An attacker can use a method named Port Scanning to examine which ports are open on...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
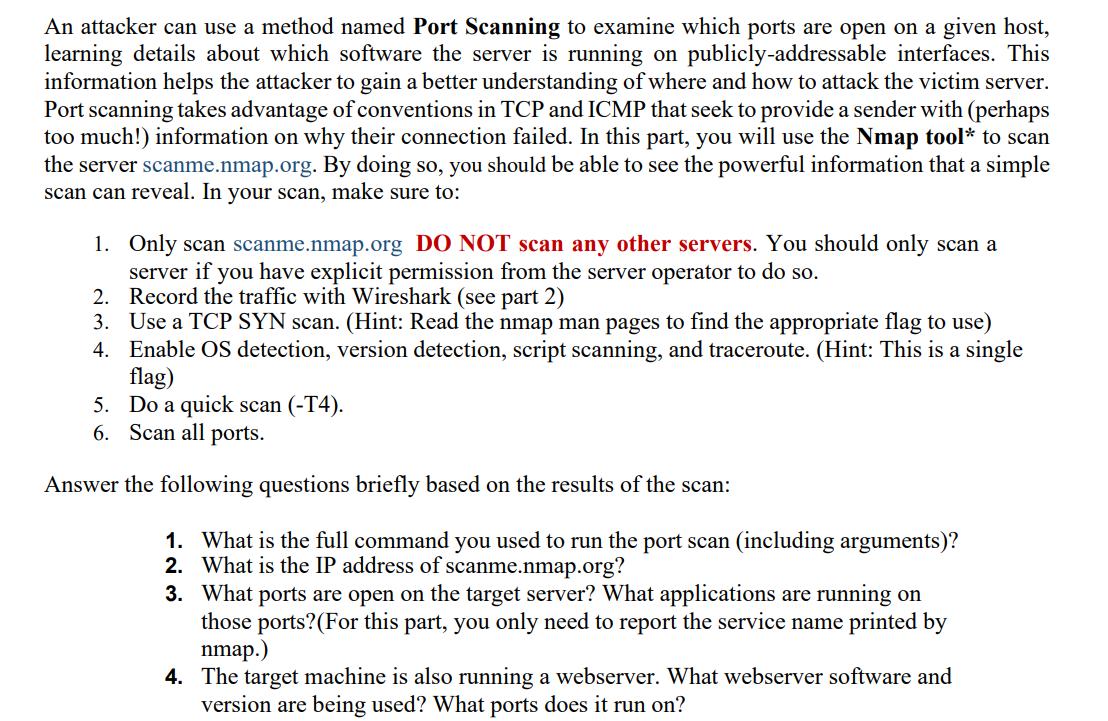
An attacker can use a method named Port Scanning to examine which ports are open on a given host, learning details about which software the server is running on publicly-addressable interfaces. This information helps the attacker to gain a better understanding of where and how to attack the victim server. Port scanning takes advantage of conventions in TCP and ICMP that seek to provide a sender with (perhaps too much!) information on why their connection failed. In this part, you will use the Nmap tool* to scan the server scanme.nmap.org. By doing so, you should be able to see the powerful information that a simple scan can reveal. In your scan, make sure to: 1. Only scan scanme.nmap.org DO NOT scan any other servers. You should only scan a server if you have explicit permission from the server operator to do so. 2. Record the traffic with Wireshark (see part 2) 3. Use a TCP SYN scan. (Hint: Read the nmap man pages to find the appropriate flag to use) 4. Enable OS detection, version detection, script scanning, and traceroute. (Hint: This is a single flag) 5. Do a quick scan (-T4). 6. Scan all ports. Answer the following questions briefly based on the results of the scan: 1. What is the full command you used to run the port scan (including arguments)? 2. What is the IP address of scanme.nmap.org? 3. What ports are open on the target server? What applications are running on those ports? (For this part, you only need to report the service name printed by nmap.) 4. The target machine is also running a webserver. What webserver software and version are being used? What ports does it run on? An attacker can use a method named Port Scanning to examine which ports are open on a given host, learning details about which software the server is running on publicly-addressable interfaces. This information helps the attacker to gain a better understanding of where and how to attack the victim server. Port scanning takes advantage of conventions in TCP and ICMP that seek to provide a sender with (perhaps too much!) information on why their connection failed. In this part, you will use the Nmap tool* to scan the server scanme.nmap.org. By doing so, you should be able to see the powerful information that a simple scan can reveal. In your scan, make sure to: 1. Only scan scanme.nmap.org DO NOT scan any other servers. You should only scan a server if you have explicit permission from the server operator to do so. 2. Record the traffic with Wireshark (see part 2) 3. Use a TCP SYN scan. (Hint: Read the nmap man pages to find the appropriate flag to use) 4. Enable OS detection, version detection, script scanning, and traceroute. (Hint: This is a single flag) 5. Do a quick scan (-T4). 6. Scan all ports. Answer the following questions briefly based on the results of the scan: 1. What is the full command you used to run the port scan (including arguments)? 2. What is the IP address of scanme.nmap.org? 3. What ports are open on the target server? What applications are running on those ports? (For this part, you only need to report the service name printed by nmap.) 4. The target machine is also running a webserver. What webserver software and version are being used? What ports does it run on?
