explain step by step 4. In a mobile roaming system, there are three entities: a mobile user
Fantastic news! We've Found the answer you've been seeking!
Question:
explain step by step
Transcribed Image Text:
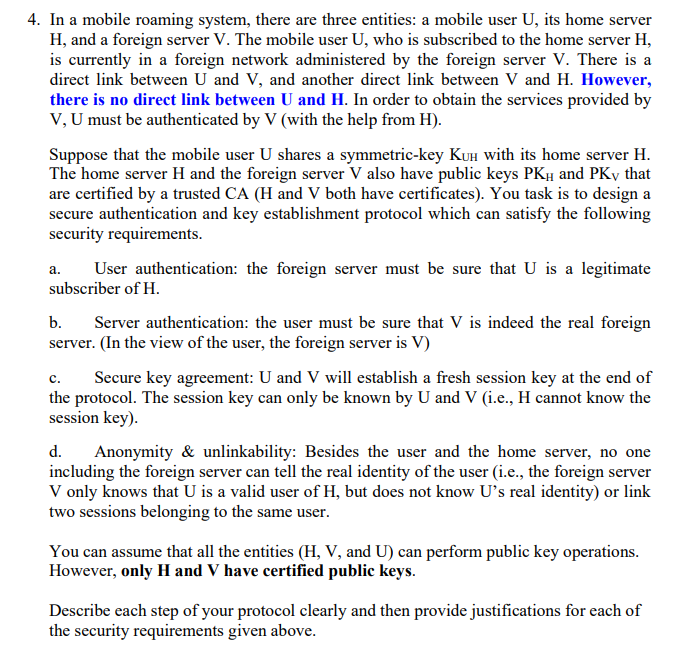
4. In a mobile roaming system, there are three entities: a mobile user U, its home server H, and a foreign server V. The mobile user U, who is subscribed to the home server H, is currently in a foreign network administered by the foreign server V. There is a direct link between U and V, and another direct link between V and H. However, there is no direct link between U and H. In order to obtain the services provided by V, U must be authenticated by V (with the help from H). Suppose that the mobile user U shares a symmetric-key KUH with its home server H. The home server H and the foreign server V also have public keys PKH and PKy that are certified by a trusted CA (H and V both have certificates). You task is to design a secure authentication and key establishment protocol which can satisfy the following security requirements. a. User authentication: the foreign server must be sure that U is a legitimate subscriber of H. b. Server authentication: the user must be sure that V is indeed the real foreign server. (In the view of the user, the foreign server is V) c. Secure key agreement: U and V will establish a fresh session key at the end of the protocol. The session key can only be known by U and V (i.e., H cannot know the session key). d. Anonymity & unlinkability: Besides the user and the home server, no one including the foreign server can tell the real identity of the user (i.e., the foreign server V only knows that U is a valid user of H, but does not know U's real identity) or link two sessions belonging to the same user. You can assume that all the entities (H, V, and U) can perform public key operations. However, only H and V have certified public keys. Describe each step of your protocol clearly and then provide justifications for each of the security requirements given above. 4. In a mobile roaming system, there are three entities: a mobile user U, its home server H, and a foreign server V. The mobile user U, who is subscribed to the home server H, is currently in a foreign network administered by the foreign server V. There is a direct link between U and V, and another direct link between V and H. However, there is no direct link between U and H. In order to obtain the services provided by V, U must be authenticated by V (with the help from H). Suppose that the mobile user U shares a symmetric-key KUH with its home server H. The home server H and the foreign server V also have public keys PKH and PKy that are certified by a trusted CA (H and V both have certificates). You task is to design a secure authentication and key establishment protocol which can satisfy the following security requirements. a. User authentication: the foreign server must be sure that U is a legitimate subscriber of H. b. Server authentication: the user must be sure that V is indeed the real foreign server. (In the view of the user, the foreign server is V) c. Secure key agreement: U and V will establish a fresh session key at the end of the protocol. The session key can only be known by U and V (i.e., H cannot know the session key). d. Anonymity & unlinkability: Besides the user and the home server, no one including the foreign server can tell the real identity of the user (i.e., the foreign server V only knows that U is a valid user of H, but does not know U's real identity) or link two sessions belonging to the same user. You can assume that all the entities (H, V, and U) can perform public key operations. However, only H and V have certified public keys. Describe each step of your protocol clearly and then provide justifications for each of the security requirements given above.
Expert Answer:

