on the graph below and show only the sequence of vertices visited: dfs (adj, s) { } n = adj.last for (i =1 to n) { } visit[i]= false dfs_recurs (adj, visit, s) dfs_recurs (adj, visit, v) { visit [v] = true ref = adj [v] while (ref !=null) { if (!visit [ref. data]) dfs_recurs (adj, visit, ref.data) ref= ref.next } } // backtrack dfs (adj, start) { n = adj. last for i=1 to n visit[i]= false Trace the depth-first search pseudocode below on the graph above and show the vertex visited and the stack at each iteration. s.push (start) visit [start] = true while (!s. empty()) { v=s.top () ref adj [v] while (ref != null) { if (!visit[ref.data]) { s.push (ref.data) visit[ref.data] = true } EE2108/68 break } else ref = ref.next } if (ref the start vertex b null) s.pop() b h
Expert Answer:
Answer rating: 100% (QA)
To trace the depthfirst search DFS on the graph using the provided pseudocode well start from node b ... View the full answer

Related Book For 

Data Structures and Algorithms in Java
ISBN: 978-1118771334
6th edition
Authors: Michael T. Goodrich, Roberto Tamassia, Michael H. Goldwasser
Posted Date:
Students also viewed these algorithms questions
-
A leading manufacturer of watches maintains a set of very exclusive networks of retailers that are authorized to sell its watches. Recently, however, there has been pressure on the company (by...
-
Can you try to define the liquidity of stocks quantitatively? (It means how to measure the liquidity.) How can we improve the liquidity of stocks?
-
Case Study: Quick Fix Dental Practice Technology requirements Application must be built using Visual Studio 2019 or Visual Studio 2017, professional or enterprise. The community edition is not...
-
A quality control manager at a manufacturing facility has taken four samples with four observations each of the diameter of a part. (a) Compute the mean of each sample. (b) Compute an estimate of the...
-
Sections of the trans-Alaska pipeline run above the ground and are supported by vertical steel shafts (k = 25 W/m K) that are 1 m long and have a cross-sectional area of 0.005 m2. Under normal...
-
' n Janet Foster bought a computer and printer at Computerland. The printer had a $600 list price with a $100 trade discount and 10 30 terms. The computer had a $1,600 list price with a 25% trade...
-
Saturated steam at \(55^{\circ} \mathrm{C}\) is to be condensed at a rate of \(10 \mathrm{~kg} / \mathrm{h}\) on the outside of a vertical tube of diameter \(3 \mathrm{~cm}\) by maintaining the...
-
The balance sheet of Terrier Company at the end of 2009 is presented here, along with certain other information for 2010: December 31, 2009 Cash ................ $ 140,000 Accounts receivable...
-
QS 12-4 (Static) Indirect: Computing cash flows from operations LO P2 Cain Incorporated reports net income of $15,000. Its comparative balance sheet shows the following changes: accounts receivable...
-
Provide the following for the following challenge exercise: a) Income Statement, Gross Margin Standard, year-to-date b) All Journal Entries c) Customer Aged Detail, all customers, with terms at Mar...
-
Today is June 1. Sustainable Corporation has an obligation of $25 million coming due on August 1. The company is planning to borrow this amount on August 1 to fulfill its obligation, and plans to pay...
-
The amount of electricity used in a typical all-electric home is shown in the circle graph in Figure 14.15. If, in a certain month, a home used 1,100 kWh (kilowatt-hours), find the amounts of...
-
Decide whether something is wrong with each of the graphs shown in Problems 13-17. Explain your reasoning. Consider the graph shown in Figure 14.20. Chevy trucks are clearly better. 95% CHEVY FORD...
-
Refer to P46. During 2008, the following events occurred: 1. Silly Inc. had sales of $800,000 to Practical Corp. Sillys gross margin was still 40% of selling price, and its income tax rate continued...
-
A professor gives six exams. Two students' scores have the same mean, although one student's scores have a small standard deviation and the other student's scores have a large standard deviation....
-
The diameter of a pipe is normally distributed, with a mean of 0.4 inch and a variance of 0.0004 . What is the probability that the diameter of a randomly selected pipe will exceed 0.41 inch?
-
1) Draw the other significant resonance contributor for the following compound; include lone pairs of electrons, formal charges, and hydrogen atoms. 2) Add curved arrows to both structures to show...
-
For the vector whose polar components are (Vr = 1, Vθ = 0), compute in polars all components of the second covariant derivative Vα;μ;ν. To find...
-
Suppose we have an n-element list L maintained according to the move-to-front heuristic. Describe a sequence of n 2 accesses that is guaranteed to take (n 3 ) time to perform on L.
-
Our quick-select implementation can be made more space-efficient by initially computing only the counts for sets L, E, and G, and creating only the new subset that will be needed for recursion....
-
Let T be a tree with n positions. Define the lowest common ancestor (LCA) between two positions p and q as the lowest position in T that has both p and q as descendants (where we allow a position to...
-
Demonstrate that for colors \(r, g\), and \(b\), color \(\mathrm{SU}(3)\) two-quark states are of the form \(q q=\mathbf{3} \otimes \mathbf{3}=\mathbf{6} \oplus \overline{\mathbf{3}}\), with Show...
-
Verify the color SU(3) representations for combinations of three or fewer quarks and antiquarks given in Eq. (19.28). Data from Eq. 19.28 qq=303=108 qq 3 3 603, 999 3 3 3 = 36315, qqq 3 3 3 1088 10,
-
Prove that Eq. (19.34) gives the simplest multi-gluon and gluon-quark states that contain an \(\mathrm{SU}(3)\) color singlet in the decomposition. Data from Eq. 19.34 (GG)1: (88)1 (Gqq) : [8 (383)8]...

Study smarter with the SolutionInn App