NACLS Submit Configure NACLs to control the access to the VMs according to the following: Allow...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
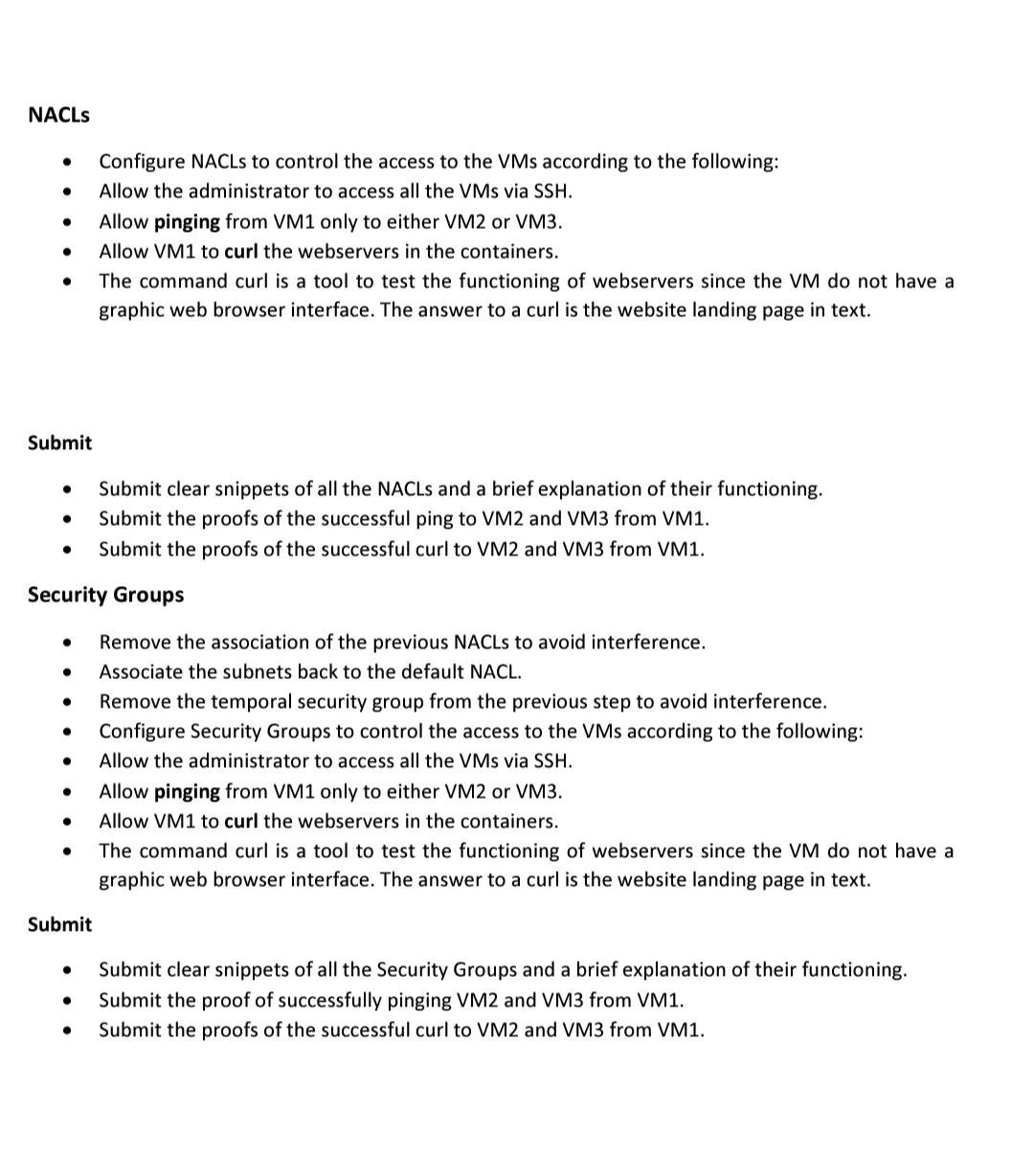
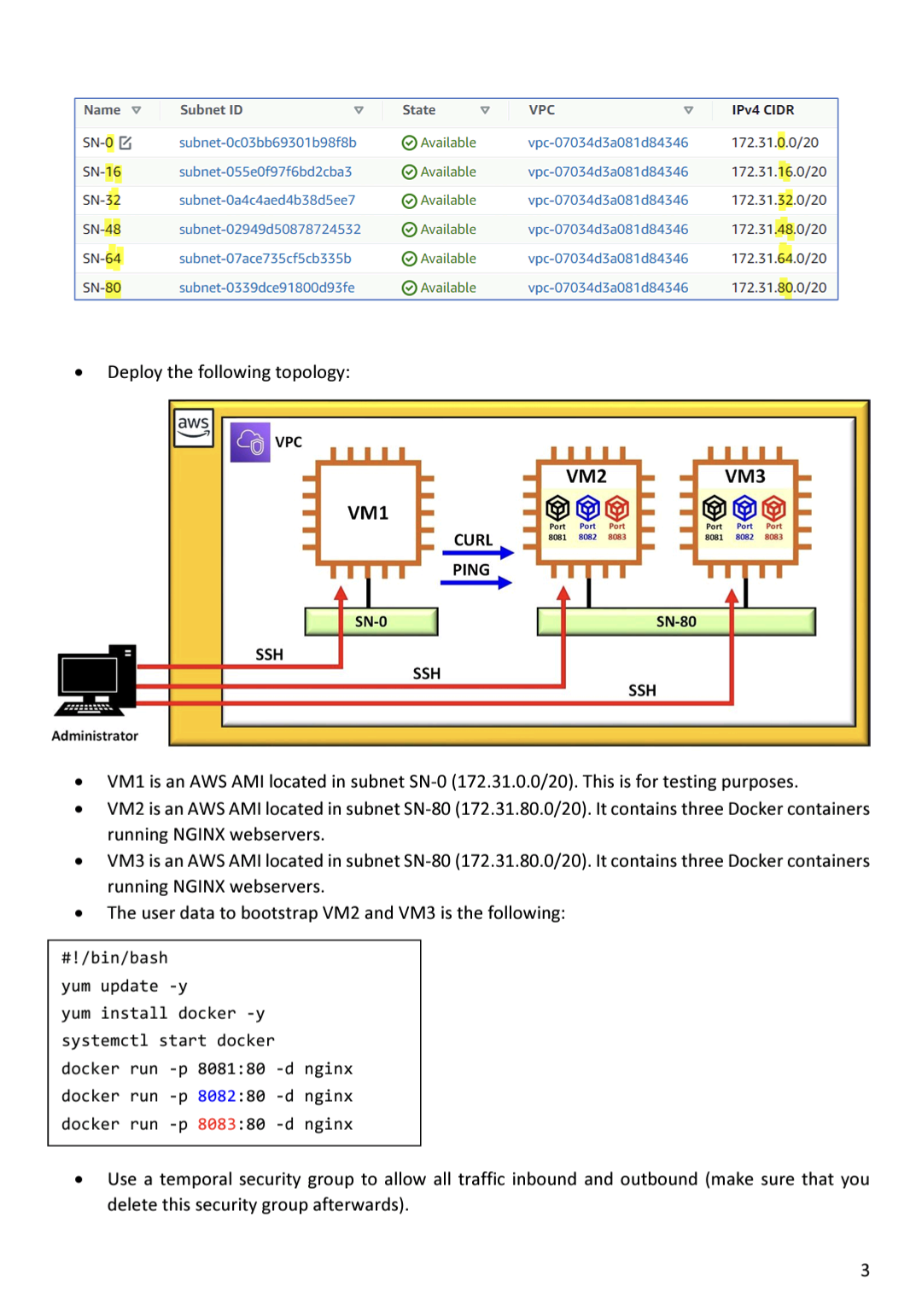
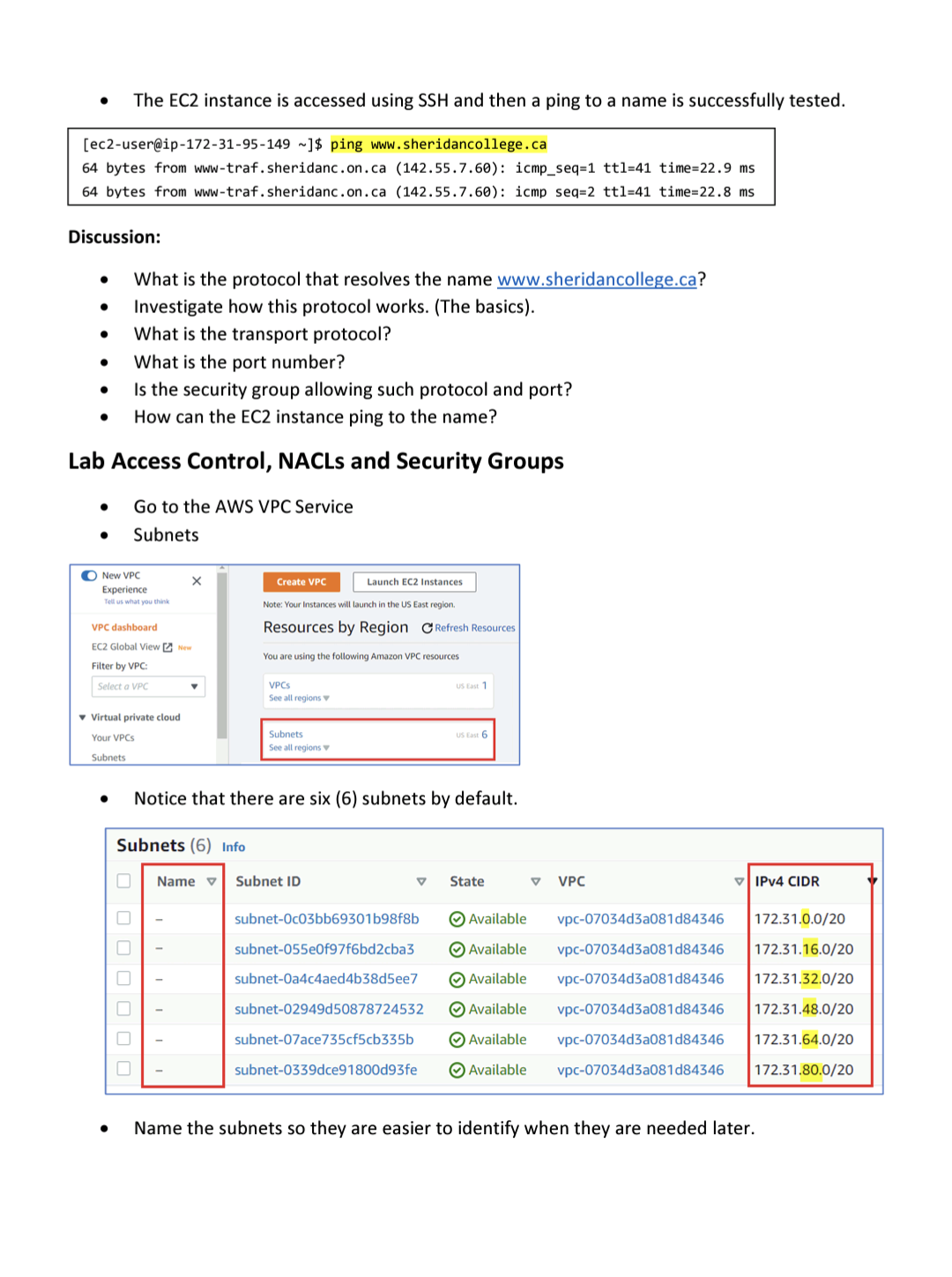
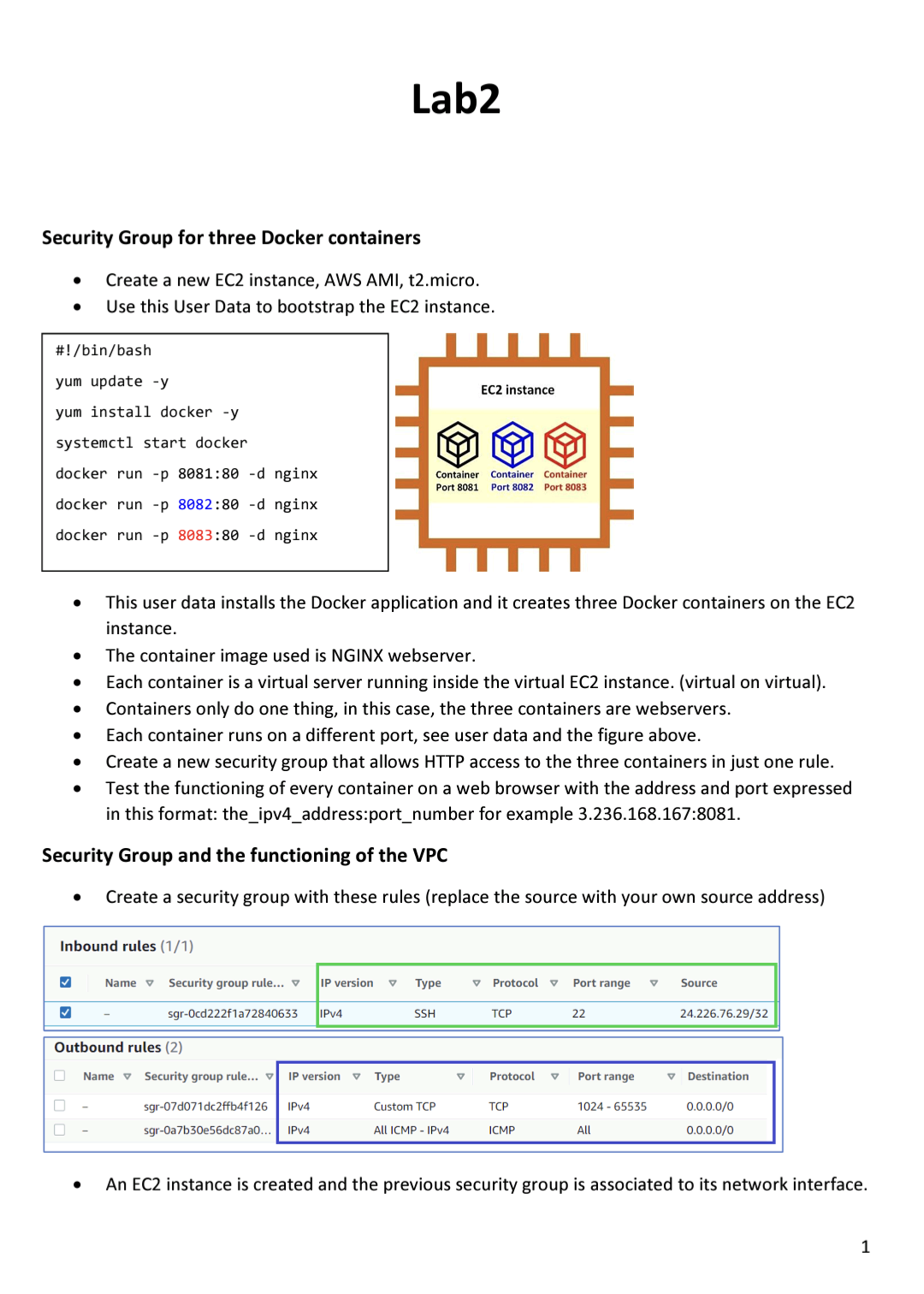
NACLS Submit Configure NACLs to control the access to the VMs according to the following: Allow the administrator to access all the VMs via SSH. Submit Allow pinging from VM1 only to either VM2 or VM3. Allow VM1 to curl the webservers in the containers. Security Groups The command curl is a tool to test the functioning of webservers since the VM do not have a graphic web browser interface. The answer to a curl is the website landing page in text. Submit clear snippets of all the NACLS and a brief explanation of their functioning. Submit the proofs of the successful ping to VM2 and VM3 from VM1. Submit the proofs of the successful curl to VM2 and VM3 from VM1. Remove the association of the previous NACLs to avoid interference. Associate the subnets back to the default NACL. Remove the temporal security group from the previous step to avoid interference. Configure Security Groups to control the access to the VMs according to the following: Allow the administrator to access all the VMs via SSH. Allow pinging from VM1 only to either VM2 or VM3. Allow VM1 to curl the webservers in the containers. The command curl is a tool to test the functioning of webservers since the VM do not have a graphic web browser interface. The answer to a curl is the website landing page in text. Submit clear snippets of all the Security Groups and a brief explanation of their functioning. Submit the proof of successfully pinging VM2 and VM3 from VM1. Submit the proofs of the successful curl to VM2 and VM3 from VM1. Name v SN-0 SN-16 SN-32 SN-48 SN-64 SN-80 Administrator Deploy the following topology: Subnet ID subnet-Oc03bb69301b98f8b subnet-055e0f97f6bd2cba3 subnet-0a4c4aed4b38d5ee7 subnet-02949d50878724532 subnet-07ace735cf5cb335b subnet-0339dce91800d93fe aws VPC SSH VM1 SN-0 #!