Cryptography - Cryptography is the art of writing or solving codes (en.oxforddictionaries.com). - In this assignment,...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
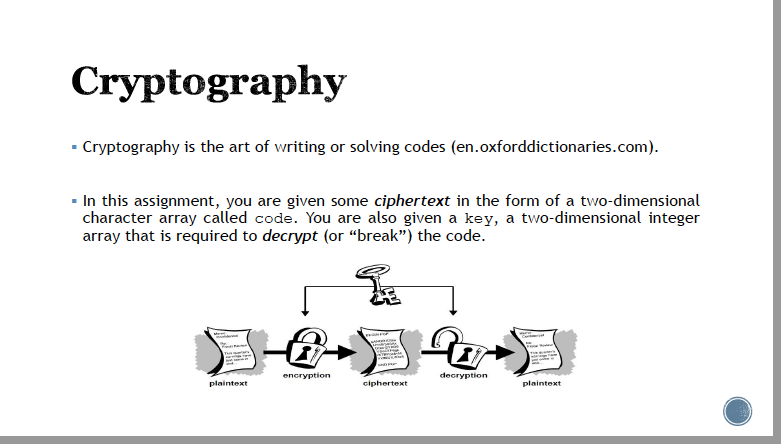
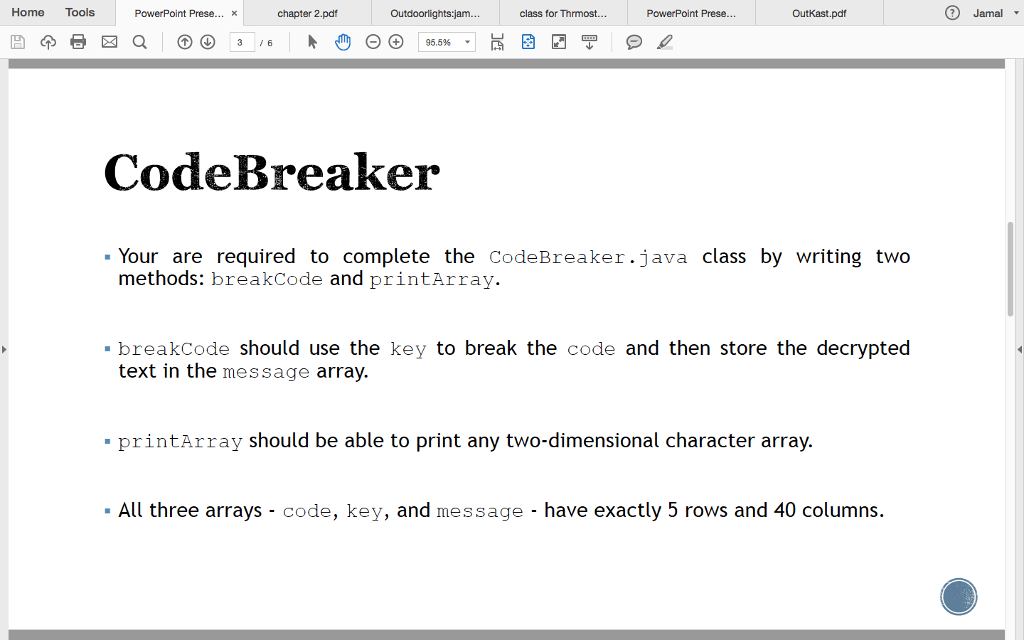
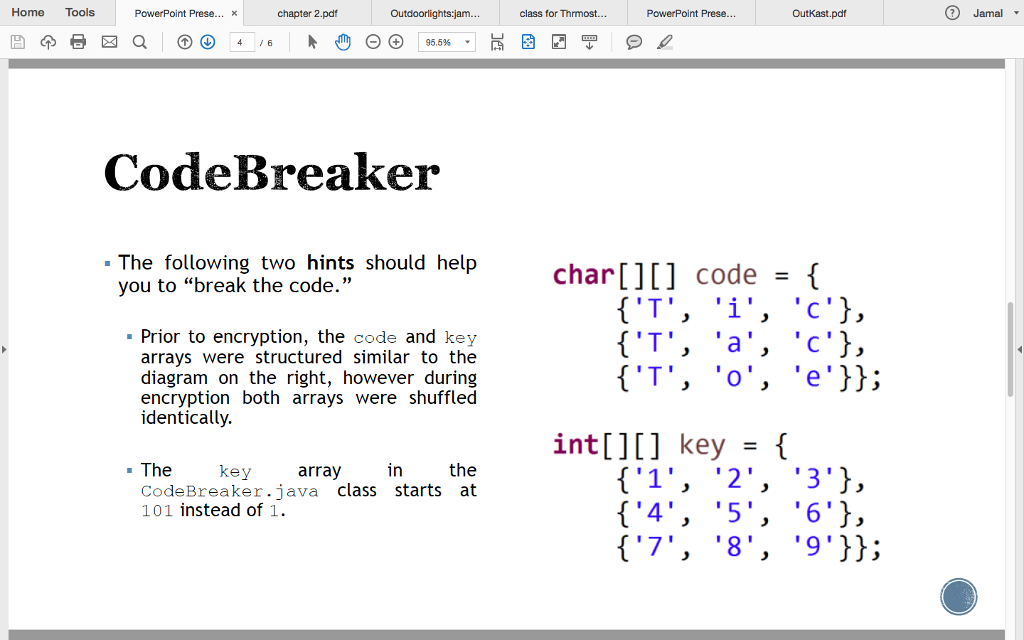
Cryptography - Cryptography is the art of writing or solving codes (en.oxforddictionaries.com). - In this assignment, you are given some ciphertext in the form of a two-dimensional character array called code. You are also given a key, a two-dimensional integer array that is required to decrypt (or "break") the code. plaintext encryption ciphertext 2 decryption plaintext Home Tools 3 a PowerPoint Prese... x 3 /6 chapter 2.pdf Outdoorlights:jam... (-) (+) 95.5% class for Thrmost... ✔ PowerPoint Prese... Outkast.pdf CodeBreaker ▪ Your are required to complete the CodeBreaker.java class by writing two methods: breakCode and printArray. ▪ breakCode should use the key to break the code and then store the decrypted text in the message array. ▪ printArray should be able to print any two-dimensional character array. ▪ All three arrays - code, key, and message - have exactly 5 rows and 40 columns. Jamal ▾ Home Tools 3 a PowerPoint Prese... x /6 chapter 2.pdf ▪ The Outdoorlights:jam... CodeBreaker - The following two hints should help you to "break the code." (-) (+) 95.5% ▪ Prior to encryption, the code and key arrays were structured similar to the diagram on the right, however during encryption both arrays were shuffled identically. key in the CodeBreaker.java class starts at 101 instead of 1. array class for Thrmost... ✔ PowerPoint Prese... Outkast.pdf char[][] code = { {'T', 'i', 'c'}, {'T', 'a', 'c'}, {'T', 'o', 'e'}}; int[][] key = { {'1', '2', '3'}, {'4', '5', '6'}, {'7', '8', '9'}}; Jamal ▾ Cryptography - Cryptography is the art of writing or solving