Given a set of n numbers, your task is to create a doubly linked list for...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
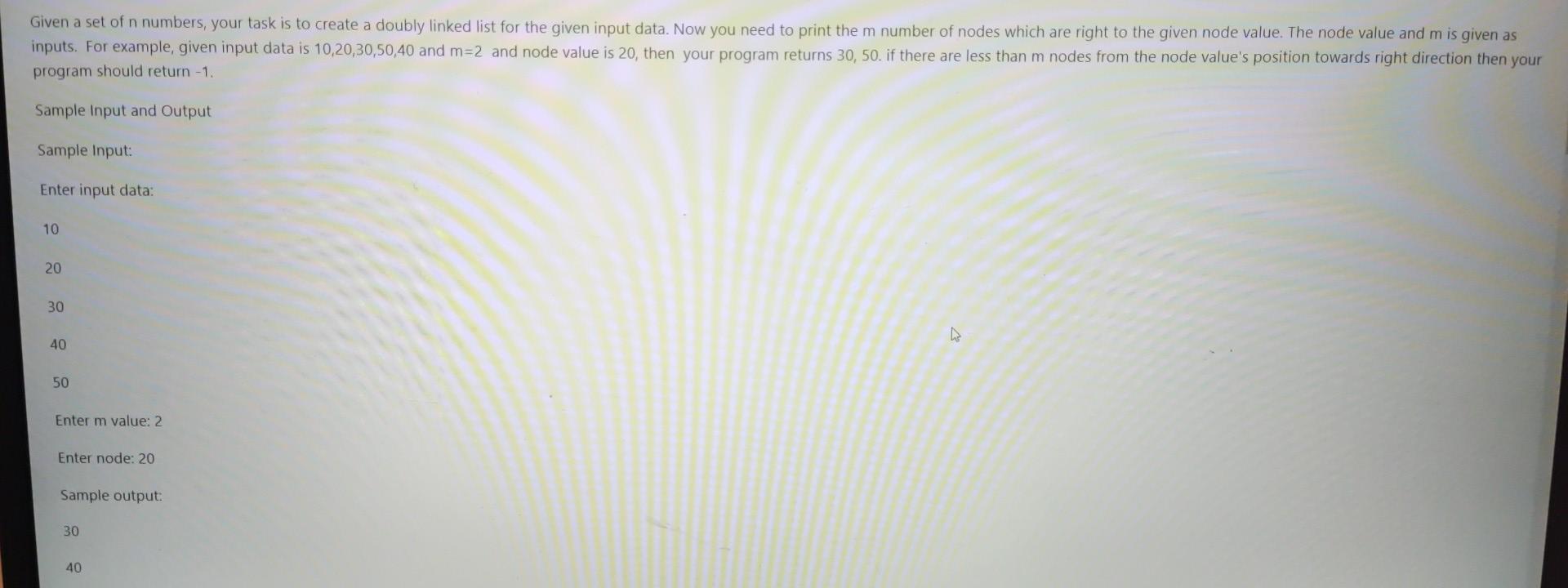
Given a set of n numbers, your task is to create a doubly linked list for the given input data. Now you need to print the m number of nodes which are right to the given node value. The node value and m is given as inputs. For example, given input data is 10,20,30,50,40 and m=2 and node value is 20, then your program returns 30, 50. if there are less than m nodes from the node value's position towards right direction then your program should return -1. Sample Input and Output Sample Input: Enter input data: 10 20 30 40 50 Enter m value: 2 Enter node: 20 Sample output: 30 40 D Given a set of n numbers, your task is to create a doubly linked list for the given input data. Now you need to print the m number of nodes which are right to the given node value. The node value and m is given as inputs. For example, given input data is 10,20,30,50,40 and m=2 and node value is 20, then your program returns 30, 50. if there are less than m nodes from the node value's position towards right direction then your program should return -1. Sample Input and Output Sample Input: Enter input data: 10 20 30 40 50 Enter m value: 2 Enter node: 20 Sample output: 30 40 D
Expert Answer:
Answer rating: 100% (QA)
Python class Node def initself data selfdata data selfprev None selfnext None de... View the full answer

