Please read the question carefully and explain your work clearly Computer A sends 200bit data packets...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
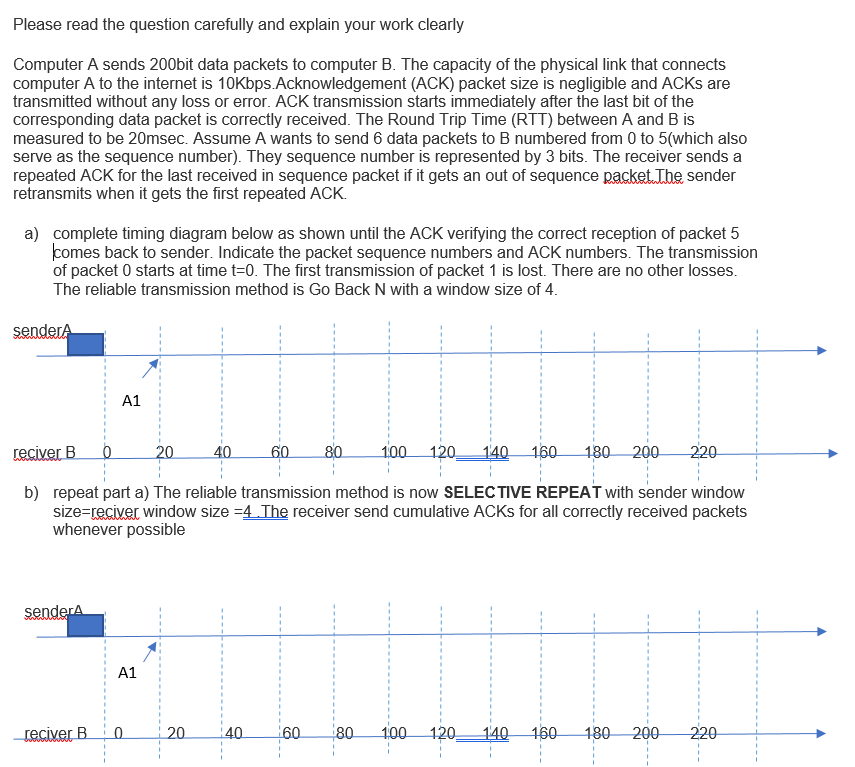
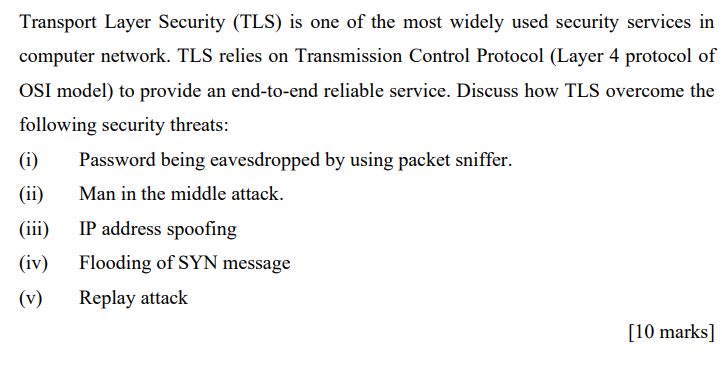
Please read the question carefully and explain your work clearly Computer A sends 200bit data packets to computer B. The capacity of the physical link that connects computer A to the internet is 10Kbps.Acknowledgement (ACK) packet size is negligible and ACKs are transmitted without any loss or error. ACK transmission starts immediately after the last bit of the corresponding data packet is correctly received. The Round Trip Time (RTT) between A and B is measured to be 20msec. Assume A wants to send 6 data packets to B numbered from 0 to 5(which also serve as the sequence number). They sequence number is represented by 3 bits. The receiver sends a repeated ACK for the last received in sequence packet if it gets an out of sequence packet. The sender retransmits when it gets the first repeated ACK. a) complete timing diagram below as shown until the ACK verifying the correct reception of packet 5 comes back to sender. Indicate the packet sequence numbers and ACK numbers. The transmission of packet 0 starts at time t=0. The first transmission of packet 1 is lost. There are no other losses. The reliable transmission method is Go Back N with a window size of 4. senderA reciver B 1:00 120 140 160 180 200 220 b) repeat part a) The reliable transmission method is now SELECTIVE REPEAT with sender window size=reciver window size =4. The receiver send cumulative ACKS for all correctly received packets whenever possible senderA A1 reciver B A1 0 20 20 40 40 60 60 80 1:00 120. 140 160 180 200 220 1 Transport Layer Security (TLS) is one of the most widely used security services in computer network. TLS relies on Transmission Control Protocol (Layer 4 protocol of OSI model) to provide an end-to-end reliable service. Discuss how TLS overcome the following security threats: (i) (ii) (iii) (iv) (v) Password being eavesdropped by using packet sniffer. Man in the middle attack. IP address spoofing Flooding of SYN message Replay attack [10 marks] Please read the question carefully and explain your work clearly Computer A sends 200bit data packets to computer B. The capacity of the physical link that connects computer A to the internet is 10Kbps.Acknowledgement (ACK) packet size is negligible and ACKs are transmitted without any loss or error. ACK transmission starts immediately after the last bit of the corresponding data packet is correctly received. The Round Trip Time (RTT) between A and B is measured to be 20msec. Assume A wants to send 6 data packets to B numbered from 0 to 5(which also serve as the sequence number). They sequence number is represented by 3 bits. The receiver sends a repeated ACK for the last received in sequence packet if it gets an out of sequence packet. The sender retransmits when it gets the first repeated ACK. a) complete timing diagram below as shown until the ACK verifying the correct reception of packet 5 comes back to sender. Indicate the packet sequence numbers and ACK numbers. The transmission of packet 0 starts at time t=0. The first transmission of packet 1 is lost. There are no other losses. The reliable transmission method is Go Back N with a window size of 4. senderA reciver B 1:00 120 140 160 180 200 220 b) repeat part a) The reliable transmission method is now SELECTIVE REPEAT with sender window size=reciver window size =4. The receiver send cumulative ACKS for all correctly received packets whenever possible senderA A1 reciver B A1 0 20 20 40 40 60 60 80 1:00 120. 140 160 180 200 220 1 Transport Layer Security (TLS) is one of the most widely used security services in computer network. TLS relies on Transmission Control Protocol (Layer 4 protocol of OSI model) to provide an end-to-end reliable service. Discuss how TLS overcome the following security threats: (i) (ii) (iii) (iv) (v) Password being eavesdropped by using packet sniffer. Man in the middle attack. IP address spoofing Flooding of SYN message Replay attack [10 marks]
Expert Answer:

Related Book For 

Accounting Information Systems
ISBN: 978-1133935940
10th edition
Authors: Ulric J. Gelinas, Richard B. Dull
Posted Date:
Students also viewed these computer network questions
-
Q1. You have identified a market opportunity for home media players that would cater for older members of the population. Many older people have difficulty in understanding the operating principles...
-
CANMNMM January of this year. (a) Each item will be held in a record. Describe all the data structures that must refer to these records to implement the required functionality. Describe all the...
-
Factor each polynomial. 125k - 64k 4
-
ICA Corporation is reviewing an investment proposal. The schedule below presents the initial cost and estimates of the investment's book value at the end of each year, the net cash flows for each...
-
Describe a commonly used format for writing marketing research reports.
-
Why is the concept of DevOps appealing to organizations?
-
Harrys Carryout Stores has eight locations. The firm wishes to expand by two more stores and needs a bank loan to do this. Mr. Wilson, the banker, will finance construction if the firm can present an...
-
1a. Determine this wave's amplitude. 1b. Determine this wave's wavelength. 1c. Determine this wave's frequency. 1d. Determine this wave's speed of propagation. 1e.Determine this wave's direction of...
-
At January 1, 2024, M. E. Gainor Corporation had outstanding the following securities: The following additional information is available: On September 1, 2024, M. E. Gainor sold 72 million...
-
Which one best indicates Carla's residency status for Canadian income tax purposes for 2018? Carla lives in Detroit, Michigan, USA. She commutes daily to Windsor, Ontario, Canada, where she is...
-
What are five negative actions that prevent a team from achieving its goals?
-
What are the criteria for evaluating sources using the CRAAP test? What does each criterion look for?
-
What are the steps for stopping the spread of fabricated or misleading information?
-
What is the difference between citation and documentation?
-
What is the difference among quotation, paraphrase, and summary?
-
For a system, RAM = 64KB, Block size = 4 bytes, Cache size = 128 bytes, 2-way Set Associative cache. CPU requires to access following memory locations while running a program "Test Cache". 3, 5, 10,...
-
Representative data read from a plot that appeared in the paper Effect of Cattle Treading on Erosion from Hill Pasture: Modeling Concepts and Analysis of Rainfall Simulator Data (Australian Journal...
-
a. Discuss the conditions under which each of the following billing processes are most appropriate: (1) pre-billing system, and (2) post-billing system. b. Discuss the relative advantages of each of...
-
Compare and contrast the efficiency and effectiveness of an in-house data center, an arrangement with an outsourcing vendor to own and operate a data center for you, a service bureau, an applications...
-
Historically, many businesses served only local customers. That model usually limited customers to a small geographic area. Identify a specific type of business, and compare/ contrast the...
-
Fill in the blank: If two variables have a positive association, then large values of one variable are associated with __________________ values of the other.
-
Percentiles are values that divide a data set into hundredths. The values that divide a data set into tenths are called deciles, denoted D1,D2, ...,D9. Describe the relationship between percentiles...
-
For each of the following pairs of variables, determine whether the association is positive or negative, and explain why. a. Would the association between outdoor temperature and consumption of...

Study smarter with the SolutionInn App