codes (en.oxforddictionaries.com). - In this assignment, you are given some ciphertext in the form of a two-dimensional character array called code. You are also given a key, a two-dimensional integer array that is required to decrypt (or "break") the code. plaintext encryption ciphertext 2 decryption plaintext Home Tools 3 a PowerPoint Prese... x 3 /6 chapter 2.pdf Outdoorlights:jam... (-) (+) 95.5% class for Thrmost... ✔ PowerPoint Prese... Outkast.pdf CodeBreaker ▪ Your are required to complete the CodeBreaker.java class by writing two methods: breakCode and printArray. ▪ breakCode should use the key to break the code and then store the decrypted text in the message array. ▪ printArray should be able to print any two-dimensional character array. ▪ All three arrays - code, key, and message - have exactly 5 rows and 40 columns. Jamal ▾ Home Tools 3 a PowerPoint Prese... x /6 chapter 2.pdf ▪ The Outdoorlights:jam... CodeBreaker - The following two hints should help you to "break the code." (-) (+) 95.5% ▪ Prior to encryption, the code and key arrays were structured similar to the diagram on the right, however during encryption both arrays were shuffled identically. key in the CodeBreaker.java class starts at 101 instead of 1. array class for Thrmost... ✔ PowerPoint Prese... Outkast.pdf char[][] code = { {'T', 'i', 'c'}, {'T', 'a', 'c'}, {'T', 'o', 'e'}}; int[][] key = { {'1', '2', '3'}, {'4', '5', '6'}, {'7', '8', '9'}}; Jamal ▾
Expert Answer:

Related Book For 

A Concise Introduction to Logic
ISBN: 978-1305958098
13th edition
Authors: Patrick J. Hurley, Lori Watson
Posted Date:
Students also viewed these electrical engineering questions
-
Datefunction in R but some odd reason i am getting the following: Using this code: My date transforms into the following: And all i wanted to look like is the same, but what i am tryingto do is...