/bin/bash yum update -y yum install docker -y systemctl start docker docker run -p 8081:80 -d nginx docker run-p 8082:80 -d nginx docker run -p 8083:80 -d nginx State Available Available Available Available Available Available SSH V CURL PING VPC vpc-07034d3a081d84346 vpc-07034d3a081d84346 vpc-07034d3a081d84346 vpc-07034d3a081d84346 vpc-07034d3a081d84346 vpc-07034d3a081d84346 VM2 1998 Port Port Port 8081 8082 8083 V SSH SN-80 IPv4 CIDR 172.31.0.0/20 172.31.16.0/20 172.31.32.0/20 172.31.48.0/20 172.31.64.0/20 172.31.80.0/20 VM3 Port Port Port 8081 8082 8083 VM1 is an AWS AMI located in subnet SN-0 (172.31.0.0/20). This is for testing purposes. VM2 is an AWS AMI located in subnet SN-80 (172.31.80.0/20). It contains three Docker containers running NGINX webservers. VM3 is an AWS AMI located in subnet SN-80 (172.31.80.0/20). It contains three Docker containers running NGINX webservers. The user data to bootstrap VM2 and VM3 is the following: Use a temporal security group to allow all traffic inbound and outbound (make sure that you delete this security group afterwards). 3 The EC2 instance is accessed using SSH and then a ping to a name is successfully tested. [ec2-user@ip-172-31-95-149 ~]$ ping www.sheridancollege.ca 64 bytes from www-traf.sheridanc.on.ca (142.55.7.60): icmp_seq=1 ttl-41 time=22.9 ms 64 bytes from www-traf.sheridanc.on.ca (142.55.7.60): icmp seq=2 ttl=41 time=22.8 ms Discussion: What is the protocol that resolves the name www.sheridancollege.ca? Investigate how this protocol works. (The basics). What is the transport protocol? What is the port number? Is the security group allowing such protocol and port? How can the EC2 instance