(9 points) Consider sending a large amount of data over a lossy link. Each bit can...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
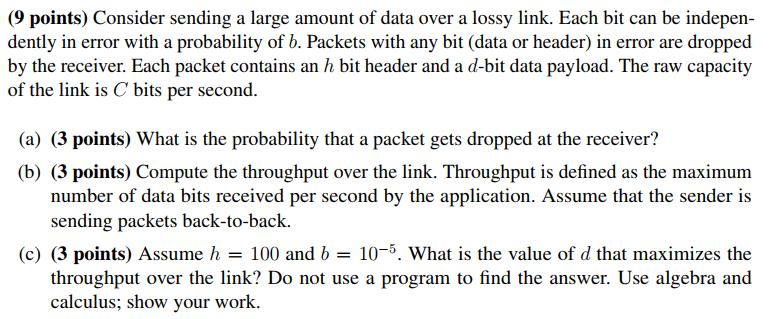
(9 points) Consider sending a large amount of data over a lossy link. Each bit can be indepen- dently in error with a probability of b. Packets with any bit (data or header) in error are dropped by the receiver. Each packet contains an h bit header and a d-bit data payload. The raw capacity of the link is C bits per second. (a) (3 points) What is the probability that a packet gets dropped at the receiver? (b) (3 points) Compute the throughput over the link. Throughput is defined as the maximum number of data bits received per second by the application. Assume that the sender is sending packets back-to-back. (c) (3 points) Assume h = 100 and b = 10-5. What is the value of d that maximizes the throughput over the link? Do not use a program to find the answer. Use algebra and calculus; show your work. (9 points) Consider sending a large amount of data over a lossy link. Each bit can be indepen- dently in error with a probability of b. Packets with any bit (data or header) in error are dropped by the receiver. Each packet contains an h bit header and a d-bit data payload. The raw capacity of the link is C bits per second. (a) (3 points) What is the probability that a packet gets dropped at the receiver? (b) (3 points) Compute the throughput over the link. Throughput is defined as the maximum number of data bits received per second by the application. Assume that the sender is sending packets back-to-back. (c) (3 points) Assume h = 100 and b = 10-5. What is the value of d that maximizes the throughput over the link? Do not use a program to find the answer. Use algebra and calculus; show your work.
Expert Answer:
Answer rating: 100% (QA)
The solutions of above question is as follows a Number of bits dh Probability of each bit being erro... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these programming questions
-
Define access control lists and capabilities, and discuss their relative strengths and weaknesses. [5 marks] Describe how the access control list mechanisms work in Unix. You have been asked to build...
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
Analyzing Revenues and Expenses and Completing an Income Statement Neighborhood Realty, Incorporated, has been operating for three years and is owned by three investors. S. Bhojraj owns 60 percent of...
-
This assignment is designed to introduce you to the preparation of both a one-variable and a two-variable "data table" in Excel 2010. Such tables are useful for conducting and reporting the results...
-
The dotplot generated below by the One Proportion applet assumed the long-run proportion of winning was equal to 50%. Use this dotplot to answer the following questions. a. How many dots are in the...
-
In 2014, Barker contacted Price about a van Price had advertised for sale. The advertisement described the van as a 1994 Ford E350. Barker and Price agreed to meet, and, on April 9, Barker inspected...
-
Some special handling devices can be obtained for $12,000. At the end of 4 years, they can be sold for $600. Compute the depreciation schedule for the devices using the following methods: (a)...
-
Traditionally, Hobbits have relied on private provision for their schooling. As the newly elected mayor of the Shire, Samwise Gamgee has decided to launch a public schooling option. The typical...
-
Loss in translation? Plus By entering your nearest bookstore. Without a doubt, you will find a wide section of dedicated books to the management and management of human behavior. A close look at the...
-
Explain the history between NHL and the Olympics sides in the negotiation you selected. Identify the chief negotiators/committee (by name and title) representing each side of NHL and the Olympics...
-
You want to conduct primary customer research. Describe two types of primary research and their purpose.
-
1. Determine tan and in the diagram to the nearest hundredth. Answer: (5) (1, 0) X (1, -3.73) 2. The path of a swing could be modelled by the function,
-
Explain how search and rescue operations are coordinated with other fire suppression operations. Identify the factors to evaluate during a search and rescue size-up. Explain how fire fighters...
-
Common Stock $ 72,000 Furniture $ 48,000 Insurance Expense 600 Research Expense 3,000 Accounts Payable 4,000 Dividends 5,400 Service Revenue 80,000 Utilities Expense 500 Building 132,000 Accounts...
-
The ABC Ltd. manufactures superior motherboards that are used in a variety of computers. The Motherboard Division (M Division) sells its motherboard both internally and externally. It is operating at...
-
4. Jobe dy -Y 2 et by
-
Suppose two nodes, A and B, are attached to opposite ends of an 800 m cable, and that they each have one frame of I,SOO bits (including all headers and preambles) to send to each other. Both nodes...
-
Consider the figure below, which shows a leaky bucket policer being fed by a stream of packets. The token buffer can hold at most two tokens, and is initially full at t =O. New tokens (uTive at a...
-
Consider the chaining example discussed at the end of Section 6.7.2. Suppose a mobile user visits foreign networks A, B, and C, and that a correspondent begins a connection to the mobile user when it...
-
Show that the Lorentz group commutation relations (13.20) are satisfied by the choices \(K_{i}= \pm \frac{i}{2} \sigma_{i}\) and \(J_{i}=\frac{1}{2} \sigma_{i}\), where the \(\sigma_{i}\) are Pauli...
-
Find the relationship of the eight SU(3) operators \(T_{ \pm}, V_{ \pm}, U_{ \pm}, T_{3}\), and \(Y\) defined in Eqs. (8.2) and (8.7)-(8.8), and the nine oscillator operators \(\left(A_{i}^{j}...
-
Verify that the set of matrices (5.14) is closed under ordinary matrix multiplication. Data from Eq. 5.14 T(oc)= = 629 > - (+19) TOO) = (721) TO) = ( ). T(oa)= T(b) TO) -(11) T(4-(11) TO=(9) T(C3)= =

Study smarter with the SolutionInn App


