Assume you are hashing a set (unknown length) of randomly generated Strings, into a HashTable with...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
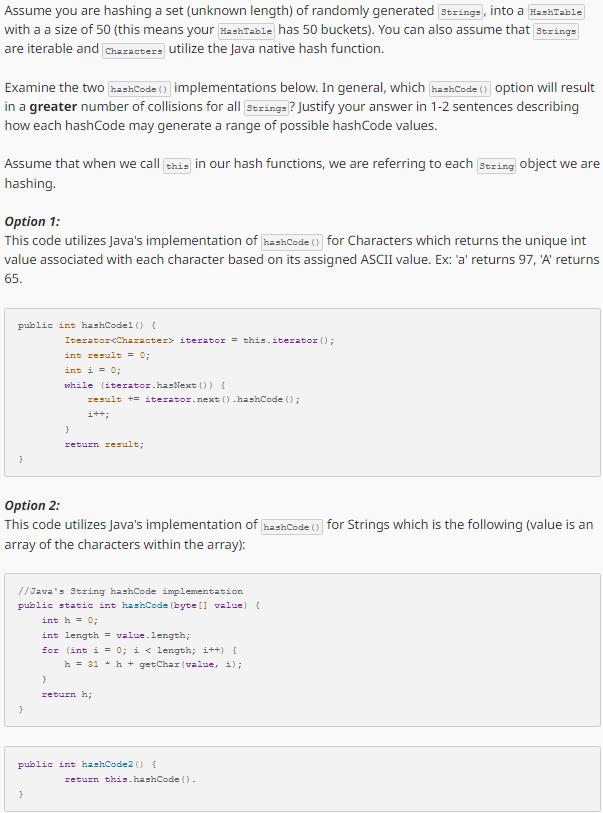
Assume you are hashing a set (unknown length) of randomly generated Strings, into a HashTable with a a size of 50 (this means your HashTable has 50 buckets). You can also assume that strings are iterable and characters utilize the Java native hash function. Examine the two hashCode() implementations below. In general, which hashCode () option will result in a greater number of collisions for all strings? Justify your answer in 1-2 sentences describing how each hashCode may generate a range of possible hashCode values. Assume that when we call this in our hash functions, we are referring to each string object we are hashing. Option 1: This code utilizes Java's implementation of hashCode () for Characters which returns the unique int value associated with each character based on its assigned ASCII value. Ex: 'a' returns 97, 'A' returns 65. public int hashCodel () { Iterator<Character> iterator= this.iterator (); int result = 0; int i = 0; while literator.hasNext ()) { result += iterator.next().hashCode (); i++; } return result; Option 2: This code utilizes Java's implementation of hashCode () for Strings which is the following (value is an array of the characters within the array): //Java's String hashCode implementation public static int hashCode (byte [ value) { int h = 0; int length = value.length; for (int i = 0; i< length; i++) { h = 31 h + getChar (value, i); } return h; public int hashCode2() { return this.hashCode (). Assume you are hashing a set (unknown length) of randomly generated Strings, into a HashTable with a a size of 50 (this means your HashTable has 50 buckets). You can also assume that strings are iterable and characters utilize the Java native hash function. Examine the two hashCode() implementations below. In general, which hashCode () option will result in a greater number of collisions for all strings? Justify your answer in 1-2 sentences describing how each hashCode may generate a range of possible hashCode values. Assume that when we call this in our hash functions, we are referring to each string object we are hashing. Option 1: This code utilizes Java's implementation of hashCode () for Characters which returns the unique int value associated with each character based on its assigned ASCII value. Ex: 'a' returns 97, 'A' returns 65. public int hashCodel () { Iterator<Character> iterator= this.iterator (); int result = 0; int i = 0; while literator.hasNext ()) { result += iterator.next().hashCode (); i++; } return result; Option 2: This code utilizes Java's implementation of hashCode () for Strings which is the following (value is an array of the characters within the array): //Java's String hashCode implementation public static int hashCode (byte [ value) { int h = 0; int length = value.length; for (int i = 0; i< length; i++) { h = 31 h + getChar (value, i); } return h; public int hashCode2() { return this.hashCode ().
Expert Answer:
Answer rating: 100% (QA)
The two options presented are Using Javas implementation of hashCode for Characters This approach assigns a unique integer value to each character based on its ASCII value For instance a returns 97 an... View the full answer