ping to the name? Lab Access Control, NACLs and Security Groups Go to the AWS VPC Service Subnets New VPC Experience Tell us what you think VPC dashboard EC2 Global ViewNew Filter by VPC: Select a VPC Virtual private cloud Your VPCS Subnets X 0000000 Create VPC Launch EC2 Instances. Note: Your Instances will launch in the US East region. Resources by Region Refresh Resources You are using the following Amazon VPC resources Name VPCs See all regions Subnets See all regions Notice that there are six (6) subnets by default. Subnets (6) Info Subnet ID US East 1 US East 6 subnet-Oc03bb69301b98f8b subnet-055e0f97f6bd2cba3 subnet-0a4c4aed4b38d5ee7 subnet-02949d50878724532 subnet-07ace735cf5cb335b subnet-0339dce91800d93fe V State V VPC IPv4 CIDR Available vpc-07034d3a081d84346 172.31.0.0/20 Available vpc-07034d3a081d84346 172.31.16.0/20 Available vpc-07034d3a081d84346 172.31.32.0/20 Available vpc-07034d3a081d84346 172.31.48.0/20 Available vpc-07034d3a081d84346 172.31.64.0/20 Available vpc-07034d3a081d84346 172.31.80.0/20 Name the subnets so they are easier to identify when they are needed later. Security Group for three Docker containers #!/bin/bash yum update -y yum install docker -y systemctl start docker docker run -p 8081:80 -d nginx docker run -p 8082:80 -d nginx docker run -p 8083:80 -d nginx 0 Create a new EC2 instance, AWS AMI, t2.micro. Use this User Data to bootstrap the EC2 instance. Inbound rules (1/1) Lab2 Create a new security group that allows HTTP access to the three containers in just one rule. Test the functioning of every container on a web browser with the address and port expressed in this format: the_ipv4_address:port_number for example 3.236.168.167:8081. Security Group and the functioning of the VPC Create a security group with these rules (replace the source with your own source address) This user data installs the Docker application and