Suppose we have an assembler/linker/loader for a new RISC-V CPU running a new (hypothetical) operating system...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
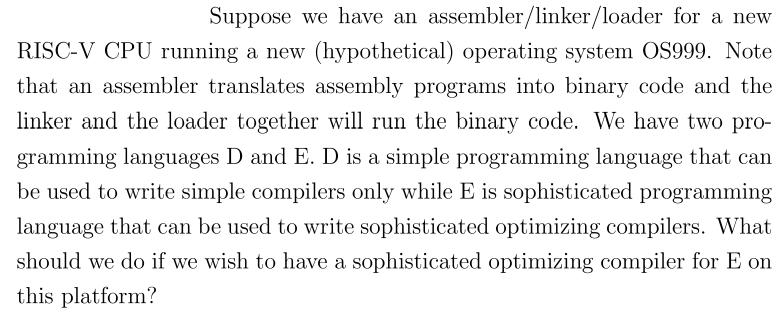
Suppose we have an assembler/linker/loader for a new RISC-V CPU running a new (hypothetical) operating system OS999. Note that an assembler translates assembly programs into binary code and the linker and the loader together will run the binary code. We have two pro- gramming languages D and E. D is a simple programming language that can be used to write simple compilers only while E is sophisticated programming language that can be used to write sophisticated optimizing compilers. What should we do if we wish to have a sophisticated optimizing compiler for E on this platform? Suppose we have an assembler/linker/loader for a new RISC-V CPU running a new (hypothetical) operating system OS999. Note that an assembler translates assembly programs into binary code and the linker and the loader together will run the binary code. We have two pro- gramming languages D and E. D is a simple programming language that can be used to write simple compilers only while E is sophisticated programming language that can be used to write sophisticated optimizing compilers. What should we do if we wish to have a sophisticated optimizing compiler for E on this platform?
Expert Answer:
Answer rating: 100% (QA)
To have a sophisticated optimizing compiler for the E programming language on the new RISCV CPU running the OS999 operating system you would need to follow a series of steps Here is a general guidelin... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
Costs incurred during March in the Blending Department were: materials used, $115,000; direct labor, $18,000; and overhead cost applied to production, $42,000. Required: 1. Prepare journal entries to...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
This case was written by Professor Michele Greenwald, Visiting Professor of Marketing at HEC Paris, for use with Advertising and Promotion: An Integrated Marketing Communications Perspective 7th...
-
Why are variances usually written off to cost of goods sold?
-
Assuming that a college graduate on average earns his or her MRP, what is the MRP for a newly hired Economics major?
-
Baldock Inc. is considering the acquisition of a new machine that costs $473,000 and has a useful life of 5 years with no salvage value . The incremental net operating income and incremental net cash...
-
How can a judgment creditor obtain funds in a judgment debtors bank account?
-
A monopolists inverse demand function is P = 100 Q. The company produces output at two facilities; the marginal cost of producing at facility 1 is MC1(Q1) = 4Q1, and the marginal cost of producing...
-
Part 1. Determine the function of the underlined asset in each of the following situations. (2 points each) 1. Shaira uses cash to buy school supplies for her son. 2. After having her dinner, Moira...
-
ABC Framing has been hired to frame a light commercial building. The project began on July 2 and was completed on August 9. The following is a list of accounting transactions associated with the...
-
Discuss the effect of the following identified risk on: Risk of Material Misstatement, Detection Risk, and the overall audit effort: Apollo's sales manual requires that orders greater than $10,000...
-
A fairly bland, but still interesting, retelling of Steve Jobss ascension from being a college dropout to one of the most influential and recognizable entrepreneurs of the twentieth century. Analyze...
-
What aspects contribute to or thwart acceptance of a newcomer into the group?
-
What are the advantages and disadvantages of various decision-making rules?
-
Have you ever experienced role reversal effects?
-
Are self-centered disruptive roles ever appropriate?
-
During February, Madison Company incurred an initial cost of $80,000. The company's overall production cost is 40% of its primary cost. In addition, the company spent $2,000 on wages paid to the...
-
The domain of the variable in the expression x 3/x + 4 is________.
-
I. Explain that cryptographic algorithms are often grouped into two broad categories: symmetric and asymmetric. II. Gain awareness that most cryptosystems often deploy a hybrid combination of...
-
True or False: Julius Caesar was associated with an early version of the substitution cipher.
-
True or False: The Center for Internet Security (CIS) outlines three categories of control to detect, prevent, respond to, and mitigate damage from attacks: Basic, Foundational, and Organizational.
-
A part of a mechanism which operates a horizontally sliding block \(E\) is shown in Fig.3.23(a). In the given configuration, the lever \(O B\) swings about \(O\) in the clockwise direction with an...
-
In the mechanism shown in Fig.3.21(a), the link \(O_{1} A\) rotates at \(24 \mathrm{rad} / \mathrm{s}\). Find the velocity and acceleration of point \(B\). \(O_{1} A=75 \mathrm{~mm}, A B=200...
-
A double slider-crank mechanism is shown in Fig.3.22(a). Crank 2 rotates at constant angular speed \(\omega_{2}=10 \mathrm{rad} / \mathrm{s}\). Determine the velocity and acceleration of each slider....

Study smarter with the SolutionInn App


