The following problems are about bit masks. 1. Masks and Shifts. 1.1 Write one C instruction...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
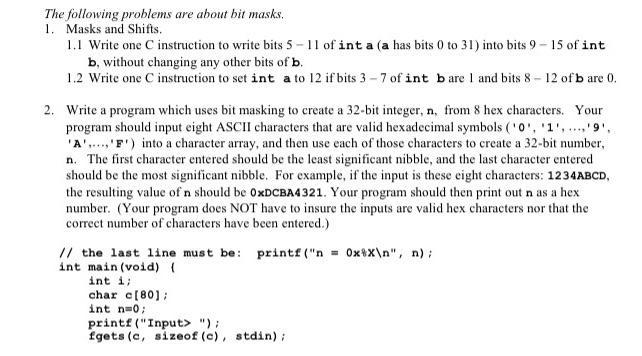
The following problems are about bit masks. 1. Masks and Shifts. 1.1 Write one C instruction to write bits 5-11 of int a (a has bits 0 to 31) into bits 9 - 15 of int b, without changing any other bits of b. 1.2 Write one C instruction to set int a to 12 if bits 3-7 of int bare 1 and bits 8-12 of b are 0. 2. Write a program which uses bit masking to create a 32-bit integer, n, from 8 hex characters. Your program should input eight ASCII characters that are valid hexadecimal symbols ('0', '1','9'. 'A'..., 'F') into a character array, and then use each of those characters to create a 32-bit number, n. The first character entered should be the least significant nibble, and the last character entered should be the most significant nibble. For example, if the input is these eight characters: 1234ABCD, the resulting value of n should be 0xDCBA4321. Your program should then print out n as a hex number. (Your program does NOT have to insure the inputs are valid hex characters nor that the correct number of characters have been entered.) // the last line must be: printf ("n=0xx\n", n); int main (void) { int i; char c[80]; int n=0; printf("Input> "); fgets (c, sizeof (c), stdin); The following problems are about bit masks. 1. Masks and Shifts. 1.1 Write one C instruction to write bits 5-11 of int a (a has bits 0 to 31) into bits 9-15 of int b, without changing any other bits of b. 1.2 Write one C instruction to set int a to 12 if bits 3-7 of int bare 1 and bits 8-12 of b are 0. 2. Write a program which uses bit masking to create a 32-bit integer, n, from 8 hex characters. Your program should input eight ASCII characters that are valid hexadecimal symbols ('0', '1','9'. 'A'..., 'F') into a character array, and then use each of those characters to create a 32-bit number, n. The first character entered should be the least significant nibble, and the last character entered should be the most significant nibble. For example, if the input is these eight characters: 1234ABCD, the resulting value of n should be 0xDCBA4321. Your program should then print out n as a hex number. (Your program does NOT have to insure the inputs are valid hex characters nor that the correct number of characters have been entered.) // the last line must be: printf ("n=0xx\n", n); int main (void) ( int i; char c[80]; int n=0; printf("Input> "); fgets (c, sizeof (c), stdin); The following problems are about bit masks. 1. Masks and Shifts. 1.1 Write one C instruction to write bits 5-11 of int a (a has bits 0 to 31) into bits 9 - 15 of int b, without changing any other bits of b. 1.2 Write one C instruction to set int a to 12 if bits 3-7 of int bare 1 and bits 8-12 of b are 0. 2. Write a program which uses bit masking to create a 32-bit integer, n, from 8 hex characters. Your program should input eight ASCII characters that are valid hexadecimal symbols ('0', '1','9'. 'A'..., 'F') into a character array, and then use each of those characters to create a 32-bit number, n. The first character entered should be the least significant nibble, and the last character entered should be the most significant nibble. For example, if the input is these eight characters: 1234ABCD, the resulting value of n should be 0xDCBA4321. Your program should then print out n as a hex number. (Your program does NOT have to insure the inputs are valid hex characters nor that the correct number of characters have been entered.) // the last line must be: printf ("n=0xx\n", n); int main (void) { int i; char c[80]; int n=0; printf("Input> "); fgets (c, sizeof (c), stdin); The following problems are about bit masks. 1. Masks and Shifts. 1.1 Write one C instruction to write bits 5-11 of int a (a has bits 0 to 31) into bits 9-15 of int b, without changing any other bits of b. 1.2 Write one C instruction to set int a to 12 if bits 3-7 of int bare 1 and bits 8-12 of b are 0. 2. Write a program which uses bit masking to create a 32-bit integer, n, from 8 hex characters. Your program should input eight ASCII characters that are valid hexadecimal symbols ('0', '1','9'. 'A'..., 'F') into a character array, and then use each of those characters to create a 32-bit number, n. The first character entered should be the least significant nibble, and the last character entered should be the most significant nibble. For example, if the input is these eight characters: 1234ABCD, the resulting value of n should be 0xDCBA4321. Your program should then print out n as a hex number. (Your program does NOT have to insure the inputs are valid hex characters nor that the correct number of characters have been entered.) // the last line must be: printf ("n=0xx\n", n); int main (void) ( int i; char c[80]; int n=0; printf("Input> "); fgets (c, sizeof (c), stdin);
Expert Answer:
Answer rating: 100% (QA)
Explanation 11 To write bits 511 of a into bits 915 of b without changing any other bits of b we can use bitwise operations like this b b 0x7F 9 a 0x7F 9 Heres how it works step by step 0x7F is a bina... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
The following problems are about the steady state response of LTI systems due to periodic signals. (a) The transfer function of a LTI system is If the input to this system is x(t) = 1 + cos(t +...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Hydrocarbon A has the formula C 9 H 12 and absorbs 3 equivalents of H 2 to yield R, C 9 H 18 , when hydrogenated over a Pd/C catalyst. On treatment of A with aqueous H 2 SO 4 in the presence of...