it creates three Docker containers on the EC2 instance. Outbound rules (2) Name The container image used is NGINX webserver. Each container is a virtual server running inside the virtual EC2 instance. (virtual on virtual). Containers only do one thing, in this case, the three containers are webservers. Each container runs on a different port, see user data and the figure above. Container Container Container Port 8081 Port 8082 Port 8083 Security group rule... V IP version V Type sgr-07d071dc2ffb4f126 IPv4 sgr-0a7b30e56dc87a0... IPv4 EC2 instance Name v Security group rule... v IP version V Type V Protocol sgr-Ocd222f1a72840633 IPv4 SSH Custom TCP All ICMP IPv4 V TCP Protocol TCP ICMP V Port range 22 Port range 1024-65535 All V Source 24.226.76.29/32 V Destination 0.0.0.0/0 0.0.0.0/0 An EC2 instance is created and the previous security group is associated to its network interface. 1 NACLS Submit Configure NACLs to control the access to the VMs according to the following: Allow the administrator to access all the VMs via SSH. Submit Allow pinging from VM1 only to either VM2 or VM3. Allow VM1 to curl the webservers in the containers. Security Groups The command curl is a tool to test the functioning of webservers since the VM do not have a graphic web browser interface. The answer to a curl is the website landing page in text. Submit clear snippets of all the NACLS and a brief explanation of their functioning. Submit the proofs of the successful ping to VM2 and VM3 from VM1. Submit the proofs of the successful curl to VM2 and VM3 from VM1. Remove the association of the previous NACLs to avoid interference. Associate the subnets back to the default NACL. Remove the temporal security group from the previous step to avoid interference. Configure Security Groups to control the access to the VMs according to the following: Allow the administrator to access all