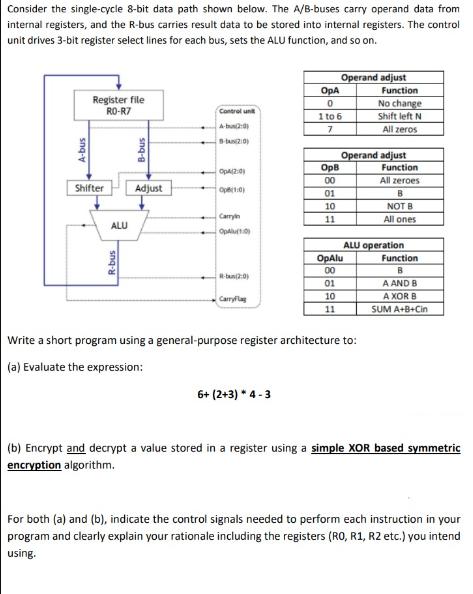
Consider the single-cycle 8-bit data path shown below. The A/B-buses carry operand data from internal registers,...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Consider the single-cycle 8-bit data path shown below. The A/B-buses carry operand data from internal registers, and the R-bus carries result data to be stored into internal registers. The control unit drives 3-bit register select lines for each bus, sets the ALU function, and so on. A-bus Register file RO-R7 Shifter ALU R-bus snq-g Adjust Control unit A-b (20) Op4(2:0) Op(1:0) Carryin OpAlu(10) R-ban(2:0) CarryFlag OpA 0 6+ (2+3) * 4-3 1 to 6 7 OpB 00 01 10 11 Operand adjust 01 10 11 OpAlu 00 Function Operand adjust Write a short program using a general-purpose register architecture to: (a) Evaluate the expression: No change Shift left N All zeros Function All zeroes B NOT B All ones ALU operation Function B A AND B A XOR B SUM A+B+Cin (b) Encrypt and decrypt a value stored in a register using a simple XOR based symmetric encryption algorithm. For both (a) and (b), indicate the control signals needed to perform each instruction in your program and clearly explain your rationale including the registers (RO, R1, R2 etc.) you intend using. Consider the single-cycle 8-bit data path shown below. The A/B-buses carry operand data from internal registers, and the R-bus carries result data to be stored into internal registers. The control unit drives 3-bit register select lines for each bus, sets the ALU function, and so on. A-bus Register file RO-R7 Shifter ALU R-bus snq-g Adjust Control unit A-b (20) Op4(2:0) Op(1:0) Carryin OpAlu(10) R-ban(2:0) CarryFlag OpA 0 6+ (2+3) * 4-3 1 to 6 7 OpB 00 01 10 11 Operand adjust 01 10 11 OpAlu 00 Function Operand adjust Write a short program using a general-purpose register architecture to: (a) Evaluate the expression: No change Shift left N All zeros Function All zeroes B NOT B All ones ALU operation Function B A AND B A XOR B SUM A+B+Cin (b) Encrypt and decrypt a value stored in a register using a simple XOR based symmetric encryption algorithm. For both (a) and (b), indicate the control signals needed to perform each instruction in your program and clearly explain your rationale including the registers (RO, R1, R2 etc.) you intend using.
Expert Answer:
Related Book For 

Computer Architecture Fundamentals And Principles Of Computer Design
ISBN: 9781032097336
2nd Edition
Authors: Joseph D. Dumas II
Posted Date:
Students also viewed these programming questions
-
You need to mark real-time media traffic in Teams meetings so that network administrators can prioritize these packets on the network. What should you do? Select only one answer. From Live events...
-
Repeat question 20 using the vertical control word depicted in Figure 3.42. Question 20 Given the horizontal control word depicted in Figure 3.41 for our simple example machine, develop the micro...
-
Given the horizontal control word depicted in Figure 3.41 for our simple example machine, develop the micro routines required to fetch and execute the ANDM instruction using the steps you outlined in...
-
Use a calculator to approximate the value. Round your answer to two decimal places. arccos(0.051)
-
When Yuji died in March 2014, his gross estate was valued at $8 million. He owed debts totaling $300,000. Funeral and administration expenses were $12,000 and $120,000, respectively. The marginal...
-
Company A has a growth rate of 3% and just paid a dividend of $1.50 per share. What is the cost of equity if the current share price is $10?
-
Krasnoy Tire, a maker of tires for cars, trucks, and tractors, is trying to determine how to account for various factory costs. The costs include the following: a. Wages earned by a factory...
-
Carpetland salespersons average $8,000 per week in sales. Steve Contois, the firms vice president, proposes a compensation plan with new selling incentives. Steve hopes that the results of a trial...
-
Please review the It's Your Gavel Case beginning on page 41 (Pozgar, 2019). After reviewing the case please discuss the following: What was the specific legal issue under consideration? What did the...
-
The water table at a site is at 5 m below the ground level, and it is required to excavate to this level. The soil profile consists of a thick bed of sand where the unit weight is 17.0 kN/m 3 above...
-
Please answer question at the bottom: S-P-O Model of Healthcare Quality The S-P-O model of healthcare quality offers a framework for comprehending and assessing healthcare quality. As Ayanian and...
-
Name the seven diatomic elements in order ofincreasing Z. hydrogen, nitrogen, fluorine, oxygen, iodine,chlorine, bromine Identify the name for each polyatomic ionshown. CO 3 2- , ClO 4 - , PO 4 3- ,...
-
1. Management and leadership are two distinctive but complementary systems of action. Elaborate on the key differences between management and leadership Question 2 (15 Marks) The plans, which are...
-
Write a chemical equationfor H2SO4( a q ) showing how it is an acidor a base according to the Arrhenius definition. Write a chemical equationfor HBr( a q ) showing how it is an acidor a base...
-
What comparable firms do you recommend as the appropriate benchmarks forevaluating the risk of Ameritrade's planned advertising and technology investments?Fully elaborate your answer.
-
An AM station broadcasts rock music at 8.10 x 102 on your radio dial. Units for AM frequencies are given in kilohertz (kHz). Find the wavelength of the station's radio waves in meters (m), nanometers...
-
Calculate the energy of transition from n = 3 to n = 1. In what region of electromagnetic spectrum is this radiation found?
-
As you rewrite these sentences, replace the cliches and buzzwords with plain language (if you don't recognize any of these terms, you can find definitions online): a. Being a jack-of-all-trades, Dave...
-
What is the most significant difference between computers of the past 10 to 15 years versus those of previous generations?
-
Given the need for user programs to access operating system services, why are traps a better solution than conventional subprogram call instructions?
-
A simple RISC CPU is implemented with a single scalar instruction processing pipeline. Instructions are always executed sequentially except in the case of branch instructions. Given that p b is the...
-
Show that if there is a non-basic variable all of whose coefficients are non-negative at some stage of execution, then the problem is unbounded, as the message described above claims.
-
Show inductively that at each pass through the loop, the next system represents a basic feasible solution. Show in addition that if there are no degeneracies, the value of the objective increases...
-
Prove that if no degeneracies are encountered at any stage, then the algorithm terminates in finitely many steps with with an unboundedness message or an optimal solution.

Study smarter with the SolutionInn App