Let's examine the 32-bit hexadecimal value Oxacfe2b7a a) Provide the binary representation of this number in...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
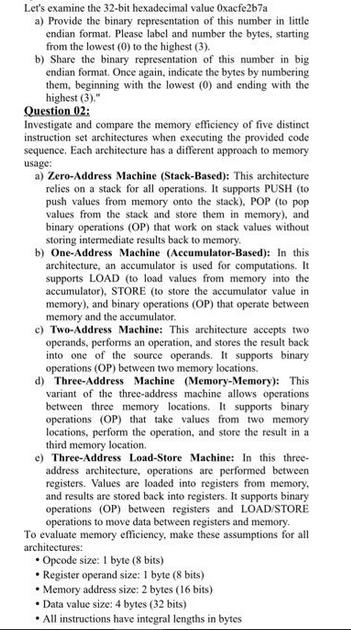
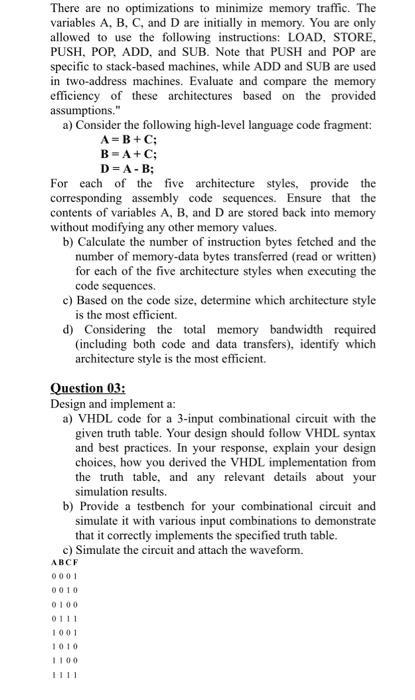
Let's examine the 32-bit hexadecimal value Oxacfe2b7a a) Provide the binary representation of this number in little endian format. Please label and number the bytes, starting from the lowest (0) to the highest (3). b) Share the binary representation of this number in big endian format. Once again, indicate the bytes by numbering them, beginning with the lowest (0) and ending with the highest (3)." Question 02: Investigate and compare the memory efficiency of five distinct instruction set architectures when executing the provided code sequence. Each architecture has a different approach to memory usage: a) Zero-Address Machine (Stack-Based): This architecture relies on a stack for all operations. It supports PUSH (to push values from memory onto the stack), POP (to pop values from the stack and store them in memory), and binary operations (OP) that work on stack values without storing intermediate results back to memory. b) One-Address Machine (Accumulator-Based): In this architecture, an accumulator is used for computations. It supports LOAD (to load values from memory into the accumulator), STORE (to store the accumulator value in memory), and binary operations (OP) that operate between memory and the accumulator. c) Two-Address Machine: This architecture accepts two operands, performs an operation, and stores the result back into one of the source operands. It supports binary operations (OP) between two memory locations. d) Three-Address Machine (Memory-Memory): This variant of the three-address machine allows operations between three memory locations. It supports binary operations (OP) that take values from two memory locations, perform the operation, and store the result in a third memory location. e) Three-Address Load-Store Machine: In this three- address architecture, operations are performed between registers. Values are loaded into registers from memory. and results are stored back into registers. It supports binary operations (OP) between registers and LOAD/STORE operations to move data between registers and memory. To evaluate memory efficiency, make these assumptions for all architectures: Opcode size: 1 byte (8 bits) Register operand size: 1 byte (8 bits) Memory address size: 2 bytes (16 bits) Data value size: 4 bytes (32 bits) All instructions have integral lengths in bytes There are no optimizations to minimize memory traffic. The variables A, B, C, and D are initially in memory. You are only allowed to use the following instructions: LOAD, STORE, PUSH, POP, ADD, and SUB. Note that PUSH and POP are specific to stack-based machines, while ADD and SUB are used in two-address machines. Evaluate and compare the memory efficiency of these architectures based on the provided assumptions." a) Consider the following high-level language code fragment: A=B+C; B=A+C; D=A-B; For each of the five architecture styles, provide the corresponding assembly code sequences. Ensure that the contents of variables A, B, and D are stored back into memory without modifying any other memory values. b) Calculate the number of instruction bytes fetched and the number of memory-data bytes transferred (read or written) for each of the five architecture styles when executing the code sequences. c) Based on the code size, determine which architecture style is the most efficient. d) Considering the total memory bandwidth required (including both code and data transfers), identify which architecture style is the most efficient. Question 03: Design and implement a: a) VHDL code for a 3-input combinational circuit with the given truth table. Your design should follow VHDL syntax and best practices. In your response, explain your design choices, how you derived the VHDL implementation from the truth table, and any relevant details about your simulation results. b) Provide a testbench for your combinational circuit and simulate it with various input combinations to demonstrate that it correctly implements the specified truth table. c) Simulate the circuit and attach the waveform. ABCF 0001 0010 0100 0111 1001 1010 Let's examine the 32-bit hexadecimal value Oxacfe2b7a a) Provide the binary representation of this number in little endian format. Please label and number