Related Book For 

Introduction to Algorithms
ISBN: 978-0262033848
3rd edition
Authors: Thomas H. Cormen, Charles E. Leiserson, Ronald L. Rivest
Posted Date:
Students also viewed these programming questions
-
Let f(x)=-53+4. Evaluate f(-1) without using a calculator. Do not include 'f(-1)='in your answer.
-
Your task is to create a game where the users can play with words and numbers. The game has three consecutive levels (Level 1, Level 2, and Level 3). Users can proceed to the next level after...
-
Ann Carter, Chief Financial Officer of Consolidated Electric Company (Con El), must make a recommendation to Con Els board of directors regarding the firms dividend policy. Con El owns two...
-
c++. error: array must be initialized with a brace enclosed initializer main.cpp X 10 11 ii 12 13 14 4567 15 16 17 18 19 287288285 20 21 23 24 25 26 27 28 25285922223288 30 31 33 34 36 37 40 41 42 43...
-
What are the obligations of the acquirer and target firms according to Section 14(d) of the Williams Act?
-
A 30-year, $250,000 mortgage has a rate of 5.4 percent. What are the interest and principal portions in the first payment? In the second?
-
Find the = 0.05 critical value for the chi-square statistic with 14 degrees of freedom.
-
Plot the vapour pressure data for a mixture of benzene (B) and acetic acid (A) given below and plot the vapour pressure/composition curve for the mixture at 50e. Then confirm that Raoult's and...
-
What are the implications of emotional intelligence for leader-member exchanges and organizational effectiveness, particularly in high-stress work environments ?
-
Design the 4-to-1 MUX two ways Write a Verilog module called mux4to1 to implement 4-to-1 multiplexer using functional descriptions and if-else blocks. Write another Verilog module called...
-
Which of the following is not a correct statement? A . Memorandum controlled by the Articles B . Memorandum states the objects while Articles provide the manner in which objects may be attained C ....
-
Share the ABC Widgets with a friend, colleague, or a member of your family. Explain how to calculate the ratios and what they mean. Talk about actions that could be taken to improve these numbers....
-
A company licenses a new enterprise resource planning ("ERP") system in hopes that the system will better help the company manage its HR, accounting, inventory tracking, purchasing, and customer...
-
Briefly summarize the difference of viewing communication across a network from an inter-layer or intra-layer viewpoint. Which view point do you think a network professional that is troubleshooting a...
-
Summarize your DMZ breach simulation results , highlighting what you found to be the greatest concerns from a network monitoring perspective .
-
Ticket Reseller An online flight ticket seller (similar to Expedia) sells a flight to a customer for $300. Prior to selling the ticket to the customer, the ticket seller purchased the ticket from the...
-
The elements of a 3 x 3 matrix A are the products of its row and column indices A.; = ij (where i, j = 1,2,3). The eigenvalues of A are- (A) (7,7,0) (B) (7,4, 3) (C) (D) (14,0,0) 14 14 14 3'3'3 (0)
-
H Corporation has a bond outstanding. It has a coupon rate of 8 percent and a $1000 par value. The bond has 6 years left to maturity but could be called after three years for $1000 plus a call...
-
Another way to evaluate a polynomial A(x) of degree-bound n at a given point x 0 is to divide A(x) by the polynomial (x x 0 ), obtaining a quotient polynomial q(x) of degree-bound n 1 and a...
-
Show that after all edges are processed by CONNECTED-COMPONENTS, two vertices are in the same connected component if and only if they are in the same set.
-
Give a non recursive algorithm that performs an in order tree walk. An easy solution uses a stack as an auxiliary data structure. A more complicated, but elegant, solution uses no stack but assumes...
-
The auditor's report may be addressed to any of the following except the client's a. Stockholders. b. Board of directors. c. Chief executive officer. d. Partners.
-
The standard audit report includes all of the following except a (an) a. Opinion paragraph. b. Scope paragraph. c. Explanatory paragraph. d. Opening paragraph.
-
The existence of audit risk is recognized by the statement in the auditor's standard report that the a. Auditor is responsible for expressing an opinion on the financial statements, which are the...

Study smarter with the SolutionInn App