Related Book For 

Probability and Stochastic Processes A Friendly Introduction for Electrical and Computer Engineers
ISBN: 978-1118324561
3rd edition
Authors: Roy D. Yates, David J. Goodman
Posted Date:
Students also viewed these computer network questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
DAT, Inc., needs to develop an aggregate plan for its product line. Relevant data are The forecast for next year is Management prefers to keep a constant workforce and production level, absorbing...
-
The distance between an object and its image formed by a diverging lens is 49.0 cm. The focal length of the lens is -233.0 cm. Find (a) The image distance and (b) The object distance.
-
A spherical wave travels such that a crest occurs at radius \(r_{1}\) at instant \(t_{1}\). The same crest has a radius \(r_{2}=2 r_{1}\) at \(t_{2}=2 t_{1}\). (a) What is the wave speed? (b) Where...
-
Indianapolis Auto Parts (IAP) has a Seat Manufacturing Department that uses ABC. IAPs activity cost allocation rates include the following: Suppose Ford has asked for a bid on 50,000 built-in baby...
-
The following accounts, with the balances indicated, appear in the ledger of Codigo Co. on December 1 of the current year: The following transactions relating to payroll, payroll deductions, and...
-
What industry is Airbnb in? Is Airbnb in a risky industry? Why/when Airbnb begin its operations? Has Airbnb announced an IPO, or possibly a SPAC deal, since it received its initial funding? If now...
-
Prepare joumal entries to record the December transactions in the General Journal Tab in the excel template file "Accounting Cycle Excel Template.xlsx". Use the following accounts as appropriate:...
-
Describe your viewpoints around the necessity for/pitfalls of Canada's use of AI in visa processing and immigration after reading the passage below. While the IRCC claims that the use of AI in visa...
-
What political, social or economic factors did influence and continues to influence the corporate governance trends in organizations such as Apple Inc. and Microsoft Corporation? Explain why, how and...
-
1. Calculate the missing amount for each of the following notes receivable. Face Value $15,000 Annual Interest Rate Fraction of the Year 4% $25,000 8% $30,000 8 months 4 months 6% 6 months
-
Use in-text citations and a Reference List in APA format to cite the course resource(s) used - an in-text citation cannot exist without a corresponding Reference List, and a Reference List cannot...
-
Write a leadership essay based on an Interview with a Healthcare Director. Objective of the leadership Interview. Write a Rationale for healthcare Director Selection. Synopsis of the interview....
-
Being an HR manager of any firm you choose, device an outsourcing strategy rather extending boundaries of a firm being sensitive about opportunity costs. Follow the formal systematic process of...
-
Draw the appropriate control flow graph of the given pseudocode.Make sure to only use one number for blocks of code which are all sequential and when the first line is executed, all of those lines...
-
The proof of Theorem 13.3 neglected the first inter-arrival time X1. Show that X1 has an exponential () PDF.
-
A business trip is equally likely to take 2, 3, or 4 (lays. After a d-day trip, the change in the traveler's weight, measured as au integer number of pounds, is a uniform (-d, d) random variable. For...
-
Problem 5.2.6 extended Example 5.3 to a test of n circuits and identified the joint PDF of X, the number of acceptable circuits, and Y, the number of successful tests before the first reject. Write a...
-
Consider a second-order system whose transfer function is in standard form as in Equation 10.7. Assume that the requirements for the system unit-step response are rise time \(t_{\mathrm{r}} \leq 0.1...
-
The transfer function of a dynamic system is given by \[G(s)=\frac{s+4}{s^{5}+2 s^{4}+3 s^{3}+8 s^{2}+4 s+5}\] Determine the stability of the system a. Using Routh's stability criterion without...
-
The unit-step response of a dynamic system is shown in Figure 10.12. Find the transfer function of the system if it can be approximated as \(a /\left(s^{2}+2 \zeta \omega_{n} s+\omega_{n}^{2}...

Study smarter with the SolutionInn App