the bytes, starting from the lowest (0) to the highest (3). b) Share the binary representation of this number in big endian format. Once again, indicate the bytes by numbering them, beginning with the lowest (0) and ending with the highest (3)." Question 02: Investigate and compare the memory efficiency of five distinct instruction set architectures when executing the provided code sequence. Each architecture has a different approach to memory usage: a) Zero-Address Machine (Stack-Based): This architecture relies on a stack for all operations. It supports PUSH (to push values from memory onto the stack), POP (to pop values from the stack and store them in memory), and binary operations (OP) that work on stack values without storing intermediate results back to memory. b) One-Address Machine (Accumulator-Based): In this architecture, an accumulator is used for computations. It supports LOAD (to load values from memory into the accumulator), STORE (to store the accumulator value in memory), and binary operations (OP) that operate between memory and the accumulator. c) Two-Address Machine: This architecture accepts two operands, performs an operation, and stores the result back into one of the source operands. It supports binary operations (OP) between two memory locations. d) Three-Address Machine (Memory-Memory): This variant of the three-address machine allows operations between three memory locations. It supports binary operations (OP) that take values from two memory locations, perform the operation, and store the result in a third memory location. e) Three-Address Load-Store Machine: In this three- address architecture, operations are performed between registers. Values are loaded into registers from memory. and results are stored back into registers. It supports binary operations (OP) between registers and LOAD/STORE operations to move data between registers and memory. To evaluate memory efficiency, make these assumptions for all architectures: Opcode size: 1 byte (8 bits) Register operand size: 1 byte (8 bits) Memory address size: 2 bytes (16 bits) Data value size: 4 bytes (32 bits) All instructions have integral lengths in bytes There are no optimizations to minimize memory traffic. The variables A, B, C, and D are initially in memory. You are only allowed to use the following instructions: LOAD, STORE, PUSH, POP, ADD, and SUB. Note that PUSH and POP are specific to stack-based machines, while ADD and SUB are used in two-address machines. Evaluate and compare the memory efficiency of these architectures based on the provided assumptions." a) Consider the following high-level language code fragment: A=B+C; B=A+C; D=A-B; For each of the five architecture styles, provide the corresponding assembly code sequences. Ensure that the contents of variables A, B, and D are stored back into memory without modifying any other memory values. b) Calculate the number of instruction bytes fetched and the number of memory-data bytes transferred (read or written) for each of the five architecture styles when executing the code sequences. c) Based on the code size, determine which architecture style is the most efficient. d) Considering the total memory bandwidth required (including both code and data transfers), identify which architecture style is the most efficient. Question 03: Design and implement a: a) VHDL code for a 3-input combinational circuit with the given truth table. Your design should follow VHDL syntax and best practices. In your response, explain your design choices, how you derived the VHDL implementation from the truth table, and any relevant details about your simulation results. b) Provide a testbench for your combinational circuit and simulate it with various input combinations to demonstrate that it correctly implements the specified truth table. c) Simulate the circuit and attach the waveform. ABCF 0001 0010 0100 0111 1001 1010
Expert Answer:
Answer rating: 100% (QA)
a The binary representation of the 32bit hexadecimal value 0xacfe2b7a in littleendian format ... View the full answer

Related Book For 

Building Java Programs A Back To Basics Approach
ISBN: 9780135471944
5th Edition
Authors: Stuart Reges, Marty Stepp
Posted Date:
Students also viewed these programming questions
-
Explain the superfluous use of x-ray in products and entertainment in the years immediately after their discovery and announcement. Describe the role played by computer technology in x-ray imaging.