Expert Answer:
Answer rating: 100% (QA)
Summarize the following text 1 The full command to run the port scan is nmap T4 sS O sC t... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Suppose you have a list of blood platelet counts from 500 patients in a hospital. Which of the following is most helpful in understanding the distribution of those values: frequency table, pie chart,...
-
Assuming Noah made 6-month payments on its wood purchases from indonesla, what is the schedule of foreign currency amounts over time?
-
A force of F = 1 5 0 N is applied at 3 0 o West of North . what is the x component of the force ?
-
Use the Rayleigh-Ritz method to approximate the three lowest natural frequencies and their corresponding mode shapes of a fixed-free beam. Use polynomials of order six or less as trial functions.
-
Assume that OMalley Corp. in Exercise 16 uses the FIFO method of process costing. a. What are the equivalent units of production for direct material? b. What are the equivalent units of production...
-
Consider the function f(x)=2| find the following: 3 a. The parent function b. The vertical intercept of f(x) written as an ordered pair c. The equation of the horizontal asymptote d. Sketch f(x)
-
Please note that IGM's share price is $43.60 and Saxon's current publicly traded share price is $12.70. Please assume that Saxon earns 0% interest income from its cash and its short term investments....
-
On January 1, 2019, PR paid $90,000 to purchase 10% (10,000) of the ordinary shares of HR Inc. On December 27, 2019, HR declared and paid a dividend of $0.50 per ordinary share. HR reported a net...
-
The first trustbusters were Presidents _______-. a) Teddy Roosevelt and William Howard Taft b) Franklin Roosevelt and Harry Truman c) Dwight D. Eisenhower and John Kennedy d) Jimmy Carter and Ronald...
-
Employers rights were protected in the _______. a) National Labor Relations Act b) Taft-Hartley Act c) Clayton Act d) Sherman Antitrust Act
-
Every person who shall monopolize, or conspire with any other person or persons to monopolize, any part of the trade or commerce of the several states, or with foreign nations, shall be guilty of a...
-
The high-water mark of antitrust enforcement was marked by the _________ case. a) Alcoa c) DuPont b) U.S. Steel d) Microsoft
-
The Microsoft case ended with ___________. a) a clear-cut win for the federal government b) a compromise settlement between Microsoft and the federal government. c) a guilty plea by Microsoft, but no...
-
(a) EHS stands for Environment, Health, and Safety. It's a general term used to refer to laws, rules, regulations, professions, programs, and workplace efforts to protect the health and safety of...
-
By referring to Figure 13.18, determine the mass of each of the following salts required to form a saturated solution in 250 g of water at 30 oC: (a) KClO3, (b) Pb(NO3)2, (c) Ce2(SO4)3.
-
Emphasize how we must first know ourselves by identifying, examining, and understanding the information and systems currently in place. Explain how in order to protect our assets, defined here as the...
-
Which of the following certifications requires the applicant to complete a written practical assignment to complete the certification process? a. Security+ b. GIAC c. CISSP d. CGEIT
-
I. Describe a content filter, which is a software filtertechnically not a firewallthat allows administrators to restrict access to content from within a network. It is a set of scripts or programs...
-
Most countries in Europe do not have stringent laws to protect whistleblowers. True/false
-
In view of significant financial losses to investors, corporate fraud does not really affect the U.S. economy and investor confidence. True/false
-
Auditors should not demand full access to the entire general ledger so that they can be more focused on the audit. True/false

Study smarter with the SolutionInn App


