data and network security subject or information security QUESTION 1 [25 MARKS] (a) Employees are increasingly having
Fantastic news! We've Found the answer you've been seeking!
Question:
data and network security subject or information security
Transcribed Image Text:
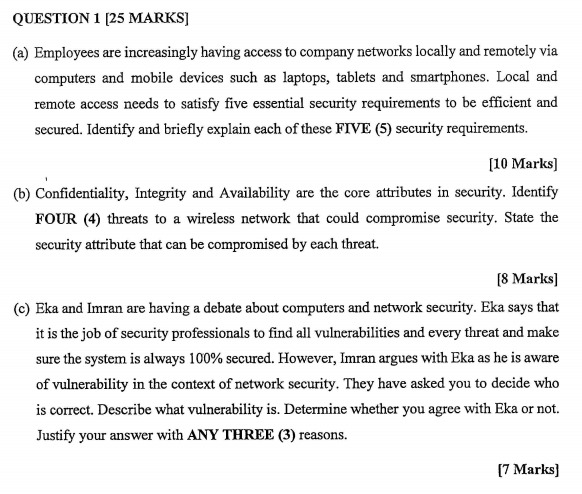
QUESTION 1 [25 MARKS] (a) Employees are increasingly having access to company networks locally and remotely via computers and mobile devices such as laptops, tablets and smartphones. Local and remote access needs to satisfy five essential security requirements to be efficient and secured. Identify and briefly explain each of these FIVE (5) security requirements. [10 Marks] (b) Confidentiality, Integrity and Availability are the core attributes in security. Identify FOUR (4) threats to a wireless network that could compromise security. State the security attribute that can be compromised by each threat. [8 Marks] (c) Eka and Imran are having a debate about computers and network security. Eka says that it is the job of security professionals to find all vulnerabilities and every threat and make sure the system is always 100% secured. However, Imran argues with Eka as he is aware of vulnerability in the context of network security. They have asked you to decide who is correct. Describe what vulnerability is. Determine whether you agree with Eka or not. Justify your answer with ANY THREE (3) reasons. [7 Marks] QUESTION 1 [25 MARKS] (a) Employees are increasingly having access to company networks locally and remotely via computers and mobile devices such as laptops, tablets and smartphones. Local and remote access needs to satisfy five essential security requirements to be efficient and secured. Identify and briefly explain each of these FIVE (5) security requirements. [10 Marks] (b) Confidentiality, Integrity and Availability are the core attributes in security. Identify FOUR (4) threats to a wireless network that could compromise security. State the security attribute that can be compromised by each threat. [8 Marks] (c) Eka and Imran are having a debate about computers and network security. Eka says that it is the job of security professionals to find all vulnerabilities and every threat and make sure the system is always 100% secured. However, Imran argues with Eka as he is aware of vulnerability in the context of network security. They have asked you to decide who is correct. Describe what vulnerability is. Determine whether you agree with Eka or not. Justify your answer with ANY THREE (3) reasons. [7 Marks]
Expert Answer:
Answer rating: 100% (QA)
a The five essential security requirements for local and remote access to company networks are 1 Authentication Authentication ensures that users are who they claim to be before granting access to the ... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these computer network questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Question (700 words) John Densmore, a law student and part-time musician, was seriously injured in a car accident. The other car's driver, Ray Manzarek, a renowned life motivation coach and a...
-
The Niakwa Industries prepared the following statement of earnings and comparative statement of financial position for 2020: The Niakwa Industries prepared the following statement of earnings and...
-
Urban Window Company had gross wages of $320,000 during the week ended July 15. The amount of wages subject to social security tax was $320,000, while the amount of wages subject to federal and state...
-
Table P-18 contains the number of severe earthquakes (those with a Richter scale magnitude of 7 and above) per year for the years 1900-1999. a. Use Minitab to smooth the earthquake data with moving...
-
Positive accounts receivable confirmations are appropriate when: a. There is reason to believe that a substantial number of accounts may be in dispute. b. Control risk is low. c. Accounts receivable...
-
Rinehart Corporation purchased from its stockholders 5,000 shares of its own previously issued stock for $255,000. It later resold 2,000 shares for $54 per share, then 2,000 more shares for $49 per...
-
Consider the energy we use everyday in routine tasks, where that energy comes from, and where it goes. When you walk up a hill you overcome the force of gravity to raise yourself higher against the...
-
A perpetual preferred stock's price is $104.78 per share. If its par value is $100 per share and the dividend rate is 5.5% per year, what annual return do investors require?
-
Explain what is meant by the accrual of liabilities.
-
Describe the main contents of a business plan for presenting to a bank providing finance for a small business.
-
Register for the free version of Talkwalker. Do a search for the brand you chose in activity 1, and view the time line of engagement. What new insights have you learned about the brand? Data From...
-
How is the economic order quantity calculated.
-
What kinds of organisation are likely to use JIT production.
-
How is development and underdevelopment defined by Dr. Walter Rodney in How Europe Underdeveloped Africa? Please give at least two (2) examples of development and underdevelopment in one African...
-
On average there are four traffic accidents in a city during one hour of rush-hour traffic. Use the Poisson distribution to calculate the probability that in one such hour there arc (a) No accidents...
-
Differentiate between conversion strategies, prioritization among multiple components, outsourcing, and technology governance.
-
Define the reality that certifications cost money and the better certifications can be quite expensive to attain. Depending on the certification, one can cost more than$750.00 alone, and...
-
I. Justify the facts that organizations that had remote access systems in place were far better equipped to handle the transformation of the workplace that was the result of the pandemic. II....
-
A university is deciding between two meal plans. One plan charges a fixed fee of \($600\) per semester and allows students to eat as much as they want. The other plan charges a fee based on the...
-
Evaluate this statement: You are a natural athlete, an attractive person who learns easily and communicates well. Clearly, you can do everything better than your friends and acquaintances. As a...
-
You have waited 30 minutes in a line for the Star Tours ride at Disneyland. You see a sign that says, From this point on, your wait is 45 minutes. You must decide whether to remain in the line or to...

Study smarter with the SolutionInn App