the VMs via SSH. Allow pinging from VM1 only to either VM2 or VM3. Allow VM1 to curl the webservers in the containers. The command curl is a tool to test the functioning of webservers since the VM do not have a graphic web browser interface. The answer to a curl is the website landing page in text. Submit clear snippets of all the Security Groups and a brief explanation of their functioning. Submit the proof of successfully pinging VM2 and VM3 from VM1. Submit the proofs of the successful curl to VM2 and VM3 from VM1. Name v SN-0 SN-16 SN-32 SN-48 SN-64 SN-80 Administrator Deploy the following topology: Subnet ID subnet-Oc03bb69301b98f8b subnet-055e0f97f6bd2cba3 subnet-0a4c4aed4b38d5ee7 subnet-02949d50878724532 subnet-07ace735cf5cb335b subnet-0339dce91800d93fe aws VPC SSH VM1 SN-0 #!/bin/bash yum update -y yum install docker -y systemctl start docker docker run -p 8081:80 -d nginx docker run-p 8082:80 -d nginx docker run -p 8083:80 -d nginx State Available Available Available Available Available Available SSH V CURL PING VPC vpc-07034d3a081d84346 vpc-07034d3a081d84346 vpc-07034d3a081d84346 vpc-07034d3a081d84346 vpc-07034d3a081d84346 vpc-07034d3a081d84346 VM2 1998 Port Port Port 8081 8082 8083 V SSH SN-80 IPv4 CIDR 172.31.0.0/20 172.31.16.0/20 172.31.32.0/20 172.31.48.0/20 172.31.64.0/20 172.31.80.0/20 VM3 Port Port Port 8081 8082 8083 VM1 is an AWS AMI located in subnet SN-0 (172.31.0.0/20). This is for testing purposes. VM2 is an AWS AMI located in subnet SN-80 (172.31.80.0/20). It contains three Docker containers running NGINX webservers. VM3 is an AWS AMI located in subnet SN-80 (172.31.80.0/20). It contains three Docker containers running NGINX webservers. The user data to bootstrap VM2 and VM3 is the following: Use a temporal security group to allow all traffic inbound and outbound (make sure that you delete this security group afterwards). 