Let F2 = {0, 1} with the usual arithmetic modulo 2. The set F2 = {0,1}...
Fantastic news! We've Found the answer you've been seeking!
Question:

Transcribed Image Text:
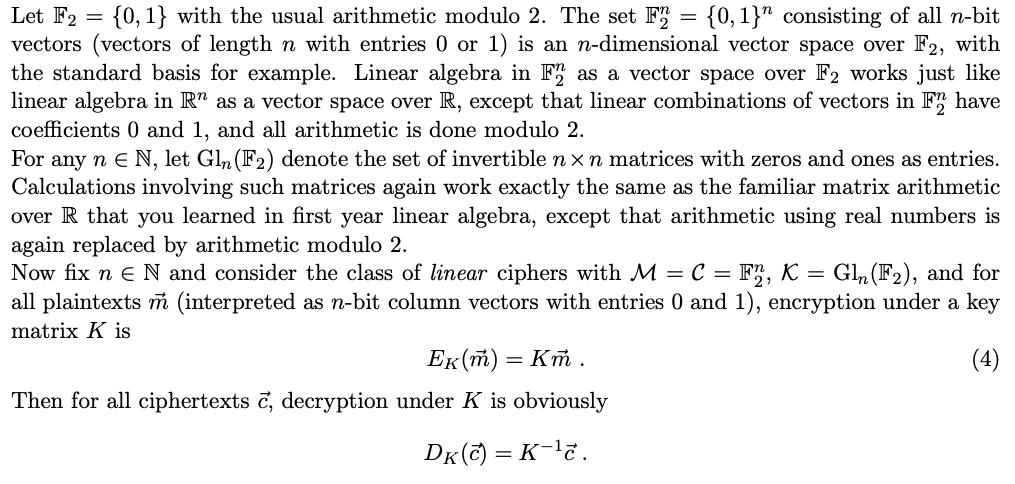
Let F2 = {0, 1} with the usual arithmetic modulo 2. The set F2 = {0,1}" consisting of all n-bit vectors (vectors of length n with entries 0 or 1) is an n-dimensional vector space over F2, with the standard basis for example. Linear algebra in F2 as a vector space over F2 works just like linear algebra in R" as a vector space over R, except that linear combinations of vectors in F2 have coefficients 0 and 1, and all arithmetic is done modulo 2. For any n E N, let Gln (F2) denote the set of invertible nxn matrices with zeros and ones as entries. Calculations involving such matrices again work exactly the same as the familiar matrix arithmetic over R that you learned in first year linear algebra, except that arithmetic using real numbers is again replaced by arithmetic modulo 2. Now fix n E N and consider the class of linear ciphers with M = C = F2, K = Gln (F), and for all plaintexts m (interpreted as n-bit column vectors with entries 0 and 1), encryption under a key matrix K is (4) Ek(m) = Km. Then for all ciphertexts c, decryption under K is obviously DK(C) = K-c. Let F2 = {0, 1} with the usual arithmetic modulo 2. The set F2 = {0,1}" consisting of all n-bit vectors (vectors of length n with entries 0 or 1) is an n-dimensional vector space over F2, with the standard basis for example. Linear algebra in F2 as a vector space over F2 works just like linear algebra in R" as a vector space over R, except that linear combinations of vectors in F2 have coefficients 0 and 1, and all arithmetic is done modulo 2. For any n E N, let Gln (F2) denote the set of invertible nxn matrices with zeros and ones as entries. Calculations involving such matrices again work exactly the same as the familiar matrix arithmetic over R that you learned in first year linear algebra, except that arithmetic using real numbers is again replaced by arithmetic modulo 2. Now fix n E N and consider the class of linear ciphers with M = C = F2, K = Gln (F), and for all plaintexts m (interpreted as n-bit column vectors with entries 0 and 1), encryption under a key matrix K is (4) Ek(m) = Km. Then for all ciphertexts c, decryption under K is obviously DK(C) = K-c.
Expert Answer:
Answer rating: 100% (QA)
Introduction The above text describes a linear cipher with plaintext and ciphertext spaces being the ... View the full answer