Related Book For 

Managerial Economics
ISBN: 978-0133020267
7th edition
Authors: Paul Keat, Philip K Young, Steve Erfle
Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Assignment 5: Hash Table implementation andconcordance There are three parts to this assignment. In the first two parts,you will complete the implementation of a hash map and aconcordance program. In...
-
When my niece Michelle told me she had learned to read, she was bursting with pride. How might reflecting on this accomplishment affect how Michelle thinks about herself?
-
The following information was taken from the 2009 annual report of Emerson Electric Co., a leader in the network power sector (dollars in millions): (a) Compute total accounts receivable as of the...
-
Johnson Company incurred $920 in shipping costs related to the inventory purchases in PE 7-5. The company paid for the shipping costs in cash. Make the journal entry necessary to record this...
-
Ryan Bagley and William Sargent were long-time friends who served in the military together. Prior to July 2014, they had discussed the possibility of forming a partnership to purchase, rent, and...
-
The names of the employees of Cox Security Systems and their regular salaries are shown in the following payroll register. Note that Hall and Short are paid monthly on the last payday, while all...
-
How do organizations leverage predictive analytics and machine learning algorithms to anticipate future performance trends and proactively address potential performance gaps ?
-
Using lab 7 with a three-day lead time (all original values), we will analyze six different scenarios to determine which would be the best scenario based on the total cost. Scenario A - Min is 3,500...
-
4. Answer the following short questions: 2 (a) Can you find a utility function u(x1, x2) resulting in the following demand func- tions for the two goods 1, 2: -0.7 1(P1 P2, w)=wp 1 and 12(P1, P2,...
-
Behavioural Finance Do you think emerging markets will be more or less efficient? Do you think they will be more or less sensitive to market sentiment? Explain.
-
My company can borrow at 5 per cent so it means that its cost of capital for all new projects is 5 per cent. Do you agree with this statement? Explain.
-
Assume that you are the manager of a family firm and the company wishes to expand its operations into a new unrelated business sector. The expansion requires funding. What type of financing (debt or...
-
Unicredit, a multinational bank, had a rights issue in January 2012. Assisted by a consortium of banks including BofA Merrill Lynch and Mediobanca, Unicredit sold 3.86 billion shares at 1.943 each,...
-
Insider Trading When corporate executives trade the shares of their own company, the share price normally responds in a correlated way (i.e. share price increases after buy transactions and share...
-
Jamming Limited has two production departments: Forming and Assembly. The company also has two service departments: Maintenance and Stores. It manufactures Part YDN12 that passes through both...
-
What are some of the possible sources of information about a company that could be used for determining the companys competitive stance?
-
Discuss the meaning of the term principal-agent problem. Why does this problem exist?
-
You are the manager of a large automobile dealership who wants to learn more about the effectiveness of various discounts offered to customers over the past 14 months. Following are the average...
-
How is the weighted average cost of capital determined?
-
Suppose you are considering investing in a Roth IRA. You collect the data in Table 12, which represent the five-year rate of return (in percent, adjusted for sales charges) for a simple random sample...
-
Construct a frequency and relative frequency histogram of the five-year rate of- return data discussed in Example 3. Approach To draw the frequency histogram, use the frequency distribution in Table...
-
Construct a frequency and relative frequency histogram of the five-year rate of- return data discussed in Example 3. Approach We will use StatCrunch to construct the frequency and relative frequency...

Study smarter with the SolutionInn App