E.1 Background As cyberspace grows more complex and increasingly contested with sophisticated threats able to exploit known
Question:
E.1 Background
As cyberspace grows more complex and increasingly contested with sophisticated threats able to exploit known and unknown vulnerabilities, cyberspace operations and cybersecurity are exceptionally critical to national security.[1] The Army's portion of the cyberspace domain requires an effective understanding of the technology landscape as it relates to current and future cyberspace capability needs. At all levels, the Army seeks to build, operate, and maintain secure and defensible networks, protecting them against specific threats to achieve mission assurance while denying the adversary freedom of action in the cyberspace domain. New and creative processes and models are required to mature holistic Army Cyberspace operations, comprising offensive, defensive, and DoD Information Networks (DoDIN) capability areas. Army perspective points, or pillars, to achieving a future vision of Army Cyberspace Operations consist of:
- Integrated Offensive Cyberspace Operations (OCO) providing degradation, disruption, or destruction effects;
- Transformed Defensive Cyberspace Operations (DCO) enabling maneuver, passive and active defense;
- Improved DoD Information Network (DoDIN) for a robust and assured defensive cyber posture; and
- Integrated Cyberspace Situational Understanding capability providing analytics, storage, and correlation to reduce risk.
As a response to the operational community, the Office of the Assistant Secretary of the Army for Acquisition, Logistics and Technology (ASA(ALT)) Systems of Systems Engineering & Integration (SoSE&I) Directorate developed the Army Cyber Innovation Challenge model. The model leverages existing authority, enabling an agile and flexible process to investigate priority Army cyberspace requirements. The challenge model provides a rapid prototyping capability to aid developmental acquisition strategies.
E.1.1 Problem Set
The Army continually seeks to mature and operationalize the cyberspace domain. General Milley, U.S. Army Chief of Staff, when testifying before the Senate Armed Services Committee, stated that one of the Army's top priorities is "...to invest in the technologies, organization, and doctrine that will allow us to maintain overmatch against future adversaries while retaining the ability to adapt to unforeseen challenges." Army networks and information systems are large and complex, creating a large cyberspace "footprint" within the Department of Defense (DoD). The Army relies upon secure and resilient networks to support Army and joint forces at the tactical and strategic levels. The Army must continue to modernize its networks and information systems by applying a threat-informed defense model capable of reacting to incidents and recovering and adapting in support of Unified Land Operations. The Army's portion of the DoDIN is the technical network that encompasses all Army information management and information systems that collect, process, store, display, disseminate, and protect information worldwide. In the pursuit of increasingly defensible networks, the Army must apply technical solutions that improve the overall security posture for creating a defensible cyber terrain that is resilient and adaptable in support of Army and Joint operations.
As an integral part of addressing this problem space, the Government has partnered with organizations such as the Consortium for Command, Control, and Communications in Cyberspace (C5) and Defense Innovation Unit Experimental (DIUx) to access leading edge technology and vendors with the collective expertise in the following technology areas specifically related to Army Cyberspace Operations:
Innovative technologies, processes, methods, facilities, and capabilities - These are sought to identify, develop, test, provide access to, and improve technologies resident in universities, private and federal labs, incubators, and industry that focus on Army cyberspace requirements (offensive, defensive, and DoDIN) related to weapons and weapons systems. At all levels, the Army seeks to build, operate, and secure defensible networks, defending them against specific threats to achieve mission assurance while denying the adversary freedom of action in the cyberspace domain.
Offensive Cyberspace Operations Objectives - Technologies supporting operations to project power by the application of force against enemies and adversaries in and through cyberspace.
Defensive Cyberspace Operations Objectives - Technologies supporting operations conducted to defend DoD or other friendly cyberspace and preserve the ability to utilize friendly cyberspace capabilities.
- Technologies to gain and maintain situational awareness through the visualization of key cyber terrain and an understanding of the actions occurring within that terrain;
- Technologies that actively predict and hunt for (search and discover) advanced internal cyber threats and vulnerabilities that do not trigger or generate warnings using routine detection measures;
- Technologies that allow friendly cyber forces to outmaneuver adversaries by performing preapproved, automated, agile, internal countermeasures that stop or mitigate cyber-attacks; and, when authorized, to conduct response actions external to friendly networks in order to create effects that deny the adversary use of offensive cyber capabilities;
- Technologies to conduct DCO mission planning and protection that identify and assure the availability of key cyber terrain and critical infrastructure for the Army, DoD, host nation, and civil authorities that support Army missions;
- Technologies that protect networks, information technology platforms, and data by controlling inbound/outbound traffic, dynamically managing locations of critical services, and hardening information systems;
- Technologies to conduct mission assurance actions that dynamically re-establish, resecure, re-route, reconstitute, or isolate degraded or compromised networks;
- Technologies to conduct site exploitation and forensic analysis and determine technical and operational impacts of intrusions; and
- Technologies to evaluate the defensive posture of networks and information systems using vulnerability assessment methods and threat emulation in order to recommend or direct changes to ensure operational readiness.
