3. Here is a Python dictionary of the relative frequency of letters in English text: {...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
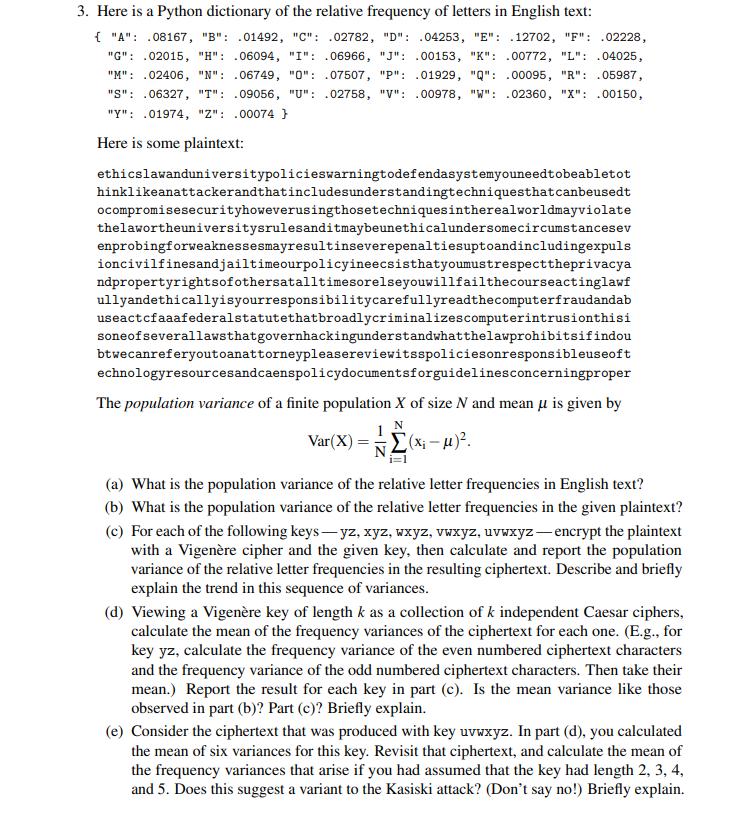
3. Here is a Python dictionary of the relative frequency of letters in English text: { "A": .08167, "B": .01492, "C": .02782, "D": .04253, "E": .12702, "F": .02228, "G": .02015, "H": .06094, "I": .06966, "J": .00153, "K": .00772, "L": .04025, "M": .02406, "N": .06749, "0": 07507, "P": .01929, "Q": .00095, "R": .05987, "S": .06327, "T": .09056, "U": .02758, "V": .00978, "W": .02360, "X": .00150, "Y": .01974, "Z": .00074 } Here is some plaintext: ethicslawanduniversitypolicieswarningtodefendasystemyouneedtobeabletot hinklikeanattackerandthat includesunderstandingtechniques that canbeusedt ocompromisesecurityhoweverusingthose techniques intherealworldmayviolate thelawortheuniversitysrulesanditmaybeunethical undersome circumstancesev enprobingforweaknessesmayresultinseverepenaltiesuptoandincludingexpuls ioncivilfinesandjailtimeourpolicyineecsisthatyoumustrespecttheprivacya ndpropertyrightsof othersatalltimesorelseyouwill fail the courseactinglawf ullyandethicallyisyourresponsibility carefullyreadthe computerfraudandab useactcfaaafederalstatute thatbroadlycriminalizes computerintrusionthisi soneofseverallaws that governhackingunderstand what thelawprohibitsifindou btwecanreferyoutoanattorneypleasereviewitsspolicies onresponsibleuseoft echnologyresourcesandcaenspolicydocumentsforguidelines concerningproper The population variance of a finite population X of size N and mean u is given by N Var(X) = (x₁ -μ)². (a) What is the population variance of the relative letter frequencies in English text? (b) What is the population variance of the relative letter frequencies in the given plaintext? (c) For each of the following keys-yz, xyz, wxyz, vwxyz, uvwxyz-encrypt the plaintext with a Vigenère cipher and the given key, then calculate and report the population variance of the relative letter frequencies in the resulting ciphertext. Describe and briefly explain the trend in this sequence of variances. (d) Viewing a Vigenère key of length k as a collection of k independent Caesar ciphers, calculate the mean of the frequency variances of the ciphertext for each one. (E.g., for key yz, calculate the frequency variance of the even numbered ciphertext characters and the frequency variance of the odd numbered ciphertext characters. Then take their mean.) Report the result for each key in part (c). Is the mean variance like those observed in part (b)? Part (c)? Briefly explain. (e) Consider the ciphertext that was produced with key uvwxyz. In part (d), you calculated the mean of six variances for this key. Revisit that ciphertext, and calculate the mean of the frequency variances that arise if you had assumed that the key had length 2, 3, 4, and 5. Does this suggest a variant to the Kasiski attack? (Don't say no!) Briefly explain. 