3 The EC2 instance is accessed using SSH and then a ping to a name is successfully tested. [ec2-user@ip-172-31-95-149 ~]$ ping www.sheridancollege.ca 64 bytes from www-traf.sheridanc.on.ca (142.55.7.60): icmp_seq=1 ttl-41 time=22.9 ms 64 bytes from www-traf.sheridanc.on.ca (142.55.7.60): icmp seq=2 ttl=41 time=22.8 ms Discussion: What is the protocol that resolves the name www.sheridancollege.ca? Investigate how this protocol works. (The basics). What is the transport protocol? What is the port number? Is the security group allowing such protocol and port? How can the EC2 instance ping to the name? Lab Access Control, NACLs and Security Groups Go to the AWS VPC Service Subnets New VPC Experience Tell us what you think VPC dashboard EC2 Global ViewNew Filter by VPC: Select a VPC Virtual private cloud Your VPCS Subnets X 0000000 Create VPC Launch EC2 Instances. Note: Your Instances will launch in the US East region. Resources by Region Refresh Resources You are using the following Amazon VPC resources Name VPCs See all regions Subnets See all regions Notice that there are six (6) subnets by default. Subnets (6) Info Subnet ID US East 1 US East 6 subnet-Oc03bb69301b98f8b subnet-055e0f97f6bd2cba3 subnet-0a4c4aed4b38d5ee7 subnet-02949d50878724532 subnet-07ace735cf5cb335b subnet-0339dce91800d93fe V State V VPC IPv4 CIDR Available vpc-07034d3a081d84346 172.31.0.0/20 Available vpc-07034d3a081d84346 172.31.16.0/20 Available vpc-07034d3a081d84346 172.31.32.0/20 Available vpc-07034d3a081d84346 172.31.48.0/20 Available vpc-07034d3a081d84346 172.31.64.0/20 Available vpc-07034d3a081d84346 172.31.80.0/20 Name the subnets so they are easier to identify when they are needed later. Security Group for three Docker containers #!