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Case Study: Quick Fix Dental Practice Technology requirements Application must be built using Visual Studio 2019 or Visual Studio 2017, professional or enterprise. The community edition is not...
-
Write Python program which implements the following two classical cryptosystem a) Affine Cipher b) Vigenere Cipher Your program should consist of at least five functions: a) Two functions named...
-
Show that the gamma density function integrates to f(x, , r) integrates to 1.
-
Suppose you wish to store utility bills for a large number of users, where each bill is identified by a customer ID and a date. How would you store the bills in a key-value store that supports range...
-
Could an include use case have an extend use case? Explain by providing an example.
-
In the following figure, a consumer is initially in equilibrium at point C. The consumers income is $ 400, and the budget line through point C is given by $ 400 $ 100X + $ 200Y. When the consumer is...
-
3) (10 pts) Write a function NextMinute that receives one integer as the input argument, which is the current minute of the hour, and returns the next minute as the output argument. Please note that...
-
55 Jason Ready, single, attended the University of San Diego during 2015-2019 under the Army ROTC program. Excluding the school expenses covered by his ROTC scholarship, he incurred additional school...
-
What are the best Distribution for High-Performance Computing? Q2. What is GPU and what is the architecture of GPU? Q3. Difference between CPU and GPU? Q4. What are the uses for GPUs other than...
-
Case Scenario Please choose ONE (1) listed company in any industry of your choice in India. You may refer to this link for listed companies in India....
-
CST8116 Lab Exercise 04 (225) Instructions The five parts of the Software Development Process as presented by Cay Horstmann [1] will be used as the basis for this lab exercise. 1) Understand the...
-
I need help with this javascript assignment I fixed the code already but still get error after I test? if the problem with my visual studio code so what the website compiler I can use to fix this...
-
Ming has income m and the utility function u(x1, x2) = 8x1 - (x1)+ x2 where and 2 are the quantities of the two goods consumed. The price of good 1 is p and the price of good 2 is p2 = 1. (a) Find...
-
A firm has the production function f(x1, x2) = 4(x1)x2 + 2-3. The price of input 1 is w, the price of input 2 is w2 = 1 and the price of output is p. (a) Find the marginal product of input 1.
-
1. Explain how the terms AROC, IROC, secants, tangents, and limits connect to the concept of rate of change and the first principles definition of a derivative using a polynomial as an example. Be...
-
For what reason might an exporter use standard international trade documentation (letter of credit, draft, order bill of lading) on an intrafirm export to its parent or sister subsidiary?
-
Write a method in the HashIntSet class called addAll that accepts another hash set as a parameter and adds all of the elements from the other set into the current set. For example, if the set stores...
-
Write an inheritance hierarchy of three-dimensional shapes. Make a top-level shape interface that has methods for getting information such as the volume and surface area of a three-dimensional shape....
-
Why is an iterator especially useful with linked lists?
-
Henry Ford, founder of Ford Motor Company, is quoted as saying that customers could choose a car in any color as long as it was black. Things have come a long way since that timewhen customization...
-
Not long ago, New England Confectionery Company, or Necco for short, marked the production of its one trillionth candy wafer. The humble roots of Necco, the country's oldest continuously operating...
-
What is utility?

Study smarter with the SolutionInn App