3. Here is a Python dictionary of the relative frequency of letters in English text: { "A": .08167, "B": .01492, "C": .02782, "D": .04253, "E": .12702, "F": .02228, "G": .02015, "H": .06094, "I": .06966, "J": .00153, "K": .00772, "L": .04025, "M": .02406, "N": .06749, "0": 07507, "P": .01929, "Q": .00095, "R": .05987, "S": .06327, "T": .09056, "U": .02758, "V": .00978, "W": .02360, "X": .00150, "Y": .01974, "Z": .00074 } Here is some plaintext: ethicslawanduniversitypolicieswarningtodefendasystemyouneedtobeabletot hinklikeanattackerandthat includesunderstandingtechniques that canbeusedt ocompromisesecurityhoweverusingthose techniques intherealworldmayviolate thelawortheuniversitysrulesanditmaybeunethical undersome circumstancesev enprobingforweaknessesmayresultinseverepenaltiesuptoandincludingexpuls ioncivilfinesandjailtimeourpolicyineecsisthatyoumustrespecttheprivacya ndpropertyrightsof othersatalltimesorelseyouwill fail the courseactinglawf ullyandethicallyisyourresponsibility carefullyreadthe computerfraudandab useactcfaaafederalstatute thatbroadlycriminalizes computerintrusionthisi soneofseverallaws that governhackingunderstand what thelawprohibitsifindou btwecanreferyoutoanattorneypleasereviewitsspolicies onresponsibleuseoft echnologyresourcesandcaenspolicydocumentsforguidelines concerningproper The population variance of a finite population X of size N and mean u is given by N Var(X) = (x₁ -μ)². (a) What is the population variance of the relative letter frequencies in English text? (b) What is the population variance of the relative letter frequencies in the given plaintext? (c) For each of the following keys-yz, xyz, wxyz, vwxyz, uvwxyz-encrypt the plaintext with a Vigenère cipher and the given key, then calculate and report the population variance of the relative letter frequencies in the resulting ciphertext. Describe and briefly explain the trend in this sequence of variances. (d) Viewing a Vigenère key of length k as a collection of k independent Caesar ciphers, calculate the mean of the frequency variances of the ciphertext for each one. (E.g., for key yz, calculate the frequency variance of the even numbered ciphertext characters and the frequency variance of the odd numbered ciphertext characters. Then take their mean.) Report the result for each key in part (c). Is the mean variance like those observed in part (b)? Part (c)? Briefly explain. (e) Consider the ciphertext that was produced with key uvwxyz. In part (d), you calculated the mean of six variances for this key. Revisit that ciphertext, and calculate the mean of the frequency variances that arise if you had assumed that the key had length 2, 3, 4, and 5. Does this suggest a variant to the Kasiski attack? (Don't say no!) Briefly explain.
Expert Answer:
Answer rating: 100% (QA)
What is the population variance of the relative letter frequencies in English text The population variance of the relative letter frequencies in English text is given by N x 2 VarX N x 2 VarX N x 2 Va... View the full answer

Related Book For 

College Mathematics for Business Economics Life Sciences and Social Sciences
ISBN: 978-0321614001
12th edition
Authors: Raymond A. Barnett, Michael R. Ziegler, Karl E. Byleen
Posted Date:
Students also viewed these mathematics questions
-
For Problems a - c (a) Using equation (20) from Problem 25, solve for the two values of {Jt¢ for which ( 1 9) is satisfied. (b) Substitute (one at a time) each value of {Jt¢ found in part...