Related Book For 

Introduction to Algorithms
ISBN: 978-0262033848
3rd edition
Authors: Thomas H. Cormen, Charles E. Leiserson, Ronald L. Rivest
Posted Date:
Students also viewed these mathematics questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
List three specific parts of the Case Guide, Objectives and Strategy Section (See below) that you had the most difficulty understanding. Describe your current understanding of these parts. Provide...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
You plan to "go green" and install solar panels on your home in 36 months. The solar company has a payment plan whereby you will pay for the panels in 120 monthly payments (installments) starting in...
-
To ensure highway safety and protect driver health, Congress charged federal agencies with regulating the hours of service of commercial motor vehicle operators. Between 1940 and 2003, the...
-
Solve the given quadratic equations by factoring. bx 2 b = x b 2 x
-
In 1940, the family of Thomas Back entered into an oil-and-gas lease with the Inland Gas Corporation. The lease held that Inland would pay to Backs family 12 cents per thousand cubic feet of gas...
-
Horvath Company uses an imprest petty cash system. The fund was established on March 1 with a balance of $100. During March, the following petty cash receipts were found in the petty cash box. The...
-
There are dozens of potentially relevant financial ratios that can be employed in an analysis of competitive firms (e.g. return on assets, earnings per share, etc.) This assignment requires that four...
-
The OLTP system data for the Fitchwood Insurance Company is in a series of flat files. What process do you envision would be needed in order to extract the data and create the ERD shown in Figure...
-
Edwin is a maintenance worker at a home for the elderly. He feels valued at his workplace, especially since Covid 19, when the cleanliness of the place came under intense scrutiny. The duties Edwin...
-
How do demographic shifts, such as aging populations and urbanization, reshape social structures and demand innovative approaches to address emerging societal needs, such as healthcare, housing, and...
-
define each word and give example in a sentences. Family Law "DOMA" Common Law Marriage Adoption Common-Law Title States Community-Property States Spousal privilege Annulment Legal Separation...
-
1. Why is the reaction in persuasive communication a measure of the success or failure of the communication made by the source in achieving its goals? 2. What must a persuadee do to establish a...
-
How do demographic trends, such as changing family structures and population aging, impact mobility patterns, and what implications do these trends have for intergenerational equity and social...
-
A portfolio has 30% of its value in Company A and the rest in Company B. The volatitly of Company A and B are 25% and 33%, respectively, and the correlation between both companies is 0.6. what is the...
-
What will be the cell potential for a Cu?Zn galvanic cell with[Zn2+]=0.1 M and the [Cu2+]=0.01 M? What will be the cell potential for a galvanic cellwith and the ? A) 1.10 V b) 1.13 V c) 1.04 V d)...
-
The Dow Jones Industrial Average reached a high of $ 7801.63 on December 29, 1997. Recall from Example 18.4 that it reached a high of $ 1003 on November 14, 1972. The Consumer Price Index for...
-
Professor Bacon claims that the algorithm for strongly connected components would be simpler if it used the original (instead of the transpose) graph in the second depth-first search and scanned the...
-
Show how to implement an FFT algorithm with the bit-reversal permutation occurring at the end, rather than at the beginning, of the computation.
-
The square of a directed graph G = (V, E) is the graph G 2 = (V, E 2 ) such that (u, ) E 2 if and only G contains a path with at most two edges between u and . Describe efficient algorithms for...
-
Determine whether each of the following items is an: (a) Cash (b) Dividend to shareholders (c) Land (d) Accounts payable (e) Capital stock (f) Notes payable (g) Accounts receivable (h) Salaries (i)...
-
Assuming the expectations theory is the correct theory of the term structure, calculate the interest rates in the term structure for maturities of one to four years, and plot the resulting yield...
-
Assuming the expectations theory is the correct theory of the term structure, calculate the interest rates in the term structure for maturities of one to four years, and plot the resulting yield...

Study smarter with the SolutionInn App