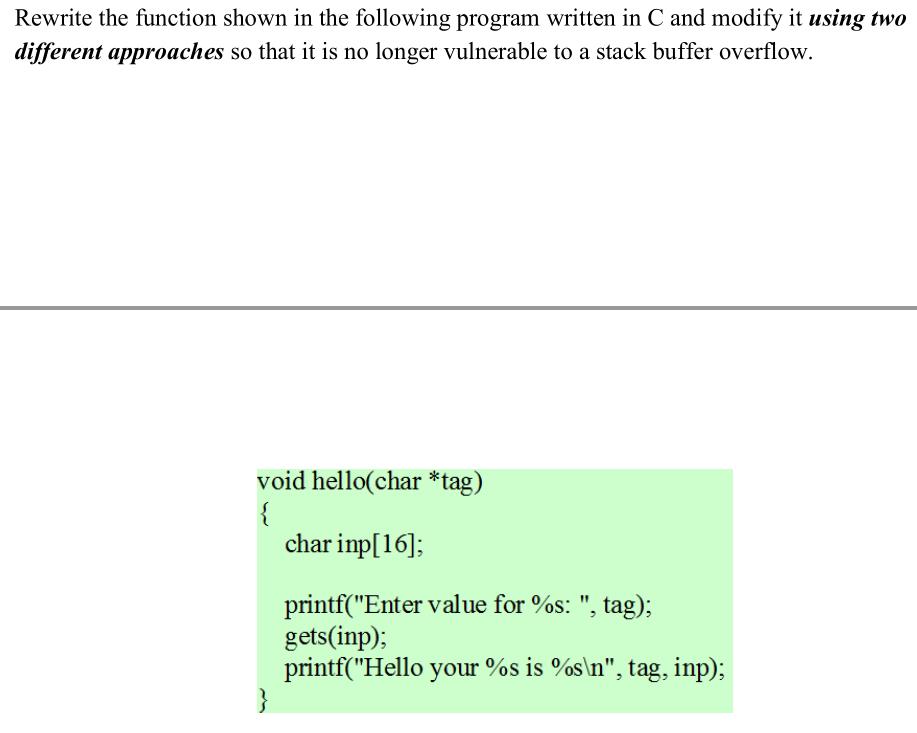
Rewrite the function shown in the following program written in C and modify it using two...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Rewrite the function shown in the following program written in C and modify it using two different approaches so that it is no longer vulnerable to a stack buffer overflow. void hello(char *tag) { char imp[16]; printf("Enter value for %s: ", tag); gets (inp); printf("Hello your %s is %s\n", tag, inp); Rewrite the function shown in the following program written in C and modify it using two different approaches so that it is no longer vulnerable to a stack buffer overflow. void hello(char *tag) { char imp[16]; printf("Enter value for %s: ", tag); gets (inp); printf("Hello your %s is %s\n", tag, inp);
Expert Answer:
Answer rating: 100% (QA)
The prompt asks to rewrite the function hello to prevent it from being vulnerable to a stack buffer overflow The gets function is dangerous because it takes a character array as input and continues re... View the full answer

Related Book For 

Operating Systems Internals and Design Principles
ISBN: 978-0133805918
8th edition
Authors: William Stallings
Posted Date:
Students also viewed these programming questions
-
123 Compare the purely graphical properties of these two notations, and the ways in which the graphical properties of each display correspond to the information structure being defined. Describe...
-
for the equality test for M and N. The question concerns how to represent multisets of strings within ML. For each of the given data representations (a), (b) and (c) describe how you would implement...
-
The average annual salary for all U.S. teachers is $47,750. Assume that the distribution is normal and the standard deviation is $5680. Find the probability that a randomly selected teacher earns a....
-
Agua Cool is a distributor of bottled water. For each of the items, compute the amount of cash receipts or payments Agua Cool will budget for September. The solution to one item may depend on the...
-
Leslie Company sells business stationery, imprinted with a customers business name and address. To do this, it purchased a printing machine costing $48,000 on January 1, 2001. The machine has an...
-
Veronicas expense report was reviewed by her company, and she was accused of taking her best friend on a business conference to Paris and charging all expenses for both of them on a company credit...
-
Rocky Mountain Interiors deposits all cash receipts each Wednesday and Friday in a night depository, after banking hours. The data required to reconcile the bank statement as of July 31 have been...
-
A student addresses a bully mocking another student, " what you're doing isn't even clever or funny, everyone has a right ti express who they are.. you know like we say every morning.. liberty and...
-
Find the holes, vertical asymptotes, horizontal asymptote, and slant asymptote of the following function, if they exist. f(x) = X = = 4x +4x-4x-4 x-x-2 If none exist, enter DNE. List vertical...
-
On November 15, 2023, Parkat Ltd., acquires control of Sparkat Ltd. Parkat and Sparkat are unrelated persons prior to the AOC. On November 14, 2023, Sparkat Ltd. owns the following properties: Land...
-
A baker's recipe for donuts yields 10 dozen donuts and it costs the baker $28.80 to produce the recipe. The raspberry filling the baker will use to fill the 10 dozen donuts costs the baker $7.13 to...
-
Blue Sky Mining Ltd has for several years provided houses for miners working at one of its remote mining sites in western Queensland. Following an inspection by government workplace health and safety...
-
Which one of the following would be an underwriter's first step in conducting a trend analysis on a set of financial statements? Available answer options Select only one option A Conducting vertical...
-
Cam is preparing a detailed report on the results of the firm's advertising campaign which ran during the year. The report will include information on the budget for the campaign, where it ran, and...
-
For each of the following annuities, calculate the annual cash flow: Note: Do not round intermediate calculations and round your answers to 2 decimal places, e.g., 32.16. Cash Flow Present Value...
-
a. What is meant by the term tax haven? b. What are the desired characteristics for a country if it expects to be used as a tax haven? c. What are the advantages leading an MNE to use a tax haven...
-
List three degrees of awareness between processes and briefly define each.
-
Table shows the process states for the VAX/VMS operating system. a. Can you provide a justification for the existence of so many distinct wait states? b. Why do the following states not have resident...
-
This diagram shows an example of memory configuration under dynamic partitioning, after a number of placement and swapping-out operations have been carried out. Addresses go from left to right; gray...
-
Assume you want to use random tests on an FIR filter program. How would you know when the program under test is executing correctly?
-
Three devices are attached to a microprocessor: Device 1 has highest priority and device 3 has lowest priority. Each devices interrupt handler takes 5 time units to execute. Show what interrupt...
-
Provide examples of how each of the following can occur in a typical program: a. compulsory miss b. capacity miss c. conflict miss
Basics Of Manufacturing Technology Conventional Machining 1st Edition - ISBN: B0B92QYY1P - Free Book

Study smarter with the SolutionInn App