/bin/bash yum update -y yum install docker -y systemctl start docker docker run -p 8081:80 -d nginx docker run -p 8082:80 -d nginx docker run -p 8083:80 -d nginx 0 Create a new EC2 instance, AWS AMI, t2.micro. Use this User Data to bootstrap the EC2 instance. Inbound rules (1/1) Lab2 Create a new security group that allows HTTP access to the three containers in just one rule. Test the functioning of every container on a web browser with the address and port expressed in this format: the_ipv4_address:port_number for example 3.236.168.167:8081. Security Group and the functioning of the VPC Create a security group with these rules (replace the source with your own source address) This user data installs the Docker application and it creates three Docker containers on the EC2 instance. Outbound rules (2) Name The container image used is NGINX webserver. Each container is a virtual server running inside the virtual EC2 instance. (virtual on virtual). Containers only do one thing, in this case, the three containers are webservers. Each container runs on a different port, see user data and the figure above. Container Container Container Port 8081 Port 8082 Port 8083 Security group rule... V IP version V Type sgr-07d071dc2ffb4f126 IPv4 sgr-0a7b30e56dc87a0... IPv4 EC2 instance Name v Security group rule... v IP version V Type V Protocol sgr-Ocd222f1a72840633 IPv4 SSH Custom TCP All ICMP IPv4 V TCP Protocol TCP ICMP V Port range 22 Port range 1024-65535 All V Source 24.226.76.29/32 V Destination 0.0.0.0/0 0.0.0.0/0 An EC2 instance is created and the previous security group is associated to its network interface. 1
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these programming questions
-
a) On the basis of a one-factor model, assume that the risk-free rate is 6% and the expected return on a portfolio with unit sensitivity to the factor is 8.5%. Consider a portfolio of two securities...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Using Exhibit 12-1, determine the life expectancy of a 40-year old male.
