P5. (10 pts) Consider a slotted ALOHA system. Suppose there are 2N nodes sharing the channel....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
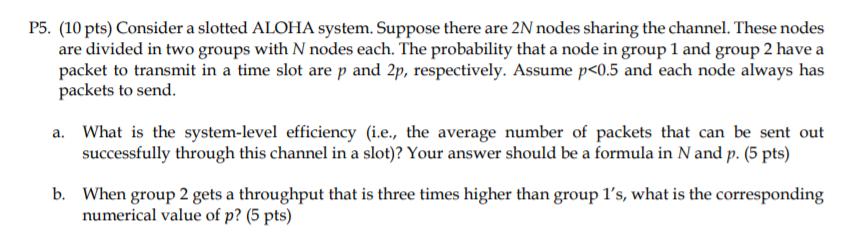
P5. (10 pts) Consider a slotted ALOHA system. Suppose there are 2N nodes sharing the channel. These nodes are divided in two groups with N nodes each. The probability that a node in group 1 and group 2 have a packet to transmit in a time slot are p and 2p, respectively. Assume p <0.5 and each node always has packets to send. a. What is the system-level efficiency (i.e., the average number of packets that can be sent out successfully through this channel in a slot)? Your answer should be a formula in N and p. (5 pts) b. When group 2 gets a throughput that is three times higher than group 1's, what is the corresponding numerical value of p? (5 pts) P5. (10 pts) Consider a slotted ALOHA system. Suppose there are 2N nodes sharing the channel. These nodes are divided in two groups with N nodes each. The probability that a node in group 1 and group 2 have a packet to transmit in a time slot are p and 2p, respectively. Assume p <0.5 and each node always has packets to send. a. What is the system-level efficiency (i.e., the average number of packets that can be sent out successfully through this channel in a slot)? Your answer should be a formula in N and p. (5 pts) b. When group 2 gets a throughput that is three times higher than group 1's, what is the corresponding numerical value of p? (5 pts)
Expert Answer:
Answer rating: 100% (QA)
a To calculate the systemlevel efficiency in a slotted ALOHA system with 2N nodes where N nodes are in each of the two groups we can use the following ... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these programming questions
-
What is multi-factor authentication? What specific products are used in multi-factor authentication? What are the strengths of these products? Do they always work as intended? If not, why not, and...
-
"internet radios" for streaming audio, and personal video recorders and players. Describe design and evaluation processes that could be used by a start-up company to improve the usability of such...
-
The figure shows the result of taking 25 SRSs from a Normal population and constructing a confidence interval for the population mean using each sample. Which confidence level 80%, 90%, 95%, or 99%do...
-
When may a company report gains or losses on fair value adjustments through other comprehensive income? Why might a company choose to report these gains and losses in other comprehensive income?
-
The diagrams shown here contain one or more of the compounds: H2A, NaHA, and Na2A, where H2A is a weak diprotic acid.
-
In 2001, the City of New York and the Dormitory Authority of the State of New York (DASNY) entered into an agreement to build a forensic biology laboratory in Manhattan. Per the agreement, DASNY...
-
The following events apply to Equipment Services Inc. in its first year of operation: 1. Acquired $60,000 cash from the issue of common stock. 2. Received a $8,200 cash advance for services to be...
-
Question 17 (1 point) If the credit to record the payment of an account payable is not posted Liabilities will be understated Expenses will be understated Cash will be overstated Which statement is...
-
Acme Oatmeal cereal contains 3 grams of fibre per standard serving size. Which of these nutrient content claims would be most appropriate for use on this product? Question 4 options: Source of fibre...
-
Discuss accounting for seismic costs. Be sure to include in your answer an explanation of the situations in which companies may opt to capitalize seismic costs and whether or not this practice is in...
-
Which of the following questions are relevant when identifying actors? (i) Where in the organization is the system used? (ii) Which hardware devices will interact with the system? (iii) How will the...
-
Which system contributes information on direct labor to a cost accounting system? a. Supply chain management system (SCMS) b. Financial reporting system (FRS) c. Customer Relational Management System...
-
Which of the following describes the purpose of an intermediate timer event? a. Indicates receipt of a message b. Indicates branching c. Indicates delay d. Both (a) and (c) e. Both (b) and (c)
-
Which of the following is not an activity in the conversion process? a. Authorize production b. Issue raw material c. Perform work d. Transfer finished goods to customers e. All of these are...
-
Phoenix Inc. purchased 75% of the voting shares of Sky Inc. for $525,000 on December 31, 2017. On that date, Sky Inc.'s Common Stock and Retained Earnings had book values of $200,000 and $100,000,...
-
A condenser (heat exchanger) brings 1 kg/s water flow at 10 kPa quality 95% to saturated liquid at 10 kPa, as shown in Fig. P4.91. The cooling is done by lake water at 20C that returns to the lake at...
-
Consider the switch shown below. Suppose that all datagrams have the same fixed length, that the switch operates in a slotted, synchronous manner, and that in one time slot a datagram can be...
-
Consider that only a single TCP (Reno) connection uses one 10Mbps link which does not buffer any data. Suppose that this link is the only congested link between the sending and receiving hosts....
-
In Section 4.2.2 an example forwarding table (using longest prefix matching) is given. Rewrite this forwarding table using the a.b.c.d/x notation instead of the binary string notation.
-
Identify the most promising areas of research for future researchers in the area of hedge fund systemic risk.
-
Discuss how hedge funds and the potential for shadow banking may contribute to systemic risk and the prospect for contagion.
-
Explain the relation between hedge fund characteristics and risks.

Study smarter with the SolutionInn App


