Assume that we have a hash table with size m = 13 and the hash function...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
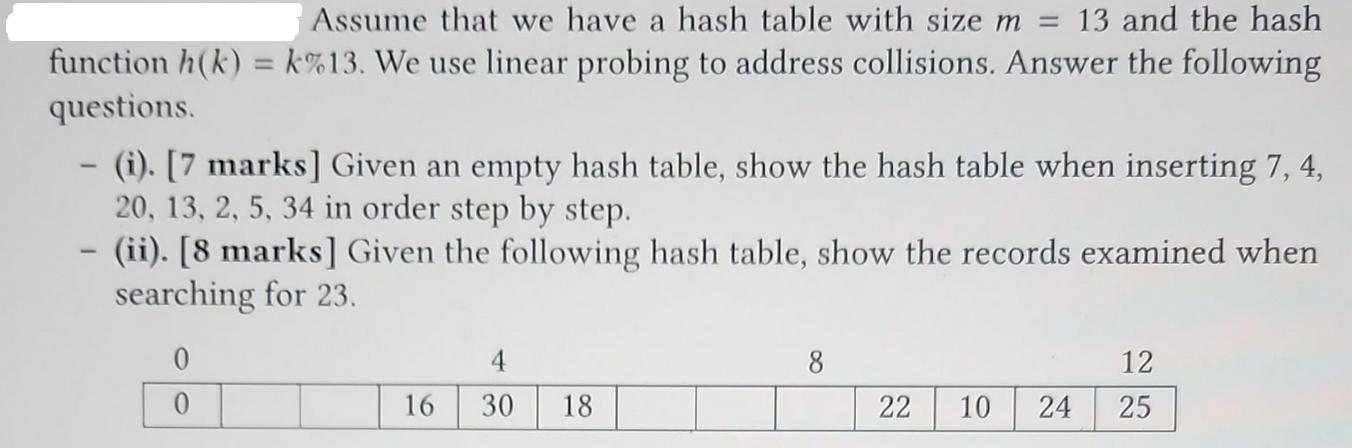
Assume that we have a hash table with size m = 13 and the hash function h(k)=k%13. We use linear probing to address collisions. Answer the following questions. - (i). [7 marks] Given an empty hash table, show the hash table when inserting 7, 4, 20, 13, 2, 5, 34 in order step by step. 1 - (ii). [8 marks] Given the following hash table, show the records examined when searching for 23. 0 0 16 4 30 18 8 22 10 24 12 25 Assume that we have a hash table with size m = 13 and the hash function h(k)=k%13. We use linear probing to address collisions. Answer the following questions. - (i). [7 marks] Given an empty hash table, show the hash table when inserting 7, 4, 20, 13, 2, 5, 34 in order step by step. 1 - (ii). [8 marks] Given the following hash table, show the records examined when searching for 23. 0 0 16 4 30 18 8 22 10 24 12 25
Expert Answer:
Answer rating: 100% (QA)
a hash table with size m 13 and the hash function hk k 13The question asks to show the records examined when searching for 23 in the given hash table ... View the full answer

Related Book For 

Building Java Programs A Back To Basics Approach
ISBN: 9780135471944
5th Edition
Authors: Stuart Reges, Marty Stepp
Posted Date:
Students also viewed these programming questions
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
Create a new file named convert.cpp . In this file, write a program that asks the user for a temperature, then converts that temperature to four ( semi - ) common temperature units. The prompt should...
-
Determine which sets of vectors are orthogonal. 3 -2 1 3 -1 3 -3 4 3 8 7 0
-
What forces are driving small businesses into international markets?
-
Ontario Manufacturing, Inc., reported the following at December 31, 2021, and December 31, 2022: Ontario Manufacturing has paid all preferred dividends only through 2018. Requirement 1. Calculate the...
-
What are the slip and coefficient of discharge?
-
David Abacus uses the Internet to place an order to license software for his computer from Inet. License, Inc. (Inet), through Inets electronic website ordering system. Inets Web page order form asks...
-
Explain demographic transition theory as was proposed by Warren Thompson and highlight the stages of development transition
-
Southwick Company uses normal costing in its job- costing system. Partially completed T- accounts and additional information for Southwick for 2012 are as follows: Required Additional information...
-
Consider operators P and Q acting on the space of square integrable functions L. The product of any two operators is defined as (PQ)(f) = P(Q(f)), where fe L. (a) Using the definition of the...
-
A milkshake has viscosity of 0.50Pa.s. To drink this shake through a straw of diameter 0.56 cm and length 22 cm, you need to reduce the pressure at the top of the straw to less than atmospheric...
-
Consider a diver (without a mask) positioned at the center of an aquarium of spherical shape 4 m in diameter. Refractive index of water is n=4/3. If the diver is looking at a spectator staying 0.5 m...
-
The financial ratios of a firm can best be compared to: (A) ratios of firms in the same city. (B) ratios of firms having the same capital structure. (C) ratios of firms in the same industry. (D)...
-
Short-term capital gains are taxed at the taxpayer's marginal tax rate. True O False
-
What is the best example of a scenario in which a new database should be created to support the business? O An organization would like to pull the current reviews of books from different sites to...
-
The National Collegiate Athletic Association (NCAA) is a nonprofit organization that regulates student athletes from 1,268 North American institutions and conferences. It is one of the largest...
-
The activities listed in lines 2125 serve primarily as examples of A) Underappreciated dangers B) Intolerable risks C) Medical priorities D) Policy failures
-
What is the output produced from the following statements? System.out.println("\ta\tb\tc"); System.out.println("\\\\"); System.out.println("'"); System.out.println("\"\"\""); System.out.println("C:...
-
Write a static method called xo that accepts an integer size as a parameter and prints a square of size by size characters, where all characters are o except that an x pattern of x characters has...
-
Write a method called consecutive that accepts three integers as parameters and returns true if they are three consecutive numbersthat is, if the numbers can be arranged into an order such that,...
-
Biologists have studied the running ability of the northern quoll, a marsupial indigenous to Australia. In one set of experiments, they studied the maximum speed that quolls could run around a curved...
-
The chain on a bicycle turns the rear wheel via a gear cluster, as shown in Figure Q7.6. The gears vary in size; the smallest gear has a radius of 2.3 cm, the largest a radius of 6.0 cm. If we assume...
-
The torque needed to open a factory-sealed jar is about the same as the torque required to turn the wheel on a passenger car. You know that the force necessary to turn your cars steering wheel is...

Study smarter with the SolutionInn App