1. Compare the three cloud computing delivery models, SaaS, PaaS, and laas, from the point of...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
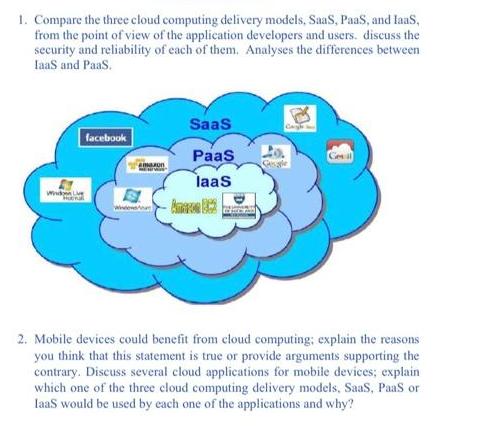
1. Compare the three cloud computing delivery models, SaaS, PaaS, and laas, from the point of view of the application developers and users. discuss the security and reliability of each of them. Analyses the differences between laaS and PaaS. Www facebook SaaS PaaS laas -Amaze 862 20 2. Mobile devices could benefit from cloud computing; explain the reasons you think that this statement is true or provide arguments supporting the contrary. Discuss several cloud applications for mobile devices; explain which one of the three cloud computing delivery models, SaaS, PaaS or IaaS would be used by each one of the applications and why? 1. Compare the three cloud computing delivery models, SaaS, PaaS, and laas, from the point of view of the application developers and users. discuss the security and reliability of each of them. Analyses the differences between laaS and PaaS. Www facebook SaaS PaaS laas -Amaze 862 20 2. Mobile devices could benefit from cloud computing; explain the reasons you think that this statement is true or provide arguments supporting the contrary. Discuss several cloud applications for mobile devices; explain which one of the three cloud computing delivery models, SaaS, PaaS or IaaS would be used by each one of the applications and why?
Expert Answer:
Answer rating: 100% (QA)
1 The three cloud computing delivery models SaaS PaaS and IaaS differ in terms of the level of control and responsibility that the cloud provider and the user have over the infrastructure and applicat... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
what ways can emotional intelligence be cultivated and enhanced through experiential learning, coaching, and feedback mechanisms, and how do individual differences in personality and temperament...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
A rectangular loop of wire 24 cm by 72 cm is bent into an L shape, as shown in FIGURE 23-49. The magnetic field in the vicinity of the loop has a magnitude of 0.035 T and points in a direction...
-
The column is used to support the upper floor. If a force F is applied perpendicular to the handle to tighten the screw, determine the compressive force in the column. The square-threaded screw on...
-
In the financial markets of emerging countries, derivative financial instruments are underdeveloped because there are not enough assets that act as underlyings. How true is this statement?
-
Table 3.4 on page 208 shows the number of points scored and penalty minutes for 24 ice hockey players on the Ottawa Senators NHL team for the 2014-2015 season. The data are also stored in...
-
The customer billing and collection functions of the Misty Company, a small paint manufacturer, are attended to by a receptionist, an accounts receivable clerk, and a cashier who also serves as a...
-
Some time ago my mother in law came to visit us. While visiting, I noticed her talent in knitting beautiful woolen scarves. I asked her if she was interested in selling them in our boutique and she...
-
City Tours Ltd. needs to update the database on a regular basis. As a customer service manager for the company, you need to add new customers and confirmations, update basic costs, delete...
-
Which one of the following is atrue statement? Question 9 options: Most individuals who change occupations in a given year are over 50 years old. Less than 3% of workers change occupations in a given...
-
Decide whether the system in Problem 1 is stable. A linear dynamic system is stable if the homogeneous solution of its mathematical model, subjected to the prescribed initial conditions, decays. More...
-
How does Figure 19.2 support the following statement: "Looking at how countries of different income at any point in time supply environmental quality (the environmental Kuznets curve) does not...
-
In the context of Figure 18.3, suppose that the risk involved with the hazardous waste landfill is objective. This may be because leaks occur often enough that the probability of a leak can be...
-
When rolling a single die, what is the probability that the outcome is 7?
-
In Figure 19.6, the optimum \(\left(E_{0}, C_{0} ight)\) is shown as the point at which the marginal rate of transformation of \(E\) for \(C\) equals the consumer's marginal rate of substitution of...
-
From a deck of five cards numbered 2, 4, 6, 8, and 10, respectively, a card is drawn at random and replaced. This is done three times. What is the probability that the card numbered 2 was drawn...
-
A test car is driven a fixed distance of n miles along a straight highway. (Here n Z+.) The car travels at one mile per hour for the first mile, two miles per hour for the second mile, four miles...
-
I. Describe how symmetric encryption uses the same key, also known as a secret key, to encrypt and decrypt a message. II. Analyze the efficiency of symmetric encryption methods as they only require...
-
I. Assess the need that physical security of information security systems is as important as logical or computer security processes. II. Review the list of the seven most common sources of physical...
-
True or False: Hashing functions require the use of keys.
-
What are the six principles of good governance?
-
On which areas do governing boards focus?
-
What are the three subject matter areas addressed by the COSO Framework?

Study smarter with the SolutionInn App


