Linux (and Unix) permit files to have holes in them. A hole can be created by...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
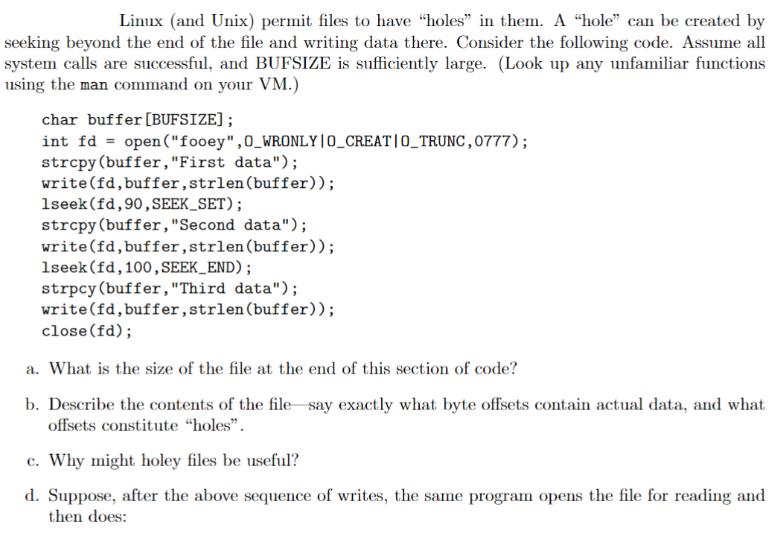
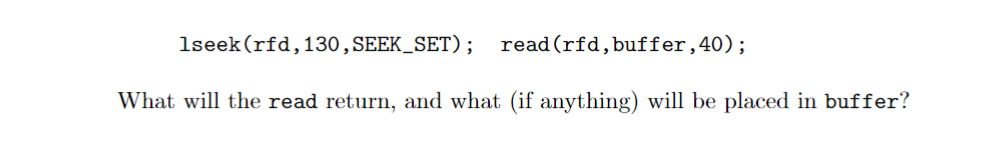
Linux (and Unix) permit files to have "holes" in them. A "hole" can be created by seeking beyond the end of the file and writing data there. Consider the following code. Assume all system calls are successful, and BUFSIZE is sufficiently large. (Look up any unfamiliar functions using the man command on your VM.) char buffer [BUFSIZE]; int fd = open("fooey",0_WRONLY | O_CREAT|O_TRUNC,0777); strcpy (buffer, "First data"); write(fd, buffer, strlen(buffer)); 1seek (fd, 90, SEEK_SET); strcpy (buffer, "Second data"); write(fd, buffer, strlen(buffer)); 1seek (fd, 100, SEEK_END); strpcy (buffer, "Third data"); write(fd, buffer, strlen(buffer)); close(fd); a. What is the size of the file at the end of this section of code? b. Describe the contents of the file say exactly what byte offsets contain actual data, and what offsets constitute "holes". c. Why might holey files be useful? d. Suppose, after the above sequence of writes, the same program opens the file for reading and then does: lseek (rfd, 130, SEEK_SET) ; read (rfd, buffer, 40); What will the read return, and what (if anything) will be placed in buffer? Linux (and Unix) permit files to have "holes" in them. A "hole" can be created by seeking beyond the end of the file and writing data there. Consider the following code. Assume all system calls are successful, and BUFSIZE is sufficiently large. (Look up any unfamiliar functions using the man command on your VM.) char buffer [BUFSIZE]; int fd = open("fooey",0_WRONLY | O_CREAT|O_TRUNC,0777); strcpy (buffer, "First data"); write(fd, buffer, strlen(buffer)); 1seek (fd, 90, SEEK_SET); strcpy (buffer, "Second data"); write(fd, buffer, strlen(buffer)); 1seek (fd, 100, SEEK_END); strpcy (buffer, "Third data"); write(fd, buffer, strlen(buffer)); close(fd); a. What is the size of the file at the end of this section of code? b. Describe the contents of the file say exactly what byte offsets contain actual data, and what offsets constitute "holes". c. Why might holey files be useful? d. Suppose, after the above sequence of writes, the same program opens the file for reading and then does: lseek (rfd, 130, SEEK_SET) ; read (rfd, buffer, 40); What will the read return, and what (if anything) will be placed in buffer?
Expert Answer:

