After carefully utilizing the reading material above. Write a qualitative risk assessment report. Your risk assessment should
Fantastic news! We've Found the answer you've been seeking!
Question:
 After carefully utilizing the reading material above. Write a qualitative risk assessment report. Your risk assessment should include all discovered vulnerabilities and a qualitative risk assessment.
After carefully utilizing the reading material above. Write a qualitative risk assessment report. Your risk assessment should include all discovered vulnerabilities and a qualitative risk assessment.
Transcribed Image Text:
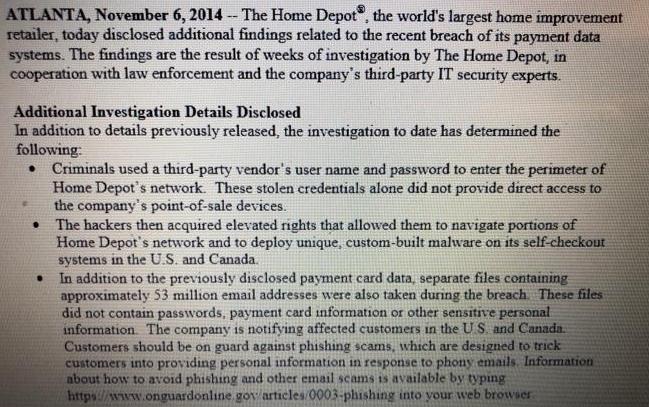
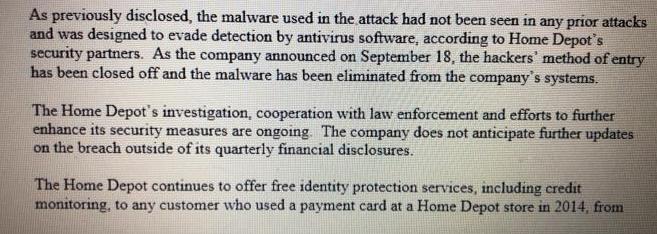
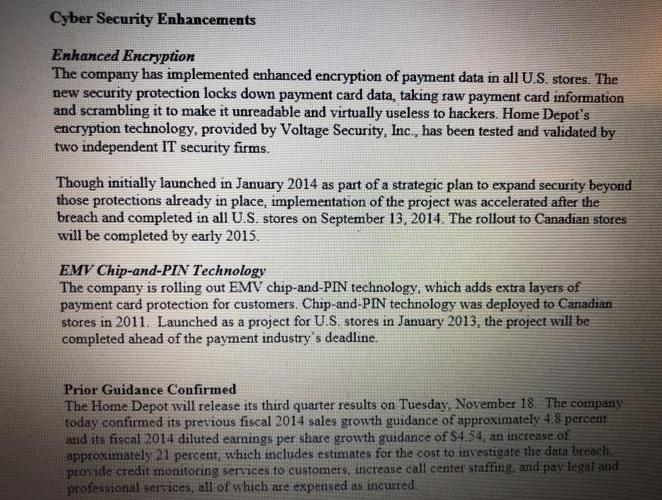
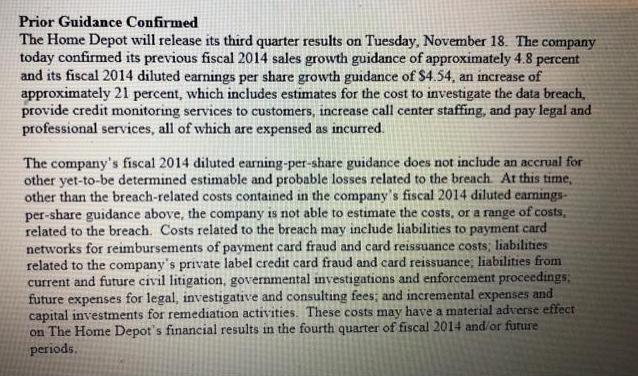
ATLANTA, November 6, 2014 -- The Home Depot, the world's largest home improvement retailer, today disclosed additional findings related to the recent breach of its payment data systems. The findings are the result of weeks of investigation by The Home Depot, in cooperation with law enforcement and the company's third-party IT security experts. Additional Investigation Details Disclosed In addition to details previously released, the investigation to date has determined the following: • Criminals used a third-party vendor's user name and password to enter the perimeter of Home Depot's network. These stolen credentials alone did not provide direct access to the company's point-of-sale devices. ● . The hackers then acquired elevated rights that allowed them to navigate portions of Home Depot's network and to deploy unique, custom-built malware on its self-checkout systems in the U.S. and Canada. In addition to the previously disclosed payment card data, separate files containing approximately 53 million email addresses were also taken during the breach. These files did not contain passwords, payment card information or other sensitive personal information. The company is notifying affected customers in the US and Canada. Customers should be on guard against phishing scams, which are designed to trick customers into providing personal information in response to phony emails. Information about how to avoid phishing and other email scams is available by typing https://www.onguardonline gov/articles/0003-phishing into your web browser. ATLANTA, November 6, 2014 -- The Home Depot, the world's largest home improvement retailer, today disclosed additional findings related to the recent breach of its payment data systems. The findings are the result of weeks of investigation by The Home Depot, in cooperation with law enforcement and the company's third-party IT security experts. Additional Investigation Details Disclosed In addition to details previously released, the investigation to date has determined the following: • Criminals used a third-party vendor's user name and password to enter the perimeter of Home Depot's network. These stolen credentials alone did not provide direct access to the company's point-of-sale devices. ● . The hackers then acquired elevated rights that allowed them to navigate portions of Home Depot's network and to deploy unique, custom-built malware on its self-checkout systems in the U.S. and Canada. In addition to the previously disclosed payment card data, separate files containing approximately 53 million email addresses were also taken during the breach. These files did not contain passwords, payment card information or other sensitive personal information. The company is notifying affected customers in the US and Canada. Customers should be on guard against phishing scams, which are designed to trick customers into providing personal information in response to phony emails. Information about how to avoid phishing and other email scams is available by typing https://www.onguardonline gov/articles/0003-phishing into your web browser.
Expert Answer:
Answer rating: 100% (QA)
Home Depot Data Breach Report This report covers Home Deport data breach vulnerabilities and risk as ... View the full answer

