In this problem, we will give another proof that the set of connectives {-, A, V}...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
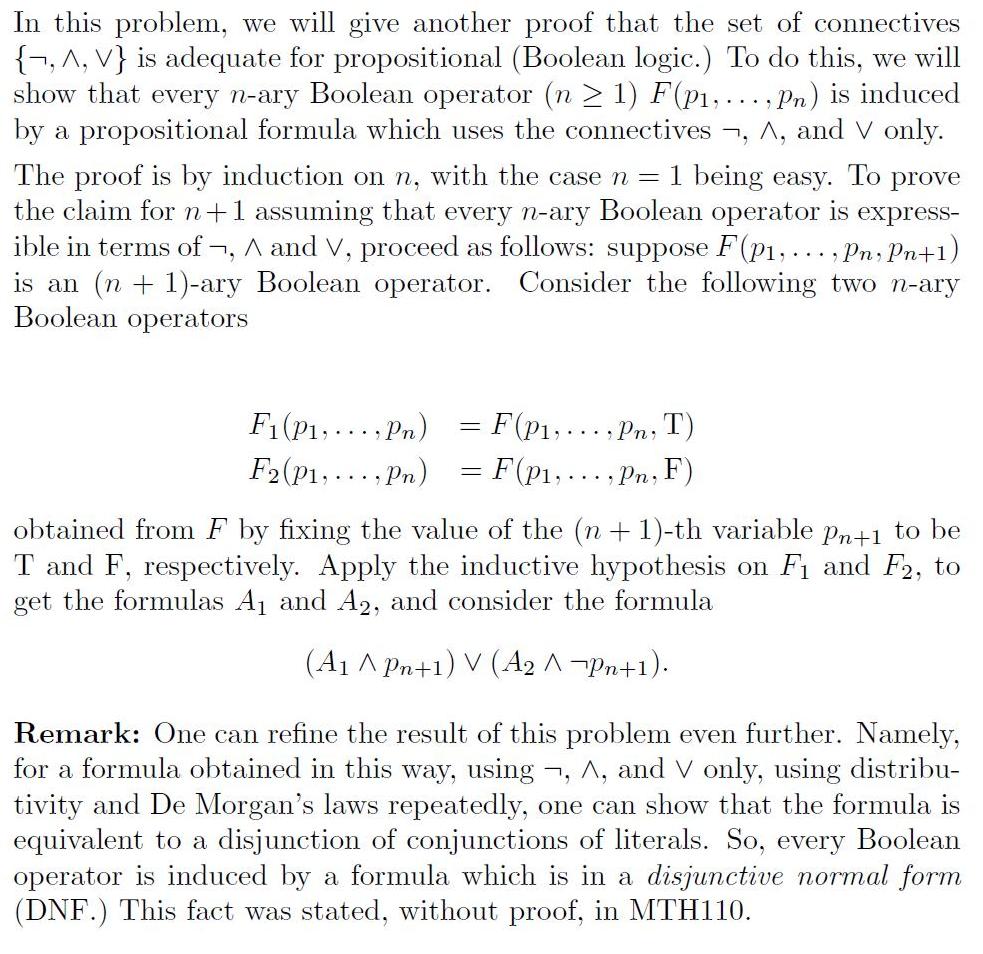
In this problem, we will give another proof that the set of connectives {-, A, V} is adequate for propositional (Boolean logic.) To do this, we will show that every n-ary Boolean operator (n > 1) F(p1,..., Pn) is induced by a propositional formula which uses the connectives , A, and V only. The proof is by induction on n, with the case n = 1 being easy. To prove the claim for n+1 assuming that every n-ary Boolean operator is express- ible in terms of ¬, A and V, proceed as follows: suppose F(p1,..., Pn, Pn+1) is an (n + 1)-ary Boolean operator. Consider the following two n-ary Boolean operators F1(P1, ... , Pn) = F(p1;...,Pn, T) F2(P1, ..., Pn) = F(p1,..., Pn, F) obtained from F by fixing the value of the (n+ 1)-th variable pn+1 to be T and F, respectively. Apply the inductive hypothesis on F1 and F2, to get the formulas A1 and A2, and consider the formula (A1 ^ Pn+1) V (A2 A-Pn+1). Remark: One can refine the result of this problem even further. Namely, for a formula obtained in this way, using tivity and De Morgan's laws repeatedly, one can show that the formula is equivalent to a disjunction of conjunctions of literals. So, every Boolean operator is induced by a formula (DNF.) This fact was stated, without proof, in MTH110. -, A, and V only, using distribu- S. hich in a disjunctive normal form In this problem, we will give another proof that the set of connectives {-, A, V} is adequate for propositional (Boolean logic.) To do this, we will show that every n-ary Boolean operator (n > 1) F(p1,..., Pn) is induced by a propositional formula which uses the connectives , A, and V only. The proof is by induction on n, with the case n = 1 being easy. To prove the claim for n+1 assuming that every n-ary Boolean operator is express- ible in terms of ¬, A and V, proceed as follows: suppose F(p1,..., Pn, Pn+1) is an (n + 1)-ary Boolean operator. Consider the following two n-ary Boolean operators F1(P1, ... , Pn) = F(p1;...,Pn, T) F2(P1, ..., Pn) = F(p1,..., Pn, F) obtained from F by fixing the value of the (n+ 1)-th variable pn+1 to be T and F, respectively. Apply the inductive hypothesis on F1 and F2, to get the formulas A1 and A2, and consider the formula (A1 ^ Pn+1) V (A2 A-Pn+1). Remark: One can refine the result of this problem even further. Namely, for a formula obtained in this way, using tivity and De Morgan's laws repeatedly, one can show that the formula is equivalent to a disjunction of conjunctions of literals. So, every Boolean operator is induced by a formula (DNF.) This fact was stated, without proof, in MTH110. -, A, and V only, using distribu- S. hich in a disjunctive normal form
Expert Answer:
Answer rating: 100% (QA)
When n1 then we have a unary operator and it can be represented usin... View the full answer

Posted Date:
Students also viewed these programming questions
-
In this problem we consider annual U.S. lumber production over 30 years. The data were obtained from the U.S. Department of Commerce Survey of Current Business and are presented in Table 16.5 a. Plot...
-
In this problem we consider sending real-time voice from Host A to Host B over a packet-switched network (VoIP). Host A converts analog voice to a digital 64 kbps bit stream on the fly. Host A then...
-