-
For Problem 16-16, develop upper and lower control limits for the range. Do these samples indicate that the process is in control?
-
The equation from the previous problem but with water entering at a rate of 4.0 cm/s. Apply the stability theorem for autonomous differential equations to the following equations. Show that your...
-
Audrey has recently purchased a home with a $325,000 mortgage. She opted for monthly payments, a term of 5 years at a rate of 3.2%, and an amortization period of 25 years. Had Audrey chosen, instead,...
-
Howard owns 2% of the shares of Y Ltd. He is also employed by Y in a middle management position. On August 1, 20X7, Howard received a loan from Y that he used to repay personal debts. Howard signed a...
-
On January 1, 2021, Winn Heat Transfer leased office space under a three-year operating lease agreement. The arrangement specified three annual lease payments of $80,000 each, beginning December 31,...
-
Which of the following assertions concerning the interpretive publications is inaccurate: (a) Interpretive publications consist of auditing Interpretations of the SASs, appendixes to the SASs,...
-
Francis Corporation purchased an asset at a cost of $50,000 on March 1, 2012. The asset has a useful life of 8 years and a salvage value of $4,000. For tax purposes, the MACRS class life is 5 years....
-
What is the present value of the following cash flow streams at an interest rate of 7.25%? Year 0 = 750 Year 1 = 2450 Year 2 = 3175 Year 3 = 4400
-
Part One: In 2015, Fran Lexa opened Fran's Flowers, a small shop selling floral arrangements. On December 31, 2016, her accounting records show the following: Sales revenue...
-
in Java...please use code i already have explanation but ineed help with the actual code Objective: Learn programming language implementation systems that includes lexical anu syntax analysis....
-
ABC Ltd has sales of 1 0 , 0 0 0 units. The sale price per unit is 3 0 . Variable costs per unit are 1 4 and the company s fixed costs total 8 0 , 0 0 0 . The company is thinking of reducing the sale...
-
A travel softball team is trying to raise funds to go to the Colorado Sparkler, a major summer national tournament. The team is going to sell 3000 raffle tickets for $9 each. The prizes and their...
-
You are assigned to the audit of Splendour Seas ( Pty ) Ltd ( Splendour ) , for the financial year ending 3 0 June 2 0 2 3 . Splendour is a passenger shipping company specializing in providing 7 day,...
-
How might the adoption of holacratic organizational principles, centered around dynamic role definitions and peer-to-peer governance, foster a culture of transparency, empowerment, and distributed...
-
If a business received a settlement discount from a creditor for paying their account off early, what would be the accounting treatment of the discount be ?
-
Question 3 (10 marks) Glow Company is presently making a light that is used as a component in one of its products. Annual required production is 40,000 units. The unit product costs for the light...
-
1-Stern observed all of the following results EXCEPT _______ in his experiment. A-one of the recombinant phenotypes was associated with an X chromosome of normal length B-the number of car, B+ male...
-
How many 4-person committees are possible from a group of 9 people if (A) There are no restrictions? (B) Both Jim and Mary must be on the committee? (C) Either Jim or Mary (but not both) must be on...
-
In Problem, could the given matrix be the transition matrix of a regular Markov chain? 110 001 090
-
In Problems 63-66, the left sum Ln or the right sum Rn is used to approximate the definite integral to the indicated accuracy. How large must n be chosen in each case? (Each function is increasing...
-
Which statement is false with respect to the PCAOB? a. PCAOB issues standards describing auditor's attestation requirements. b. D.W. Squires was a former chief auditor of PCAOB. c. PCAOB is a...
-
Select five of these alleged fraudsters and prepare a two-paragraph discussion of them. Outline their modus operandi. 1. Frank Abagnale 2. Jack Abramoff 3. Kobi Alexander 4. Eddie Antar 5. Jim Bakker...
-
Which statement is false with respect to Section 404 of SOX? a. The section requires management's assessment of internal control over financial reporting. b. The auditor's report on internal control...

Study smarter with the SolutionInn App