Related Book For 

Auditing and Assurance Services A Systematic Approach
ISBN: 978-1259162343
9th edition
Authors: William Messier, Steven Glover, Douglas Prawitt
Posted Date:
Students also viewed these banking questions
-
For this assignment, first think about your major or career goals. What is something that you'd like to learn more about in your future courses? Then, use the NLU University Library to find a book or...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
In Problems 1318, express the graph shown in blue using interval notation. Also express each as an inequality involving x. -1 0 1 2 3
-
Construct truth tables for the given statement forms? 1. p (q 2. ( (p (q) (p (q) 3. (p (q) q 4. (p q) (p (q)
-
Payroll liability and payroll taxes go together. Whats the nature of payroll liability for the employer? What are the typical journal entries for payroll, payroll liability and payroll taxes? You can...
-
When no heat energy is allowed to enter or leave a system, the system is called a/an (a) Isothermal system (b) Reversible system (c) Adiabatic system (d) Irreversible system.
-
1. What four characteristics of deep ecology does Guha list? 2. What are his criticisms of the four? 3. Why does he think the emphasis on wilderness preservation is harmful? 4. What problems does he...
-
What are the following SQL Server Administration and Management Tools used for?(3 Marks) SQL Server Configuration Manager SQL Server Profiler SQL Server Agent What is the purpose of the...
-
Jim Andrews opened a delivery business in March. He rented a small office and has a part-time assistant. His trial balance shows accounts for the first three months of business. Andrews' transactions...
-
Match the correct functional area with it responsibilities. a. Responsible for disseminating incident situation information to the incident commander (IC), and prepares the incident action plan (IAP)...
-
Max Gruber graduated from university 6 years ago with a finance undergraduate degree. Although he is satisfied with his current job, his goal is to become an investment banker. He feels that an MBA...
-
Using the same firm you selected for question 8, make a list of the firms strategic assets. How does each of its strategic assets strengthen its business model? Question 8 Select one of the following...
-
Brenda Wilson owns a restaurant chain named Rhapsody Cuisine. She is planning to expand her chain from 9 restaurants to 15. Brenda is now working to put together a set of pro forma financial...
-
You believe that household income in a country has a mean of around $40,000 with a standard deviation of about $30,000. How large a sample should you take if you want the width of a 95 percent...
-
Martinez Company incurred the following costs during 2015 in connection with its research and development activities. Instructions Compute the amount to be reported as research and development...
-
Suppose that a monopolist faces the following inverse demand curve for its product: p = 50 - 2q where p is the price of the product and q is the quantity of the product. The monopolist incurs a...
-
Subprime loans have higher loss rates than many other types of loans. Explain why lenders offer subprime loans. Describe the characteristics of the typical borrower in a subprime consumer loan.
-
List the three categories of GAAS. Discuss why the GAAS and the SAS are considered minimum standards of performance for auditors.
-
The first element in managements process for assessing the effectiveness of internal control is determining which controls should be tested. Identify the controls that would typically be tested by...
-
Dean Wareham, an audit manager, is preparing a proposal for a publicly held company in the manufacturing industry. The potential client is growing rapidly and introducing many new products yet still...
-
An orthotropic AS/3501 carbon/epoxy lamina (see Tables 2.2 and 4.1) is subjected to the plane stress condition \(\sigma_{x}=1000 \mathrm{MPa}, \sigma_{y}=50 \mathrm{MPa}\), and \(\tau_{x y}=50...
-
Determine the longitudinal tensile strength of the hybrid carbon/aramid/ epoxy composite described in Problem 3.4 and Figure 3.10 of Chapter 3 if the fiber packing array is square with the closest...
-
Compare and discuss the estimated longitudinal compressive strengths of Scotchply 1002 E-glass/epoxy based on (a) fiber microbuckling and (b) transverse tensile rupture. Assume linear elastic...

Study smarter with the SolutionInn App