In this problem we will visit United Rentals Inc. (URI), which was introduced at the beginning of the chapter. The following table shows the monthly return on URI stock and on the S&P 500 stock index...
-
The operations of Balloons Ltd. generated the following data for its current December 31 taxation year: Business losses (150,000) Dividends received and deducted (Division C) 25,000 Bond interest...
-
Use the forecast errors given here to compute MAD and MSE. Discuss the information yielded by each type of error measurement. Period .... e 1 ...... 2.3 2 ...... 1.6 3 ..... -1.4 4 ..... 1.1 5 .......
-
In the public-key authentication protocol of Fig. 8-43, in message 7, RB is encrypted with KS. Is this encryption necessary, or would it have been adequate to send it back in plaintext? Explain your...
-
Online processing is most useful for which of these tasks? a. preparing payroll checks b. reconciling job-time tickets and time cards c. paying payroll tax obligations d. making changes in employee...
-
Peachtree Company uses a sales journal, a purchases journal, a cash receipts journal, a cash disbursements journal, and a general journal. The following transactions occur in the month of May. May 1...
-
Hint(s) Check My Work Eastman Publishing Company is considering publishing an electronic textbook about spreadsheet applications for business. The fixed cost of manuscript preparation, textbook...
-
A. Richard McCarthy (born 2/14/64; Social Security number 100-10-9090) and Christine McCarthy (born 6/1/1966; Social security number 101-21-3434) have a 19-year-old son (born 10/2/99 Social Security...
-
Question A : Can you explain to me the theory of attribution and the two types of factors I need to take into account when managing a team? do fast and neeed correct answer answer with should be in...
-
Explain the relationship of (1) emotional feelings and (2) commitment in a persons emotional response.
-
What does it mean to have an emotional understanding of other people?
-
What would be the appropriate operating system architecture for the: (a) Inertial measurement system (b) Nuclear monitoring system (c) Patient monitoring system (d) Airline reservations system (e)...
-
What functions are performed in effective groups? Illustrate how a breakdown in one of these functions can jeopardize the success of the other functions. As your example for class discussion, use the...
-
Show with an example that EDF is no longer an optimal scheduling policy if preemption is not allowed.
-
7 The maximum sum You are given an integer N and an integer array a of N elements. You can decrease the elements of the array multiple times. You have to make the array non-decreasing. In all such...
-
A local politician is concerned that a program for the homeless in her city is discriminating against blacks and other minorities. The following data were taken from a random sample of black and...
-
Eden Development Company has two competing investments. Proposal A and Proposal B. Proposals A and B have an initial investment of $175,000. The net cash flows estimated for the two investments are...
-
Pyramid Construction Company is planning an investment of \($174,000\) for a bulldozer. The bulldozer is expected to operate for 1,400 hours per year for five years. Customers will be charged \($80\)...
-
Financial statement data is utilized by a variety of user-groups to include a companys board of directors, bondholders, corporate employees and executives, customers, investment advisors, labor...

Study smarter with the SolutionInn App