-
Determine the normal force, shear force, and moment at a section passing through point C. Units Used: kN = 103 N Given: P = 8 kN c = 0.75 m a = 0.75m d = 0.5 m b = 0.75m r = 0.1 m - d+r -A, A, b+c
-
Gold Sense, which uses time-driven activity-based costing, estimates that one minute of time uses $1.35 in resources, and it has developed the following time estimates for its activities: Activity...
-
The table below shows the condition indices and variance decomposition proportions for the acetylene data using centered regressors. Use this information to diagnose multicollinearity in the data and...
-
You own an oil pipeline which will generate a $2 million cash return over the coming year. The pipelines operating costs are negligible, and it is expected to last for a very long time....
-
Your beginning salary is $68,000. You deposit 8% each year in a savings account that earns 3% interest. Your salary increases by 5% per year and inflation is 2.5% per year. What value does your...
-
On January 1, Year 2, the following information was drawn from the accounting records of Carter Company: cash of $800; land of $3,500; notes payable of $600; and common stock of $1,000. Required a....
-
While each community in the State Road 7 Collaborative maintains its identity and independence, Dahlstrom believes that the leverage of multi-governmental applications will ultimately secure more...
-
Compute the Fourier transform of each of the sequences in Exercise 2.1. Exercise 2.1. Compute the \(z\) transform of the following sequences, indicating their regions of convergence: (a) \(x(n)=\sin...
-
Based on Azarovs statement concerning ERISA and ASC 715, which of the following statements is correct? A. Maglav is not allowed to terminate the plan. B. Maglav can exclude the plans service costs...
-
Write a MATLAB program to plot the solution to the three difference equations in Exercise 1.18 for \(\omega=\pi / 3\) and \(\omega=\pi\). Exercise 1.18 Determine the steady-state response for the...
-
If the signal \(x(n)=4 \cos [(\pi / 4) n-(\pi / 6)] u(n)\) is input to the linear system of Exercise 2.6e, determine its steady-state response. Exercise 2.6e, (e) \(\frac{1-z^{2}}{\left(2 z^{2}-1...
-
Solve Exercise 1.22 using the concept of the transfer function. Exercise 1.22 Compute the inverse Fourier transform of \[X\left(\mathrm{e}^{\mathrm{j} \omega} ight)=\frac{1}{1-\mathrm{e}^{-\mathrm{j}...
-
Problem 1. (Matlab assignment) Use Matlab to perform the following operations and explain the results you obtain (no need to turn in matlab codes). Note that eps represents the rounding unit in...
-
A company produces earbuds. The revenue from the sale of x units of these earbuds is R = 8x. The cost to produce x units of earbuds is C = 3x + 1500. In what interval will the company at least break...
-
Describe three differences between REA diagrams and ER diagrams.
-
Classify the following users of information as either I internal user T --external user, trading partner S--external user stakeholder a. Internal Revenue Service b. Inventory control manager c....
-
Describe a distributed denial of service (DDos) attack.
-
Verify that the log-likelihood of model (7.7) is \(\sum_{i=1}^{k}\left[n_{i} \lambda-\exp (\lambda) ight]\). (a) Compute MLE of \(\lambda\). (b) Compute the Pearson chi-square statistic and compare...
-
Think about the general concept of a relationship, not necessarily in a business setting, but just relationships in general between any two parties. What aspects of relationships are inherently...
-
What is value? In what ways does a relationship selling approach add value to your customers, to you the salesperson, and to your sales organization?

Study smarter with the SolutionInn App


