RSA cryptosystem is used to secure a shared key between two party A and B. the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
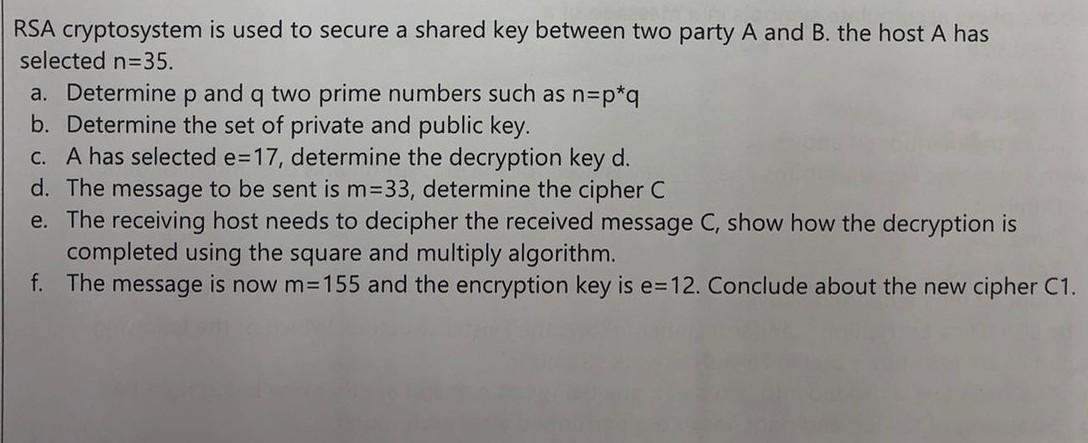
RSA cryptosystem is used to secure a shared key between two party A and B. the host A has selected n=35. a. Determine p and q two prime numbers such as n=p*q b. Determine the set of private and public key. c. A has selected e=17, determine the decryption key d. d. The message to be sent is m=33, determine the cipher C e. The receiving host needs to decipher the received message C, show how the decryption is completed using the square and multiply algorithm. f. The message is now m=155 and the encryption key is e=12. Conclude about the new cipher C1. RSA cryptosystem is used to secure a shared key between two party A and B. the host A has selected n=35. a. Determine p and q two prime numbers such as n=p*q b. Determine the set of private and public key. c. A has selected e=17, determine the decryption key d. d. The message to be sent is m=33, determine the cipher C e. The receiving host needs to decipher the received message C, show how the decryption is completed using the square and multiply algorithm. f. The message is now m=155 and the encryption key is e=12. Conclude about the new cipher C1.
Expert Answer:
Answer rating: 100% (QA)
Solution a To find p and q you need to factorize n into two prime numbers One way to do this is to try dividing n by small primes until you find one t... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Advertising plays a major role in the ______________ stage of the product life cycle, and_______________ plays a major role in the maturity stage.
-
Jessi Paulis started a consulting firm, Paulis Consulting Ltd., on May 1, 2017. The following transactions occurred during the month of May. May 1 Paulis invested £8,000 cash in the business in...
-
In addition to the information presented in Mini-Exercise 14.2, the selling price for each unit is $20. Based on past experience, ABC expects that 35% of a months sales will be collected in the month...
-
Imagine you are the CIO of a hospital in which almost no computer-based tools are used. One of the hospital's goals is to support health care professionals in their daily tasks by offering up-to-date...
-
Stromberg Company of Zwingle, Kansas, spreads herbicides and applies liquid fertilizer for local farmers. On May 31, 2012, the company??s Cash account per its general ledger showed a balance of...
-
An RC circuit is powered by an alternating voltage source oscillating with angular frequency 7.4 rad/s. It is connected in series to a 8.4 ohm resistor and a 5.8 CF capacitor. In degrees, what is the...
-
You are employed by McDowell and Partners, Chartered Accountants (M&P). A new client, Community Finance Corporation (CFC), approached M&P for assistance. Enviro Ltd. (Enviro) has asked CFC for a loan...
-
We have been gathering vital data from engineering students as part of a thorough investigation of the effect of 40-100 on people's success. We ask the following extremely objective questions in a...
-
A consumer s preferences for consumption across two time periods c 1 and c 2 can be represented by the utility function U ( C 1 , C 2 ) = C 1 ^ 0 . 7 C 2 ^ 0 . 3 . The consumer s endowment of...
-
QUESTION 2 Consider the sprinkler system shown below. The sprinkler is rotating at w = 2.5 rad/s in the direction shown but is accelerating at a = 0.5 rad/s. Focusing on Figure 2: (a) Find the...
-
6.9 [37] Derive the dynamic equations for the three-link manipulator with one prismatic joint shown in Fig. 3.9. Link 1 has an inertia tensor given by C I = Link 2 has point mass m located at the...
-
Write MATLAB code to generate and plot four different mathematical functions on the same graph within the range [4, 4//4, 4]. Plot these curves using different line styles, colors, and markers....
-
Screw engagement length is 4.7mm And I am applying 200Ncm torque on M4 screw from top and screwdriver length is 150 mm. Q1- how much torque will transfer on M4 standoff? M4 Screw material (STEEL...
-
Consider the following hypothesis. H0: average cost per stay in a large hospital is $6,200, and H1: average cost per stay is $5,600, to be tested at the 95 percent level of confidence. A sample of...
-
Identify Thank You mission, strategy and core competencies. Identify strategy changes that have taken place at Thank You since its founding in 2008. Your answer must in text references and must be...
-
(a) What is a governance framework? (b) Compare the focus of COSO with that of CobiT. (c) Compare the focus of CobiT with that of the ISO/IEC 27000 family of standards.
-
Why is cyber espionage so attractive?
-
(a) What have privacy protection laws forced companies to do? (b) What did they find when they did so? (c) What institutions are subject to the Gramm-Leach-Bliley Act? (d) What institutions are...
-
Prove: 'Bernoulli's equation is a restrictive form of energy equation'.
-
What are the assumption made for the establishment of Bernoulli's equation?
-
A pipe, through which water is flowing, has diameters \(30 \mathrm{~cm}\) and \(15 \mathrm{~cm}\) at crosssections 1 and 2 respectively. The discharge velocity of the pipe is \(40 \mathrm{~L} /...

Study smarter with the SolutionInn App