-
Brenda: Seth, I am trying to help you here. But there is no way that I can pay you $230 per unit. I have competitive bids from other vendors for about $170, and that difference means $1,200,000 in my...
-
How to fix it and get rid of the error message? < SAP Q at > Type Item Msg. Area MT 10 609 VL E 20 609 VL E 60 Technical Information i Help 2 B Cancel Goods movement: Error log More 0 02 AO LO...
-
Figure shows a cycle consisting of five paths: AB is isothermal at 300 K, BC is adiabatic with work = 5.0 J, CD is at a constant pressure of 5 atm, D E is isothermal, and EA is adiabatic with a...
-
1. In our simple model, if C = 100 + 0.8y, and I = 50, equilibrium output will be ______. 2. If in Exercise 3.1 I increase to 100, a. The equilibrium income will be ______. b. The multiplier is...
-
Devin Wolf Company has the following balances in selected accounts on December 31, 2020. Accounts Receivable ...............................................$ 0 Accumulated DepreciationEquipment...
-
What ethical rules must be followed by paralegals? What are the goals of the ethical rules?
-
Staybrite Electronics Co. amended its pension plan effective January 1, 2011. The increase in the PBO occurring as a result of the plan amendment is $6,290,000. Staybrite arranged to fund the prior...
-
The following information relates to the pension plan for the employees of Sheridan Company: 1/1/25 12/31/25 12/31/26 Accum. benefit obligation $9740000 $10160000 $13100000 Projected benefit...
-
A factory has five assembly lines. Each assembly line is down (not working) p percent of the time. What must p equal so that there is a 95 percent chance that at least one assembly line is working?
-
Bushman et al. concluded from their study on aggression in married couples that relationships could be improved by: a. mandatory sentencing guidelines and resources for those accused of domestic...
-
1. 2. The spot exchange rate is $1.50/. The three-month forward exchange rate is $1.52/. The 3-month interest rate is 8.0% per annum in the U.S. and 5.8% per annum in the U.K. Investors can borrow...
-
Two students collect baseball cards. Shushu has 210 cards, and Vivak has 160 cards. Shushy adds 8 new cards to her collection each month, and Vivak adds 13 new cards each month. After how many months...
-
Lawrence Kohlberg's theory of moral development consists of three main stages. At the preconventional level, moral reasoning is related to the physical consequences of an act. An action is considered...
-
Find the following for the company Capital One Calculate the total return of the company and separating out the income and capital appreciation components Calculation and understanding of the...
-
Compute ending work in process inventory for a manufacturer using the following information. Raw materials purchased Direct materials used Direct labor used Factory overhead Work in process...
-
The applicant, Mr. Shaun Sun, he is 28 years old and was born in China in 1992. He came to Canada under a student visa in 2017, then graduated from Seneca college with diploma in 2019. After...
-
Refer to the data for problem 13-36 regarding Long Beach Pharmaceutical Company. Required: Compute each division's residual income for the year under each of the following assumptions about the...
-
Use indirect truth tables to determine whether the following arguments are valid or invalid.
-
If stem-cell research is restricted, then future cures will not materialize. If future cures do not materialize, then people will die prematurely. Therefore, if stem-cell research is restricted, then...
-
Use conditional proof and the eighteen rules of inference to derive the conclusions of the following symbolized arguments. Having done so, attempt to derive the conclusions without using conditional...
-
The board of directors of the Canadian Red Cross is having its regular quarterly meeting. Accounting policies are on the agenda, and depreciation is being discussed. A new board member, a social...
-
On January 2, 2018, Yuki Sporting Goods Ltd. purchased branding equipment at a cost of \(\$ 63,000\). Before placing the equipment in service, the company spent \(\$ 2,200\) for delivery, \(\$...
-
CrossCanada Transport Inc. (CC) provides warehouse and distribution services. The excerpts that follow are adapted from CC's financial statements for fiscal year 2020. {Requirements} 1. How much was...

Study smarter with the SolutionInn App