DoDIN Operations Objectives - Technologies supporting operations to design, build, configure, secure, operate, maintain, and sustain networks.
- Technologies to build (plan, engineer, install) secure, resilient, and defensible networks;
- Technologies that support global, secure, adaptive, and rapid access across trusted and authenticated domains to authorized entities;
- Technologies that allow for the secure operation of networks (i.e., automated scanning and remediation of vulnerabilities);
- Technologies that support the integration with mission partners during garrison and deployed operations; and
? Technologies that support the discovery, delivery, and storage of data to provide awareness and access to information in a timely and efficient manner.
E.1.2 Acquisition Approach
To ensure the full scope of Army requirements and technology objectives would be accommodated through various consortium communities and associated models, ASA(ALT) engaged with the Army Armament Research, Development and Engineering Center (ARDEC) to adequately scope technology objectives and utilized an existing community, the Consortium for Command, Control, and Communications in Cyberspace, known as C5. Membership in the consortium is open (on a rolling basis) to all companies and academic institutions with associated capabilities, with annual dues of $500 annually. Academic institution fees are waived. The consortium approach allows for cross-sector collaboration among industry, university, and Government entities, offering diversity of subject matter expertise focused on addressing the most critical cyberspace operational challenges. The Army's vision is to leverage various organizations such as C5, DIUx, and potentially others to help guide the development of next-generation defensive, offensive, and DoDIN cyberspace operations capability.
The Government has established a Section 845 Prototype Other Transaction Agreement (OTA) with an existing consortium, the Consortium for Command, Control, and Communications in Cyberspace (C5) that has significant non-traditional contractor participants. The goal of this consortium community is to assist in maturing Army Cyberspace Operations through re-use, augmenting existing cyber technologies, and fostering relevant cyber weapons systems and awareness in the newly established Cyber domain. Cyberspace is a global domain within the information environment consisting of the interdependent network of information technology infrastructures and resident data including the Internet, telecommunications networks, computer systems, and embedded processors and controllers (JP 1-02). Maturing the Army Cyberspace domain requires an effective understanding of the technology landscape as it relates to current and future cyberspace capability needs.
The mission of the consortium is to establish the Army as a leader in cyberspace operations, capability development, R&D, education and training programs, and policy development. Additional goals include:
- Be a thought and action leader across the cyberspace operations stakeholder community;
- Serve as proof-of-concept test bed and blueprint for requirements articulation and capability development;
- Facilitate the advancement of membership cyber maturity levels (as this domain knowledge grows, the probability of warfighter technological advantage increases);
- a cyber center of gravity as incubator and engine for a cyberspace capability; and
? Shape and enable cyberspace operations education.
E.1.3 Consortium Business Model and Other Transaction Authority (OTA)
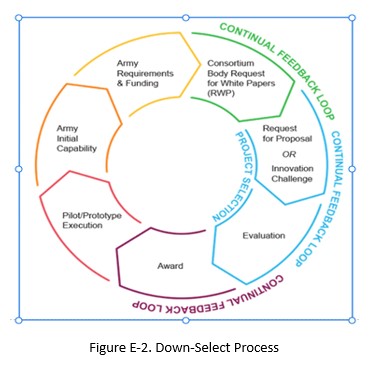
To execute each Cyber Innovation Challenge, the Army works through a consortium, a voluntary organization with members from industry, academia, and Government, utilizing a flexible acquisition mechanism known as Other Transaction Authority (OTA). This approach allows the Army to quickly solicit, evaluate, and purchase limited quantity prototypes of equipment from a wide range of non-traditional sources, including small and micro companies, who may lack the resources to engage in the traditional Government contracting process.
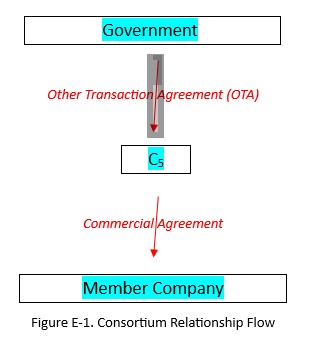
The C5 consortium acts as a conduit and marketplace linking the Army and industry (members of the consortium). The relationship between the Army and C5 is established through an OTA, while C5 translates the Army's requirements into commercial agreements with members of the consortium. Figure E-1 depicts the relationships and overarching process flow of the consortium business model[2] used by the Army and C5.
Government