Related Book For 

Accounting Information Systems
ISBN: 9780132871938
11th Edition
Authors: George H. Bodnar, William S. Hopwood
Posted Date:
Students also viewed these programming questions
-
This exercise is comprised of four parts. Part 1 covers automated routines macros in Excel to rearrange and transform data, Part 2 covers Pivot Table: Data Sets Cross-Tabulation and Querying in Excel...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Consider the deletion of record 5 from the file as shown below compare the relative merits of the following techniques for implementing the deletion: a. Move record 6 to the space occupied by record...
-
A 15.0-kg object moving in the + x direction at 5.5m/s collides head-on with a 10.0-kg object moving in the x direction at 4.0m/s. Find the final velocity of each mass if: (a) The objects stick...
-
What pricing objective(s) is a skimming pricing policy most likely implementing? Is the same true for a penetration pricing policy? Which policy is probably most appropriate for each of the following...
-
Unless otherwise specified, which rule will always be processed?
-
Baker Mfg Inc. wishes to compare its inventory turnover to those of industry leaders, who have turnover of about 13 times per year and 8% of their assets invested in inventory. a. What is Bakers...
-
Medicare is financed through which three primary sources? Public donations, beneficiary premiums, general tax revenue General tax revenue, beneficiary premiums, payroll tax contributions Payroll tax...
-
Suppose 40% of recent college graduates plan on pursuing a graduate degree. Fifteen recent college graduates are randomly selected. a. What is the probability that no more than four of the college...
-
Make a simulation that produces registers D = 10H, B' = 45H, and C' = 75H using the OR, AND, and EXX instructions if it is known that register A = 31H, register B = 45H, and register H = 12H. 1....
-
Using the slide below as a template:Define and analyze the competitive structure for the Energy Bars category. Level of Competition Product form PDA Competition Definition Full-features Competitors...
-
James Pet Supplies Incorporated Balance Sheets Years ended 2014 and 2015 Assets Liab. Equity 2014 2015 2014 2015 Cash $1,500 $2,300 Accounts Pay $3,000 $4,000 Accounts Rec. 1,600 2,800 Inventory...
-
Engage in a discussion where you takes on a role within the project team (e.g., project manager, client representative, team member). Discuss the scenario, debate the pros and cons of introducing...
-
Describe an example where the Theory of Constraints (TOC) was successfully applied to improve a process or where you saw the potential for TOC to improve the process in either a company you worked...
-
This is a very top-down approach where the supervisor makes all the decisions and dictates tasks and procedures to the team. 2. Democratic Style: In this style, the supervisor involves the team in...
-
What are QSAR structure-function relationship quantitative studies?
-
Evenflow Power Co. is considering a new project that is a little riskier than the current operations of the company. Thus, management has decided to add an additional 1.5% to the company's overall...
-
In 2001, XY Company purchased over $ 10 million of office equipment under its special ordering system, with individual orders ranging from $ 5,000 to $ 30,000. Special orders entail low- volume items...
-
List the four types of master records that are used in SAP ERP.
-
For each of the following application files, discuss the relative merits of sequential, direct, and indexed- sequential file organization: a. Open-order file in a large manufacturing firm b. Accounts...
-
Which of the following statements is true? a. Money is a commodity as well as a medium of exchange in a conventional mode of financing. b. Money is not a commodity and is a medium of exchange and...
-
The standards-setting body of the IFRS Foundation is a. International Accounting Standards Board (IASB) b. IFRS Foundation Monitoring Board c. IFRS Interpretations Committee d. IFRS Foundation...
-
In general, financial accounting can be broken down into the following steps: a. Identifying and recording economic transactions b. Recording and communicating economic transactions c. Identifying,...

Study smarter with the SolutionInn App