a. Write the binary string for the message hello friends. How many bits are needed for...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
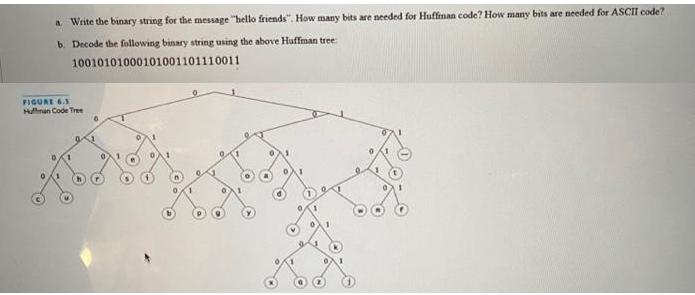
a. Write the binary string for the message "hello friends". How many bits are needed for Huffiman code? How many bits are needed for ASCII code? b. Decode the following binary string using the above Huffman tree: 10010101000101001101110011 FIGURE 6.3 Hunan Code Tree a. Write the binary string for the message "hello friends". How many bits are needed for Huffiman code? How many bits are needed for ASCII code? b. Decode the following binary string using the above Huffman tree: 10010101000101001101110011 FIGURE 6.3 Hunan Code Tree
Expert Answer:
Answer rating: 100% (QA)
a Write the binary string for the message hello friends How many bits are needed for Huffman code How many bits are needed for ASCII code The binary s... View the full answer

Related Book For 

Introduction To Java Programming And Data Structures Comprehensive Version
ISBN: 9780136520238
12th Edition
Authors: Y. Daniel Liang
Posted Date:
Students also viewed these programming questions
-
1. A digital computer has a memory unit with 48 bits per word. The instruction set consists of 240 different operations. All instructions have an operation code part (opcode) and an address part...
-
Lets assume you have been offered a job by Jekyll Corporation, a company in the consumer products industry. The job is in your chosen career path. Jekyll Corporation has offered you a position that...
-
The distance between a carbon atom (mC = 12 u) and an oxygen atom (mO = 16 u) in the CO molecule is 1.13 X 10-10 m. How far from the carbon atom is the center of mass of the molecule?
-
In your own words, discuss the integrated marketing communications concept. Explain what its emphasis on consistent and complete messages implies with respect to promotion blends.
-
Determine if the mixed method aspect is concurrent, sequential,, or nested. Develop a hypothetical research scenario that would necessitate the use of the Mixed Method A-B-A Design. The research will...
-
Analysis of Installment-Sales Accounts Samuels Co. appropriately uses the installment-sales method of accounting. On December 31, 2012, the books show balances as follows. Instructions (a) Prepare...
-
Beddington and May (1982) have proposed the following model to study the interactions between baleen whales and their main food source, krill (a small shrimp-like animal), in the southern ocean: - x...
-
What Are Empirical/Research Articles? Describe the resource assigned to you including two examples of how this resource will support your successful completion of the capstone project?
-
2011-2012 Losses Rs. 10, 000, The Profits & losses for the last years are: 2012-2013 Losses Rs. 2,500 2013-2014 Profits Rs. 98, 000 2014-2015 Profits Rs. 76,000 average capital employed in the...
-
Evaluate: lim, 0 4a - 2x sin a
-
Beths Lawn Mowing Service acts as a monopoly. The prevailing market price equation is given by P = 20 - 0.2q where q represents one acre of lawn. Cost equations are as follows: Total Cost = 0.1 q 2 +...
-
Anfield Albion is preparing for the next season of English Premier League, the most watched sports league in the world, broadcast in 212 territories to 643 million homes and a potential TV audience...
-
Given two utility functions U(x, y) = x 2/3 y 4/5 and U(x, y) = x 2 + y, with Px = 2, Py = 1, budget is 10 unit, show the consumer choice respectively.
-
A solid metal sphere of radius a = 2.5 cm has a net charge Qin = -3 nC (1 nC = 10^{-9)C). The sphere is surrounded by a concentric conducting spherical shell of inner radius b = 6 cm and outer radius...
-
If R is the event that a convict committed armed robbery and D is the event that the convict pushed dope, state in words what probabilities are expressed by (a) P(R|D); (b)P(D'|R); (c)P(R'|D');...
-
As indicated by mutual fund flows, investors tend to beat the market seek safety invest in last year's winner invest in last years loser
-
Rewrite Programming Exercise 7.3 using streams. Data from Programming Exercise 7.3 Write a program that reads the integers between 1 and 100 and counts the occurrences of each. Assume the input ends...
-
Write a program that demonstrates the properties of a text area. The program uses a check box to indicate whether the text is wrapped onto next line, as shown in Figure 16.41a. Exercise16 12 Four...
-
Rewrite the preceding servlet. Assume for each class, a table is used to store the student name, ssn, and score. The table name is the same as the class ID. For instance, if the class ID were...
-
Might it be desirable to use a combination of team-based and individual incentives at Lakeside Utility Company? How might such a plan be structured? Lakeside Utility Company provides electrical power...
-
Students form pairs. One student takes the role of Pamela Johnson; the other, the role of an HRM consultant Johnson has hired to help her decide what to do next. Role-play the meeting between the...
-
This experiential exercise involves a group of six students. One will be a manager and five will be part of a team that has worked closely together during the past year. A bonus of $12,000 is to be...

Study smarter with the SolutionInn App