2. Consider the following figure showing TCP congestion window size as a function of the transmission...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
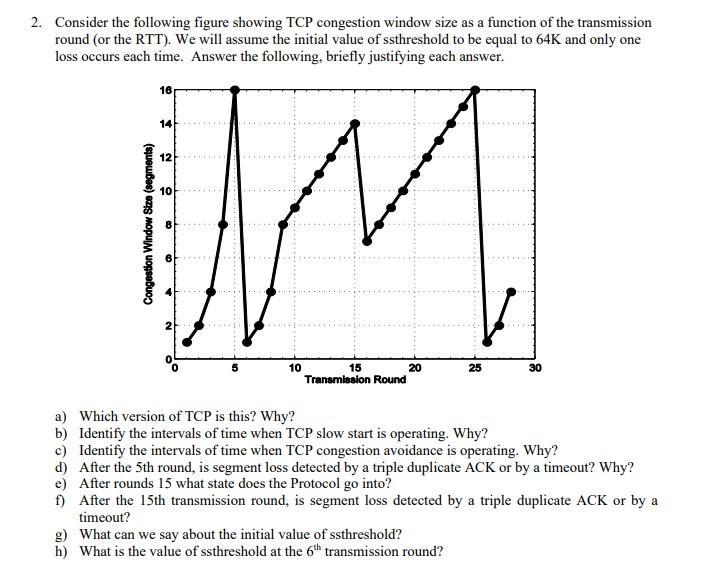
2. Consider the following figure showing TCP congestion window size as a function of the transmission round (or the RTT). We will assume the initial value of ssthreshold to be equal to 64K and only one loss occurs each time. Answer the following, briefly justifying each answer. Congestion Window Size (segments) 16 14 12 10 B 10 *** 15 Transmission Round 20 25 g) What can we say about the initial value of ssthreshold? h) What is the value of ssthreshold at the 6th transmission round? 30 a) Which version of TCP is this? Why? b) Identify the intervals of time when TCP slow start is operating. Why? c) Identify the intervals of time when TCP congestion avoidance is operating. Why? d) After the 5th round, is segment loss detected by a triple duplicate ACK or by a timeout? Why? e) After rounds 15 what state does the Protocol go into? f) After the 15th transmission round, is segment loss detected by a triple duplicate ACK or by a timeout? 2. Consider the following figure showing TCP congestion window size as a function of the transmission round (or the RTT). We will assume the initial value of ssthreshold to be equal to 64K and only one loss occurs each time. Answer the following, briefly justifying each answer. Congestion Window Size (segments) 16 14 12 10 B 10 *** 15 Transmission Round 20 25 g) What can we say about the initial value of ssthreshold? h) What is the value of ssthreshold at the 6th transmission round? 30 a) Which version of TCP is this? Why? b) Identify the intervals of time when TCP slow start is operating. Why? c) Identify the intervals of time when TCP congestion avoidance is operating. Why? d) After the 5th round, is segment loss detected by a triple duplicate ACK or by a timeout? Why? e) After rounds 15 what state does the Protocol go into? f) After the 15th transmission round, is segment loss detected by a triple duplicate ACK or by a timeout?
Expert Answer:
Answer rating: 100% (QA)
a This is TCP Reno Because the packet loss detection is triggered by 3 du... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these programming questions
-
Consider Figure 3.58. Assuming TCP Reno is the protocol experiencing the behavior shown above, answer the following questions. In all cases, you should provide a short discussion justifying your...
-
What is the Passive communication Style ? Example of Passive communication Style? Passive communication Style: Positive Impact on Communication? Passive communication Style: Negative Impact on...
-
Describe what this statement does: print user name = + userName
-
You are auditing the December 31, 2019, financial statements of Hockney plc, manufacturer of novelties and party favors. During your inspection of the company garage, you discovered that a used...
-
Tiny Toddlers, a manufacturer of childrens toys and furniture, is designing and implementing a distributed system to assist its sales force. Each of the 10 sales offices in Canada and 20 in the...
-
This exercise considers data from the Medical Expenditure Panel Survey (MEPS), conducted by the U.S. Agency of Health Research and Quality. MEPS is a probability survey that provides nationally...
-
On June 1, 2011, MacDougall Corporation approached Silverman Corporation about purchasing a parcel of undeveloped land. Silverman was asking $240,000 for the land and MacDougall saw that there was...
-
What is the yield to maturity of a corporate bond that has a coupon rate of 5%, a face value of $1,000, a present value of $574.32, and a time to maturity of 20 years?
-
5. Assume that there is a dipole p = p(t) 2 at the origin. (a) Show the charge density and current density, p = -p(t) - V8(F) and j = p 8(F), describe the dipole. (Hint: You can use V2, = -plen,...
-
Go to the Web. Locate your states criminal statutes. Examine your states gun control laws. In your judgment, are these laws too permissive or too restrictive? Are any of these statutes susceptible to...
-
Go to the web. Locate your states criminal statutes (or another states if yours are not available online). Determine whether your state uses Model Penal Code terminology (purposely, knowingly,...
-
Go to http://www.findlaw.com/casecode/supreme.html. Locate the Supreme Courts decision in United States v. Ramirez, decided March 4, 1998. Read the decision. Write a brief summary of the decision in...
-
Use www.findlaw.com or some other Internet resource to locate the U.S. Supreme Courts most recent decisions in the areas of arrest and interrogation. Try to determine whether the Court has agreed to...
-
Go to the Court TV website at http://www.courtv.com. Follow Court TVs coverage of a current trial. Write a memorandum to your instructor summarizing the major factual and legal issues before the...
-
Hector has two residential rental properties that are mortgaged. Both properties are in Class 1 with a CCA rate of 4 percent. At the beginning of the year, Property A has a UCC of $650,000 and...
-
What mass of KBr (in grams) should you use to make 350.0 mL of a 1.30 M KBr solution?
-
Provide a filter table and a connection table for a stateful firewall that is restrictive as possible but accomplishes the following: a. Allows all internal users to establish Telnet sessions with...
-
Consider again the figure for P21. a. Assume a priority service, with packets 1,4, 5, 6, and 11 being highpriority packets. The remaining packets are low priority. Indicate the slots in which packets...
-
Consider Figure S.38 in problem P14. Provide MAC addresses and IP addresses for the interfaces at Host A, both routers, and Host F. Suppose Host A sends a datagram to Host F. Give the source and...
-
Longfellow Ranch in Pecos County, Texas. While Amerimex would usually provide mobile bunkhouses for its crews on site, the present contract required them to locate the bunkhouses 30 miles north in...
-
T-Mobile customers with qualifying plans can participate in a promotional service called T-Mobile Tuesdays, which offers free items and discounts from various well-known stores. Messages are sent...
-
Frankie and Trena Gibbs and Joel and Madeira Glenn were members of the Creek Baptist Church. On Saturday, May 31, 2008, the Gatlin Creek Baptist Church, which both couples had attended, held a...

Study smarter with the SolutionInn App