-
Ethical Dilemma: Suppose you are president of West Turner Bank (WTB). WTB made loans for major construction projects in countries in Eastern Europe and North Africa. However, WTB's fortunes declined...
-
Locate the centroidal (x and ) of the beam's cross-sectional area, and then determine the product of inertia of this area with respect to the centroidal x' and y' axes. 300 mm y 10 mm 100 mm- 10 mm C...
-
The following selected accounts and balances appear on the adjusted trial balance for Ray Service, Inc., on December 31, 2010: 1. What is the net income or net loss? 2. What is the change in Retained...
-
Mathis Company and Reece Company use the perpetual inventory system. The following transactions occurred during the month of April: a. On April 1, Mathis Company purchased merchandise on account from...
-
Let f ( x , y , z ) = y x / z . Find the value of the following partial derivatives. ( a ) fx ( 4 , 3 , 4 ) ( b ) fy ( 3 , 2 , 3 ) ( c ) fz ( 3 , 2 , 3 )
-
A. Richard McCarthy (born 2/14/64; Social Security number 100-10-9090) and Christine McCarthy (born 6/1/1966; Social security number 101-21-3434) have a 19-year-old son (born 10/2/99 Social Security...
-
You are the controller of ABC Limited (ABCL) and are in the process of determining the value of several items to prepare the year-end financial statements. The company follows IFRS. The items are...
-
Provide summary, conclusion, facts and judgement of judge on this case. Captains and chiefs association v Algoma Central Marine, 2010 CIRB 531
-
Q) Referring to your property legislation, both Act and Regulations, what is addressed regarding trust accounting? Record these 10 items under the correct Act or Regulation. 1 Keep trust books of...
-
Clonex Labs, Incorporated, uses the weighted-average method of process costing. The following data are available for one department for October: Work in process, October 1 Work in process, October 31...
-
Baby Warehouse is a retail baby goods business located in far north QLD . Following a cyclone, its main retail premise in Cairns was damaged. The cyclone caused substantial damage to the roof and car...
-
The following data were extracted from the accounting records of Dana Designs on March 3 1 , the end of Dana s fiscal year: Line Item Description Amount Inventory, April 1 $ 5 3 0 , 0 0 0 Inventory,...
-
Identify the terms, the degree of each term and the degree of the polynomial. Then identify the leading term, the leading coefficient, and the constant term. 6v^(9)+10v^(10)p^(8)+4v^(4)p^(4)+4v^(4)-8
-
Reread the discussion leading to the result given in (7). Does the matrix sI - A always have an inverse? Discuss.
-
The transfer function of an IIR filter is (a) Calculate the impulse response h[n]of the filter. (b) Would it be possible for this filter to have linear phase? Explain. (c) Sketch the magnitude...
-
Consider the following problems related to filtering of periodic signals: (a) A periodic signal x(t)of fundamental frequency Ω 0 = Ï/4 is the input of an ideal band-pass filter with...
-
An LTI discrete time system has the impulse response h[n] = (1) n u[n]. Use the convolution sum to compute the output response y[n],n 0, when the input is x[n] = u[n] u[n 3] and the initial...
-
In your year-end audit of The Joshua Redman Co., a defense contractor specializing in building sophisticated tracking systerns for missile defense systems, you bring in a specialist, Mal Waldron, to...
-
Specialists may be required to perform audit tasks that require knowledge or skills outside the auditor's abilities. Examples from the text include an engineer (to verify the stage of completion of...
-
Consider the internal audit staffs of the following two companies: Carl Company's internal auditors are college graduates who have been hired mostly from the ranks of marketing personnel who did not...

Study smarter with the SolutionInn App